Contents
Atlassian Cloud SSO (Single Sign-On) for Google apps using OAuth Provider
Jira OAuth Single-Sign On(SSO) for Atlassian Cloud allows you to use a single set of login credentials for secure access using miniOrange SSO solution. Single Sign-on (SSO) into your Atlassian Access or Atlassian Jira Cloud Account with any of your existing OAuth Provider credentials for enhanced security using our module.
You can refer the steps to configure Multiple IDPs and Domain Mapping in Atlassian Access from the video or documentation given below
Pre-requisites
1. Atlassian Access Subscription
Atlassian Access is an additional subscription applied across the Atlassian cloud products like Jira Software, Jira Service Management, Jira Work Management, Confluence, Bitbucket, etc. So it is needed for Single Sign-On(SSO) or any Cloud Service which comes under Atlassian Access.
2. Domain Verification:
The first step of Atlassian Access starts with the Domain Verification Process to enforce SAML SSO on the managed user accounts. This process verifies that you own a valid domain for managing the user accounts and use the same domain name for the email addresses.
In this document, we will demonstrate the setup in two parts.
Part 1: Configure SAML SSO between Atlassian cloud as SP and miniOrange as IDP
Part 2: Configure SAML SSO between miniOrange as SP and Google Apps as IDP
Part 1 + Part 2 : Testing SSO between Atlassian cloud as SP and Google Apps as IDP using miniOrange Identity Broker.
Part 1: Setup miniOrange with Atlassian Access
Step 1. Setup miniOrange as an Identity Provider
- Login into miniOrange Admin Console.
- Go to Apps and click on the Add Application button.
- In Choose Application Type click on Create App button in SAML/WS-FED application type.
- Search for Atlassian Cloud (SAML) in the list.
- Enter the following values in the respective fields, you will receive these values after creating an app in Atlassian access. Refer this step.
-
Custom Application Name Any name would be fine SP Entity ID or Issuer You will receive after configuring Atlassian Access App ACS URL You will receive after configuring Atlassian Access App - Also make sure that Sign Response & Sign Assertion both options are turned ON. Then click on the Save button.
- Once the App is successfully Created, Select that App and then click on Metadata option to get app’s Metadata.
- Since we are using miniOrange as a Brokering Service in this solution, Go to Information required to authenticate via external idp section as highlighted, and Click on Show Metadata Details.
- After clicking on the Show Metadata Details button you can see the metadata details.
- In the left sidebar hover on Users then click on Users List
- Click on Add User and enter details to enforce Single Sign On(SSO) on that user.








Step 2. Setup Atlassian Cloud
- Now login to Atlassian Cloud Admin Console.
- Select your organization and then select the Security tab. Click on SAML Single Sign-On from the left sidebar.
- You can click on Instructions for different Identity Providers. It provides a help page for specific IDP and Attribute Names for Attribute Mapping.
- Here you will get the SAML Configuration Instructions for different identity providers as listed. Click on Got it.
- Click on Add SAML Configuration.
- You will be redirected to the Add SAML Configuration window. Enter IDP Entity ID, SSO URL and the public certificate. Click on the Save Configuration button.
- Now you will be shown SP Entity ID & SP ACS URL as shown below. These details will be needed in miniOrange app configuration. Now set up the Authentication Policies by clicking on the View Authentication Policies.
- Click on Add Policy.
- Enter the policy name and add the policy.
- Now under Single Sign-On, click on Enable Single Sign-On.
- Then click on the Members tab besides the settings tab and click on Add Members.
- Enter details and click on Add Members.










Step 3. Test Atlassian Cloud - miniOrange Configuration
- Go to Atlassian Login Page.
- Enter email and click on Continue. Then you will be redirected to miniOrange Login Page
- After logging into miniOrange, you will be successfully logged into Atlassian Cloud Dashboard
If you do not have any IDP, you can always go with miniOrange IDP.
Part 2: Setup miniOrange with Google Apps
Step 1. Setup Google Apps as IDP
- Login to Google Console:Visit the Google's Developer Console and login to your account.
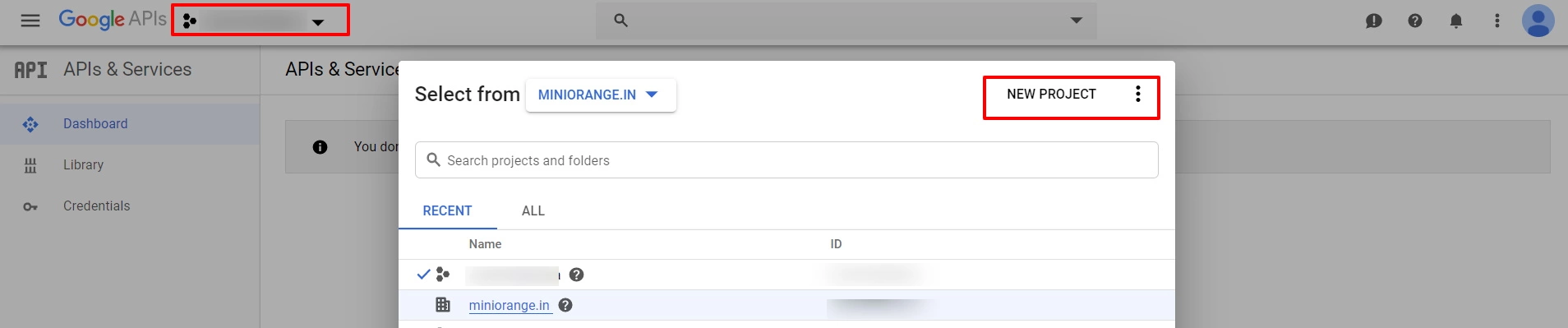
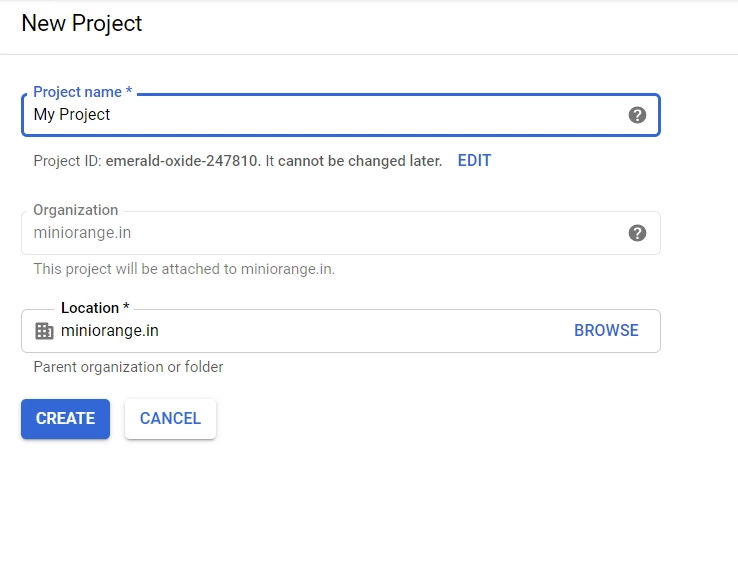
- Click Select a project, then NEW PROJECT, and enter a name for the project, and optionally, edit the provided project ID. Then click on Create button.
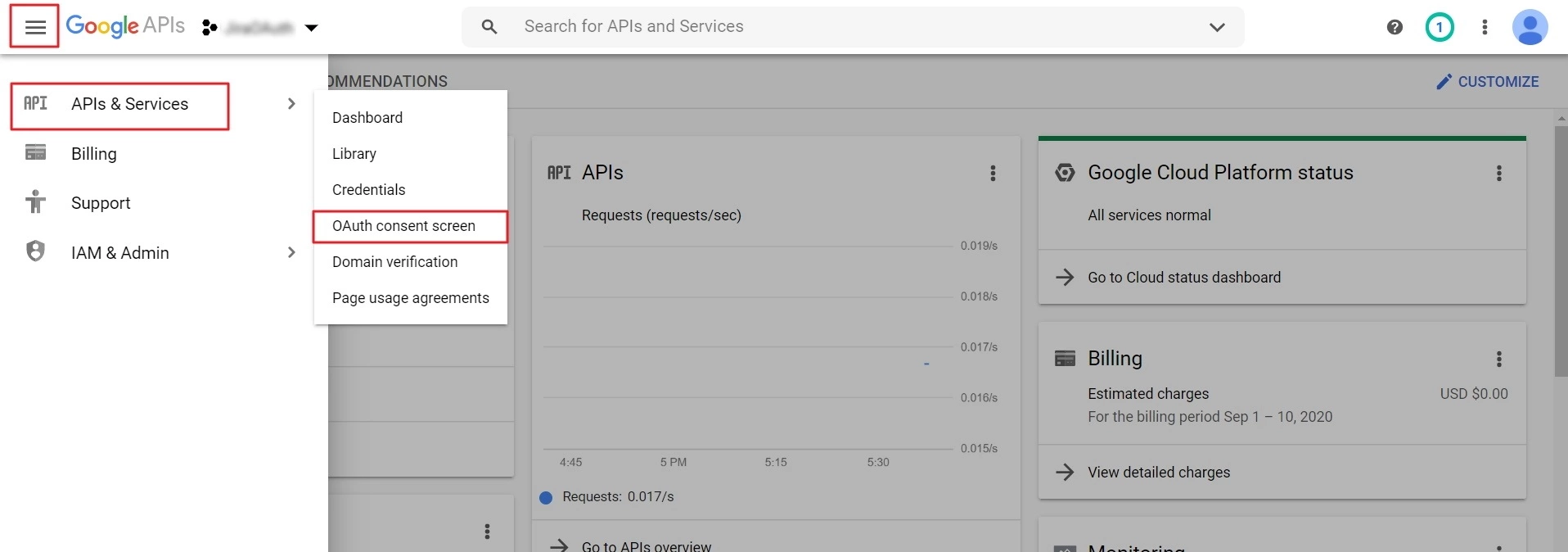
- Select your project, click on APIs & Services and select OAuth consent screen option.
- On the Consent screen page, select the User Type and click on Create. In the next screen, provide Application name and save the changes.
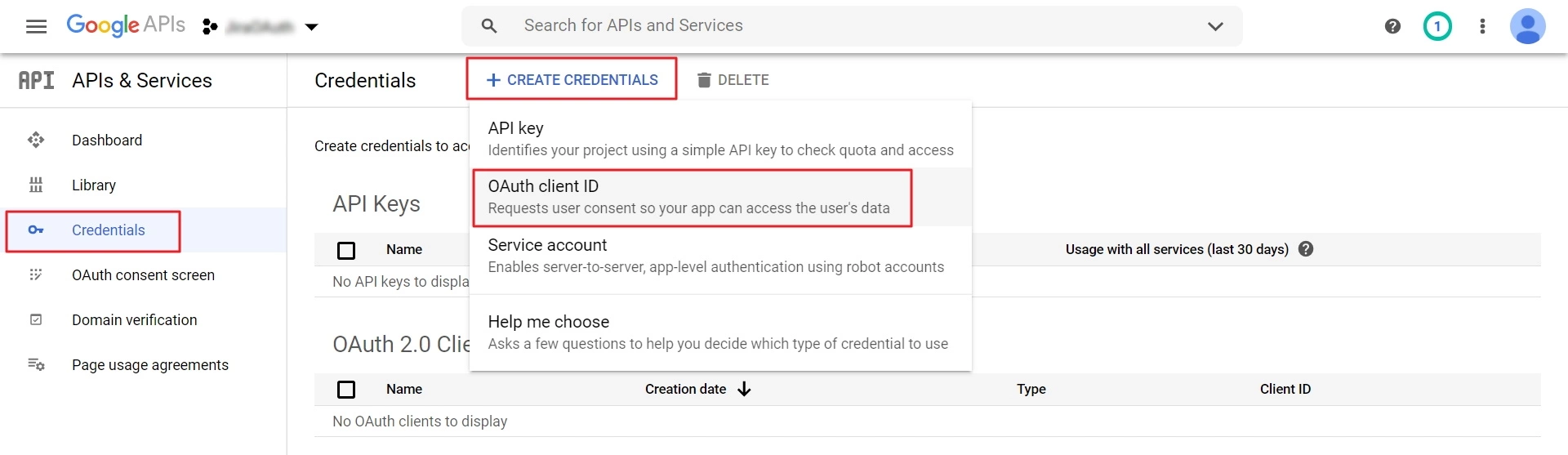
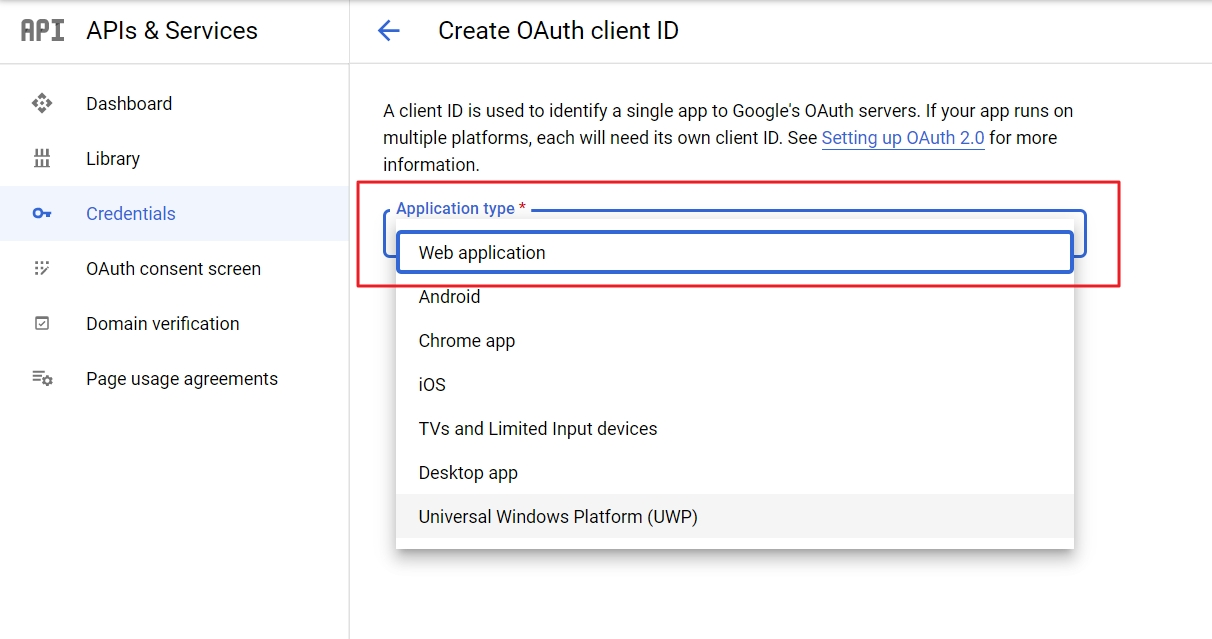
- Now go to Credentials, click on Create Credentials and select OAuth Client ID.
- Select Web Application as application type.
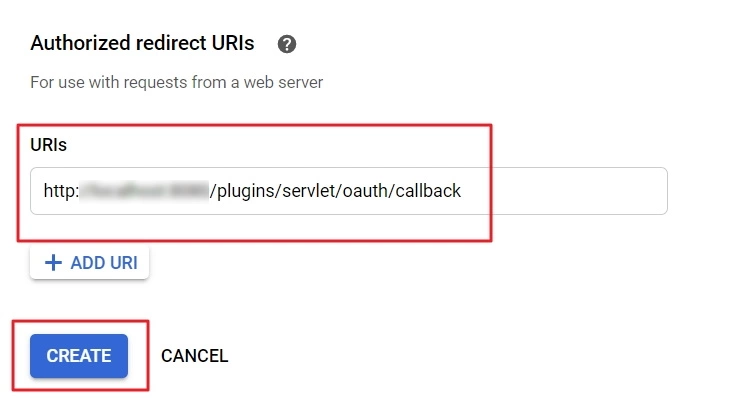
- Click on the Add URI button in Authorized redirect URIs section. Collect the callback URL provided in the miniOrange plugin and enter it here. Click on Create.
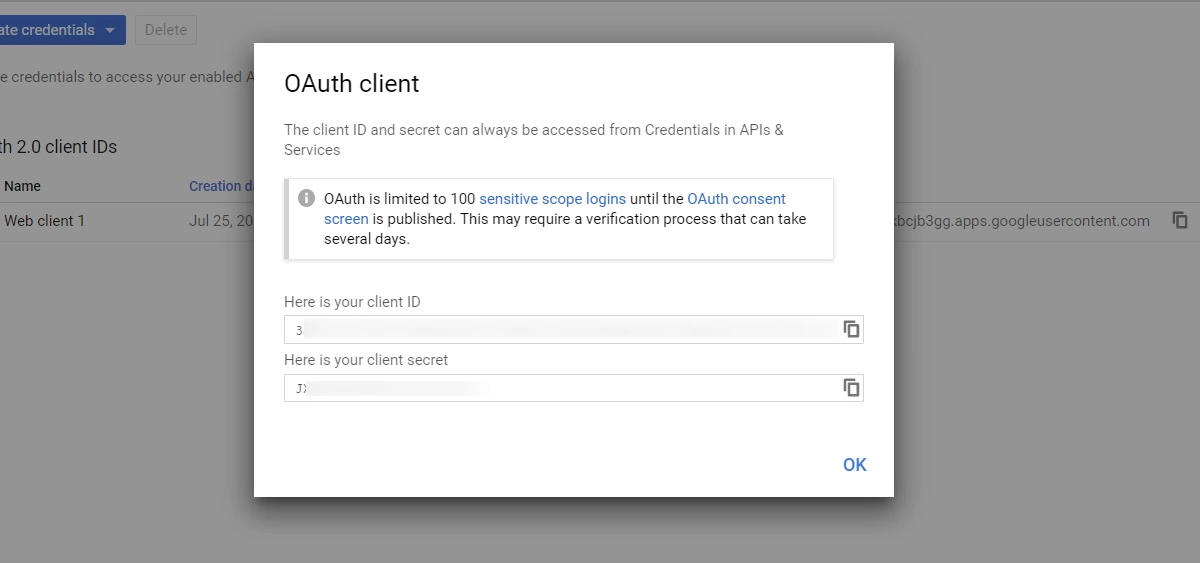
The callback URL would be {oauth_client_base_url}/plugins/servlet/oauth/callback - Get Client ID and Client Secret: Copy the client ID and client secret to your clipboard, as you will need them when you configure miniOrange plugin.
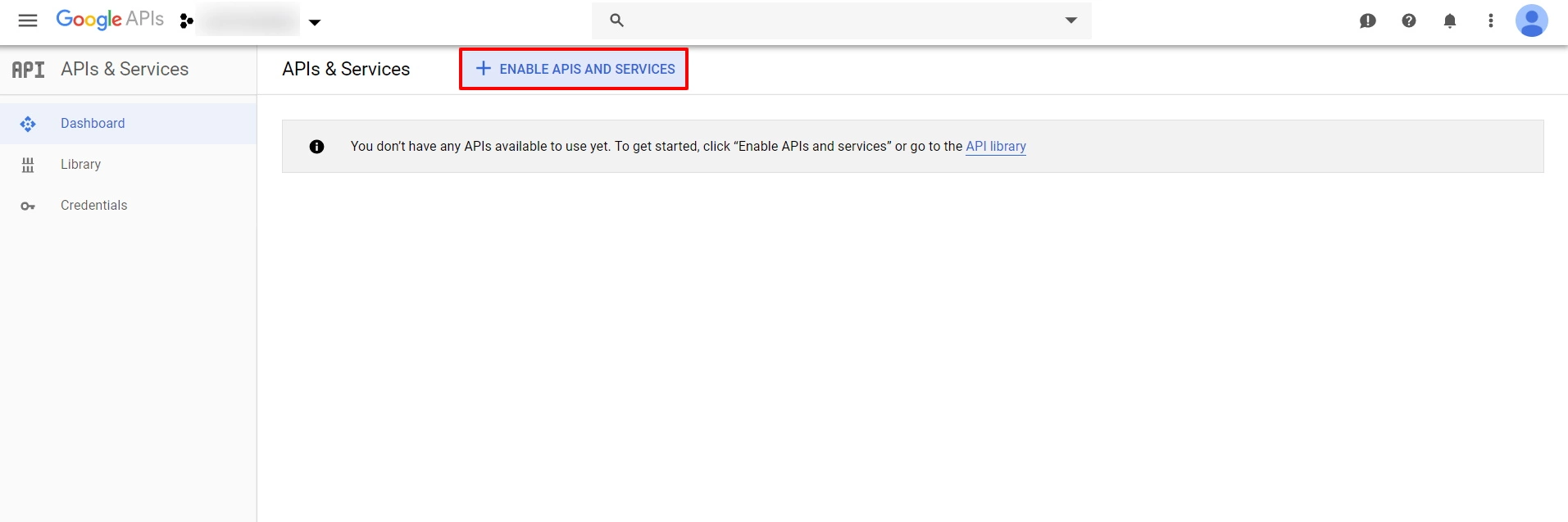
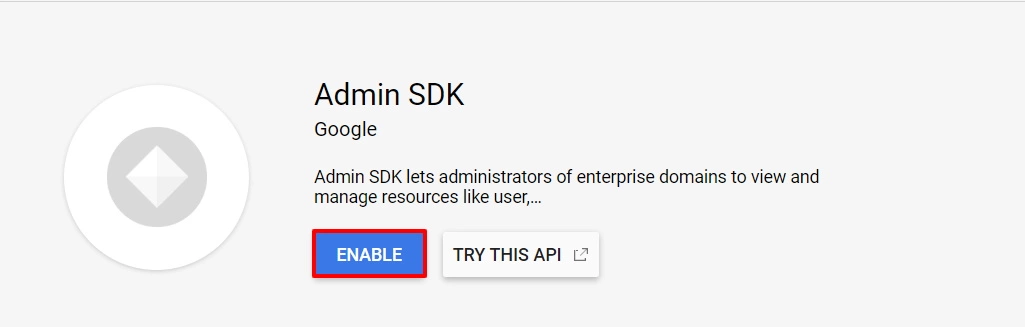
- To send user's group to the client application, you need to enable Admin SDK and API access. For Admin SDK, navigate to the Dashboard and click on ENABLE APIS AND SERVICES.
- Now search for Admin SDK, select it from the list and then click on ENABLE button.
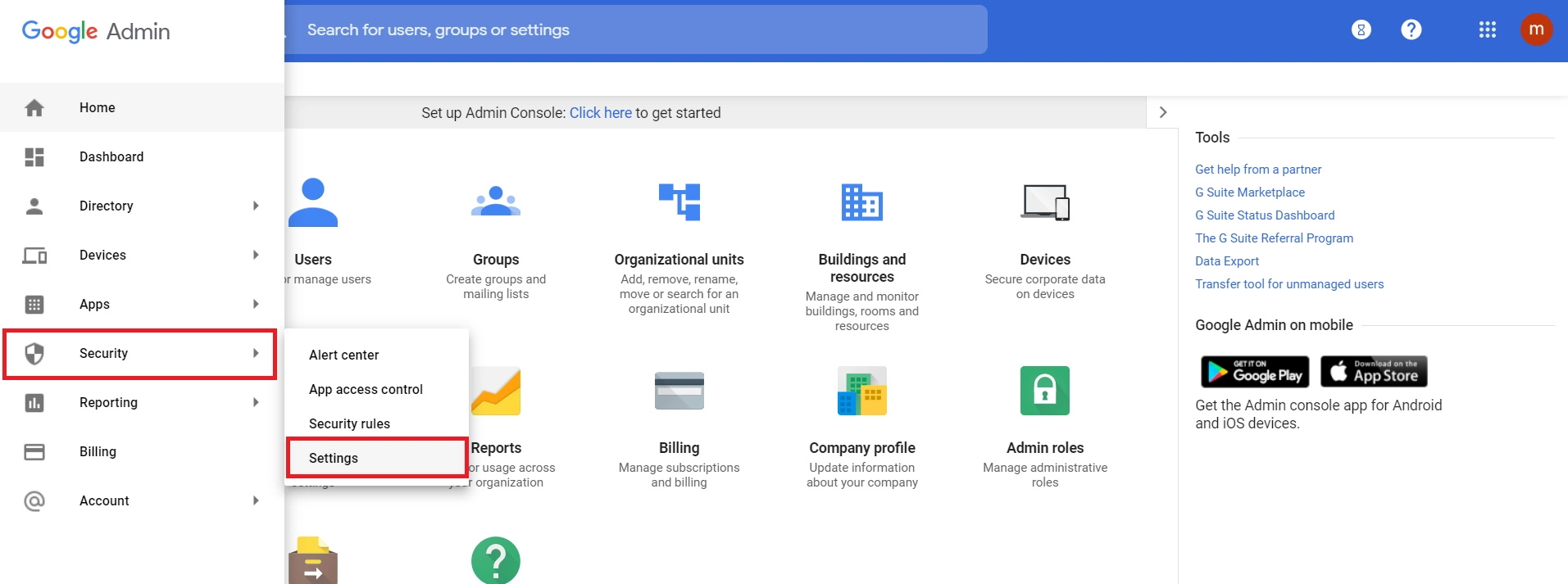
- To enable API Access you need to login into Google Admin console. In Google Admin Console, go to Security ->Settings.
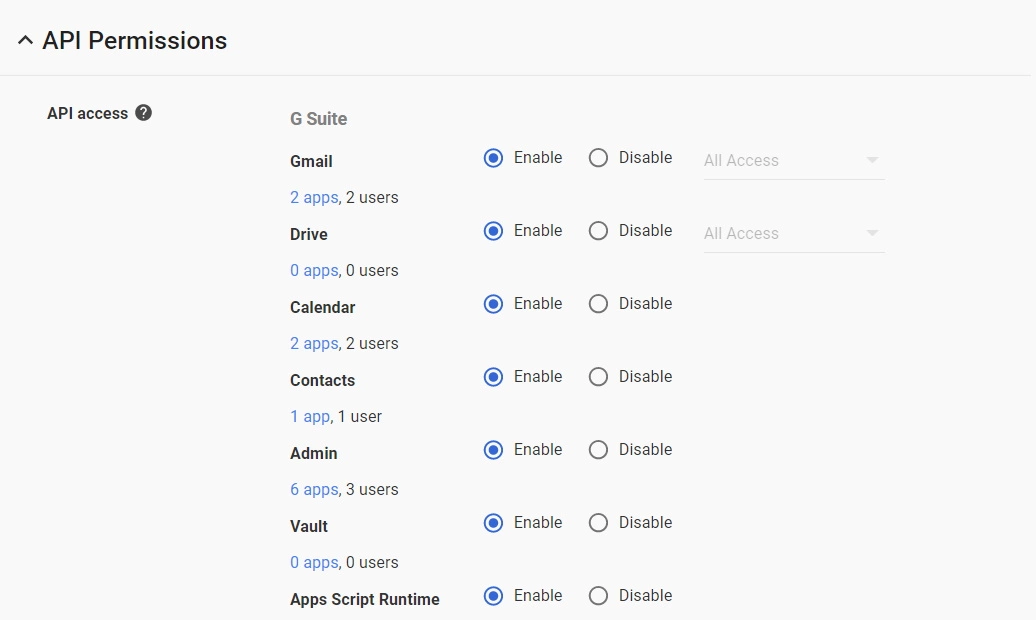
- Look for API Permissions -> Enable API access
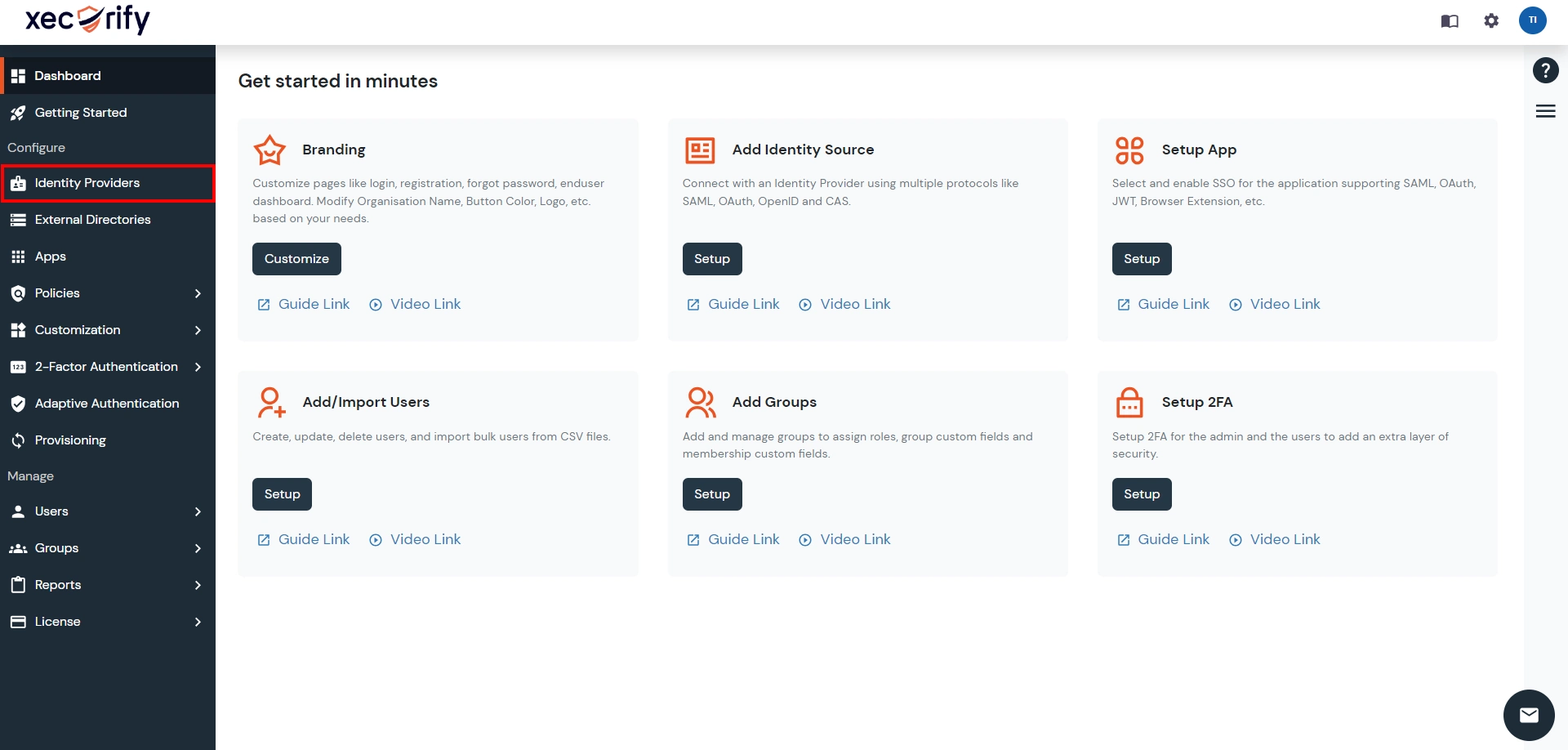
- Go to miniOrange Admin Console.
- From the left navigation bar select Identity Provider.
- Select OAuth tab.
- Enter the following values.
- Go to the miniOrange Admin Dashboard.
- Go to Identity Providers tab. Then click on select button under the app you just created. Then click on Test Connection.
- A new popup login window will open. Enter your credentials and login.
- Now you will see TEST SUCCESSFUL in a new popup window. If not, then check if you have missed any of the above step.
Step 2. Setup miniOrange as Service Provider
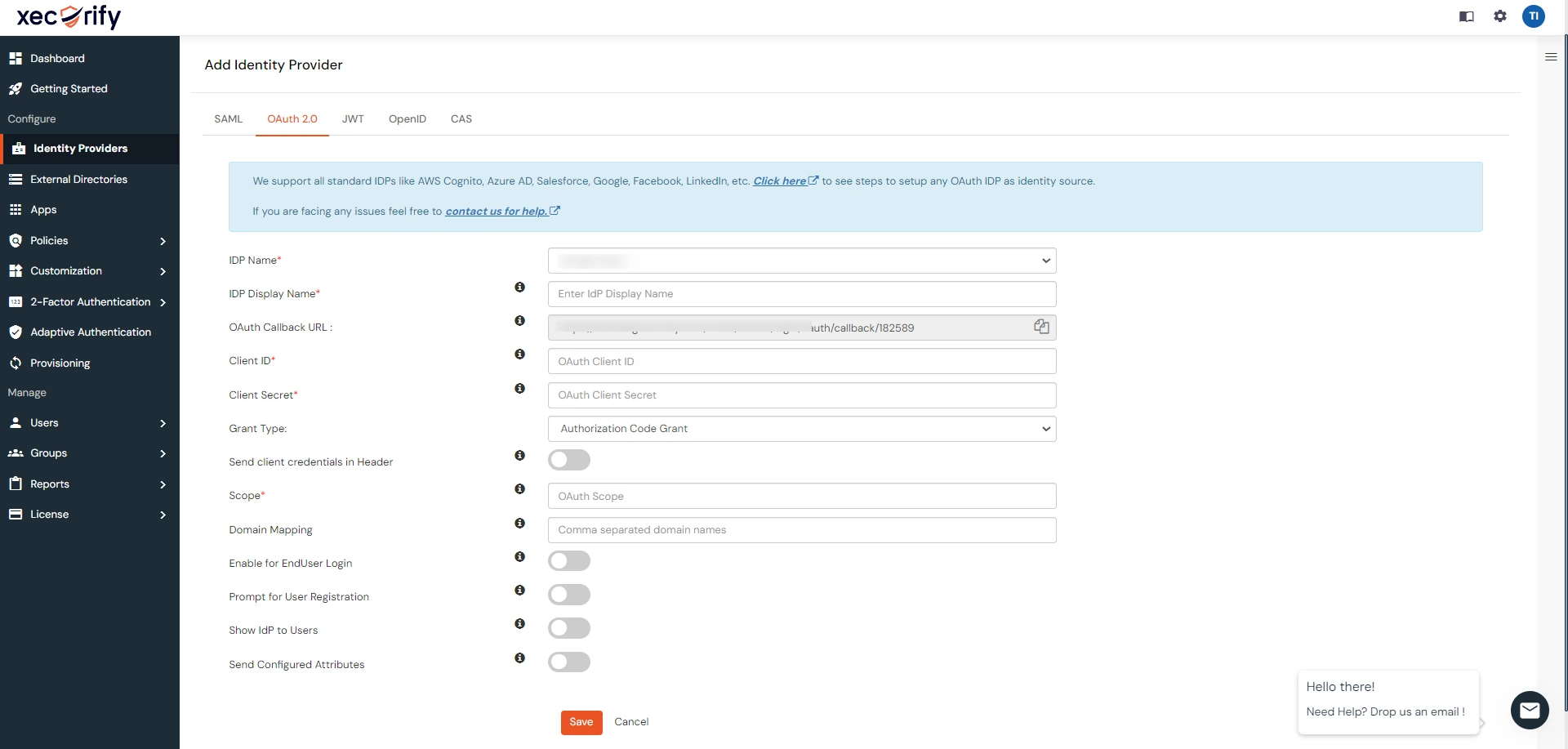
| IdP Name | Custom Provider |
| IdP Display Name | Choose appropriate Name |
| OAuth Authorize Endpoint | https://<wso2-app-domain>/oauth2/authorize | OAuth Access Token Endpoint | https://<wso2-app-domain>/oauth2/token | OAuth Get User Info Endpoint (optional) | https://<wso2-app-domain>/oauth2/userinfo |
| Client ID | From step 1 |
| Client secret | From step 1 |
| Scope | openid |
Step 3. Test connection between miniOrange and Google Apps

Part 3: Test Atlassian - Google Apps Configuration
- Go to Atlassian Login Portal.
- Enter email and click on Continue. Then you will be redirected to Google Apps Login Page.
- After logging into Google Apps Login Page, you will be successfully logged into Atlassian Cloud Dashboard.

Exclusive features other miniOrange cloud app provides
- Multiple Identity Providers(IDPs) to authenticate different types of users with different IDP.
- Multiple Department Based Login to force the users to authenticate via a specific IDP based on the users' department.
- Domain Mapping that allow users to redirect to their IDP based on their email departments.
- Custom Attribute Mapping to update the user profile attributes in the application with the user attributes received from the IdP.
- Signed Request and Response to secure your SSO with signed requests and encrypted SAML assertions.
- Username Transformation to extract the required username from the received attribute using Regular Expression.
- Group Mapping allows mapping user’s Identity Provider(IdP) groups to application groups. The user groups are updated on SSO.
- User Store to integrate your application with multiple user stores like AD, LDAP, external database, etc. to easily manage your users.
- Server to Cloud Migration to easily migrate your server SSO settings into Cloud.

