Contents
Atlassian Cloud SSO (Single Sign-On) for Shibboleth3 using SAML
You can refer the steps to configure Multiple IDPs and Domain Mapping in Atlassian Access from the video or documentation given below
Pre-requisites
1. Atlassian Access Subscription
Atlassian Access is an additional subscription applied across the Atlassian cloud products like Jira Software, Jira Service Management, Jira Work Management, Confluence, Bitbucket, etc. So it is needed for Single Sign-On(SSO) or any Cloud Service which comes under Atlassian Access.
2. Domain Verification:
The first step of Atlassian Access starts with the Domain Verification Process to enforce SAML SSO on the managed user accounts. This process verifies that you own a valid domain for managing the user accounts and use the same domain name for the email addresses.
In this document, we will demonstrate the setup in two parts.
Part 1: Configure SAML SSO between Atlassian cloud as SP and miniOrange as IDP
Part 2: Configure SAML SSO between miniOrange as SP and Shibboleth as IDP
Part 1 + Part 2 : Testing SSO between Atlassian cloud as SP and Shibboleth as IDP using miniOrange Identity Broker.
Part 1: Setup miniOrange with Atlassian Access
Step 1. Setup miniOrange as an Identity Provider
- Login into miniOrange Admin Console.
- Go to Apps and click on the Add Application button.
- In Choose Application Type click on Create App button in SAML/WS-FED application type.
- Search for Atlassian Cloud (SAML) in the list.
- Enter the following values in the respective fields, you will receive these values after creating an app in Atlassian access. Refer this step.
-
Custom Application Name Any name would be fine SP Entity ID or Issuer You will receive after configuring Atlassian Access App ACS URL You will receive after configuring Atlassian Access App - Also make sure that Sign Response & Sign Assertion both options are turned ON. Then click on the Save button.
- Once the App is successfully Created, Select that App and then click on Metadata option to get app’s Metadata.
- Since we are using miniOrange as a Brokering Service in this solution, Go to Information required to authenticate via external idp section as highlighted, and Click on Show Metadata Details.
- After clicking on the Show Metadata Details button you can see the metadata details.
- In the left sidebar hover on Users then click on Users List
- Click on Add User and enter details to enforce Single Sign On(SSO) on that user.








Step 2. Setup Atlassian Cloud
- Now login to Atlassian Cloud Admin Console.
- Select your organization and then select the Security tab. Click on SAML Single Sign-On from the left sidebar.
- You can click on Instructions for different Identity Providers. It provides a help page for specific IDP and Attribute Names for Attribute Mapping.
- Here you will get the SAML Configuration Instructions for different identity providers as listed. Click on Got it.
- Click on Add SAML Configuration.
- You will be redirected to the Add SAML Configuration window. Enter IDP Entity ID, SSO URL and the public certificate. Click on the Save Configuration button.
- Now you will be shown SP Entity ID & SP ACS URL as shown below. These details will be needed in miniOrange app configuration. Now set up the Authentication Policies by clicking on the View Authentication Policies.
- Click on Add Policy.
- Enter the policy name and add the policy.
- Now under Single Sign-On, click on Enable Single Sign-On.
- Then click on the Members tab besides the settings tab and click on Add Members.
- Enter details and click on Add Members.










Step 3. Test Atlassian Cloud - miniOrange Configuration
- Go to Atlassian Login Page.
- Enter email and click on Continue. Then you will be redirected to miniOrange Login Page
- After logging into miniOrange, you will be successfully logged into Atlassian Cloud Dashboard
If you do not have any IDP, you can always go with miniOrange IDP.
Part 2: Setup miniOrange with Shibboleth3
Step 1. Setup Shibboleth3 as IDP
- In conf/idp.properties, uncomment and set 'idp.encryption.optional' to
true.
eg. idp.encryption.optional = true - In conf/metadata-providers.xml, configure Service Provider like below.
- In conf/saml-nameid.properties, uncomment and set default NameID as Email Address like this
- In conf/saml-nameid-xml, search for shibboleth.SAML2NameIDGenerators. Uncomment the shibboleth.SAML2AttributeSourcedGenerator bean and comment all other ref beans.
- Make sure you have defined AttributeDefinition in conf/attribute-resolver.xml.
- Make sure you have AttributeFilterPolicy defined in conf/attribute-filter.xml.
- Restart the Shibboleth server.
- You need to configure these endpoints in the miniOrange SAML plugin.
<MetadataProvider xmlns:samlmd="urn:oasis:names:tc:SAML:2.0:metadata"
id="miniOrangeInLineEntity" xsi:type="InlineMetadataProvider" sortKey="1">
<samlmd:EntityDescriptor ID="entity" entityID="<SP-EntityID / Issuer from Service Provider Info tab in plugin.>"
validUntil="2020-09-06T04:13:32Z">
<samlmd:SPSSODescriptor AuthnRequestsSigned="false" WantAssertionsSigned="true"
protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol">
<samlmd:NameIDFormat>
urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
</samlmd:NameIDFormat>
<samlmd:AssertionConsumerService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
Location="<ACS (AssertionConsumerService) URL from Step1 of the plugin under Identity Provider Tab.>"
index="1" />
</samlmd:SPSSODescriptor>
</samlmd:EntityDescriptor>
</MetadataProvider>
idp.nameid.saml2.default=urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
<!-- SAML 2 NameID Generation -->
<util:list id="shibboleth.SAML2NameIDGenerators">
<!--<ref bean="shibboleth.SAML2TransientGenerator" /> -->
<!-->ref bean="shibboleth.SAML2PersistentGenerator" /> -->
<bean parent="shibboleth.SAML2AttributeSourcedGenerator"
p:format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress"
p:attributeSourceIds="#{ {'email'} }" />
</util:list>
<!-- Note: AttributeDefinitionid must be same as what you provided in attributeSourceIds in conf/saml-nameid.xml -->
<resolver:AttributeDefinitionxsi:type="ad:Simple" id="email" sourceAttributeID="mail">
<resolver:Dependency ref="ldapConnector" />
<resolver:AttributeEncoderxsi:type="enc:SAML2String" name="email" friendlyName="email" />
</resolver:AttributeDefinition >
<resolver:DataConnector id="ldapConnector" xsi:type="dc:LDAPDirectory" ldapURL="%{idp.authn.LDAP.ldapURL}"
baseDN="%{idp.authn.LDAP.baseDN}" principal="%{idp.authn.LDAP.bindDN}"
principalCredential="%{idp.authn.LDAP.bindDNCredential}">
<dc:FilterTemplate>
<!-- Define you User Search Filter here -->
<![CDATA[ (&(objectclass=*)(cn=$requestContext.principalName)) ]]>
</dc:FilterTemplate>
<dc:ReturnAttributes>*</dc:ReturnAttributes>
</resolver:DataConnector>
<afp:AttributeFilterPolicy id="ldapAttributes">
<afp:PolicyRequirementRulexsi:type="basic:ANY"/>
<afp:AttributeRuleattributeID="email">
<afp:PermitValueRulexsi:type="basic:ANY"/>
</afp:AttributeRule>
</afp:AttributeFilterPolicy>
| IDP Entity ID | https://<your_domain>/idp/shibboleth |
| Single Login URL | https://<your_domain>/idp/profile/SAML2/Redirect/SSO |
| Single Logout URL | https://<your_domain>/idp/shibboleth |
| X.509 Certificate | The public key certificate of your Shibboleth server |
Step 2. Setup miniOrange as Service Provider
- Go to miniOrange Admin Console.
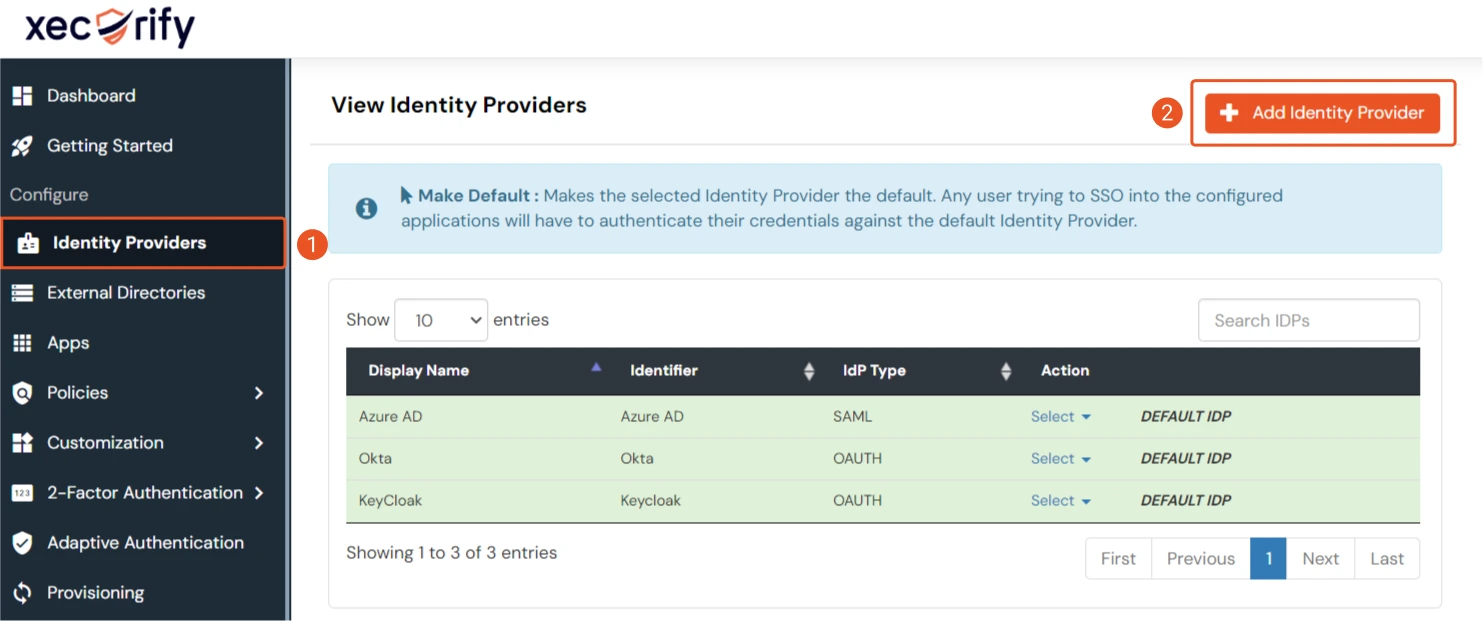
- From the left navigation bar select Identity Provider. Then click on Add Identity Provider
- Select SAML tab.
- Click on Show Metadata details under For SP - INITIATED SSO. You can either manually enter details or use Metadata URL or File
- Now to create SAML app for Shibboleth, go to the Add Identity Provider page and click on Import IDP Metadata. Import the metadata file that you will get from the SAML Login Information section of Shibboleth.
- If you don't have a metadata file, you can also provide the details manually. You need to configure following endpoints:
- Few other optional features that can be added to the Identity Provider(IDP) are listed in the table below:
- Click on Save.



| IDP Entity ID | Entity ID of IDP |
| Single Login URL | Login Url from IDP |
| Single Logout URL | Logout Url from IDP |
| X.509 Certificate | The public key certificate of your IDP. |
| Domain Mapping | Can be used to redirect specific domain user to specific IDP |
| Show IdP to Users | Enable this if you want to show this IDP to all users during Login |
| Send Configured Attributes | Enabling this would allow you to add attributes to be sent from IDP |
Step 3. Test connection between miniOrange and Shibboleth
- Go to the miniOrange Admin Dashboard.
- Go to Identity Providers tab. Then click on select button under the app you just created. Then click on Test Connection.
- A new popup login window will open. Enter your credentials and login.
- Now you will see TEST SUCCESSFUL in a new popup window. If not, then check if you have missed any of the above step.



