How to add an OAuth App
miniOrange supports Single Sign-on into your apps, to securely login for admins and users. miniOrange supports several different protocols for your applications, such as
SAML, WS-FED, OAuth, OIDC, JWT, RADIUS, etc. Using Single Sign-on, users can use one set of credentials to login to multiple applications. This improves security, as it reduces avenues for phishing attacks, and also improves access to your application.
OAuth (Open Authorization) is an open standard for token-based authentication and authorization. OAuth allows an end-user's account information to be used by third-party services, such as Facebook, without exposing the user's password. It acts as an intermediary on behalf of the end-user, providing the service with an access token that authorizes specific account information to be shared.
miniOrange provides a solution to perform single sign-on(SSO) for applications supporting OAuth protocol, like Salesforce, WordPress, Joomla, Atlassian, Azure AD, Reddit, Spotify, Paypal, WHMCS, Slack, Discord, etc.
Configure Single Sign-On (SSO) Settings for OAuth Apps:
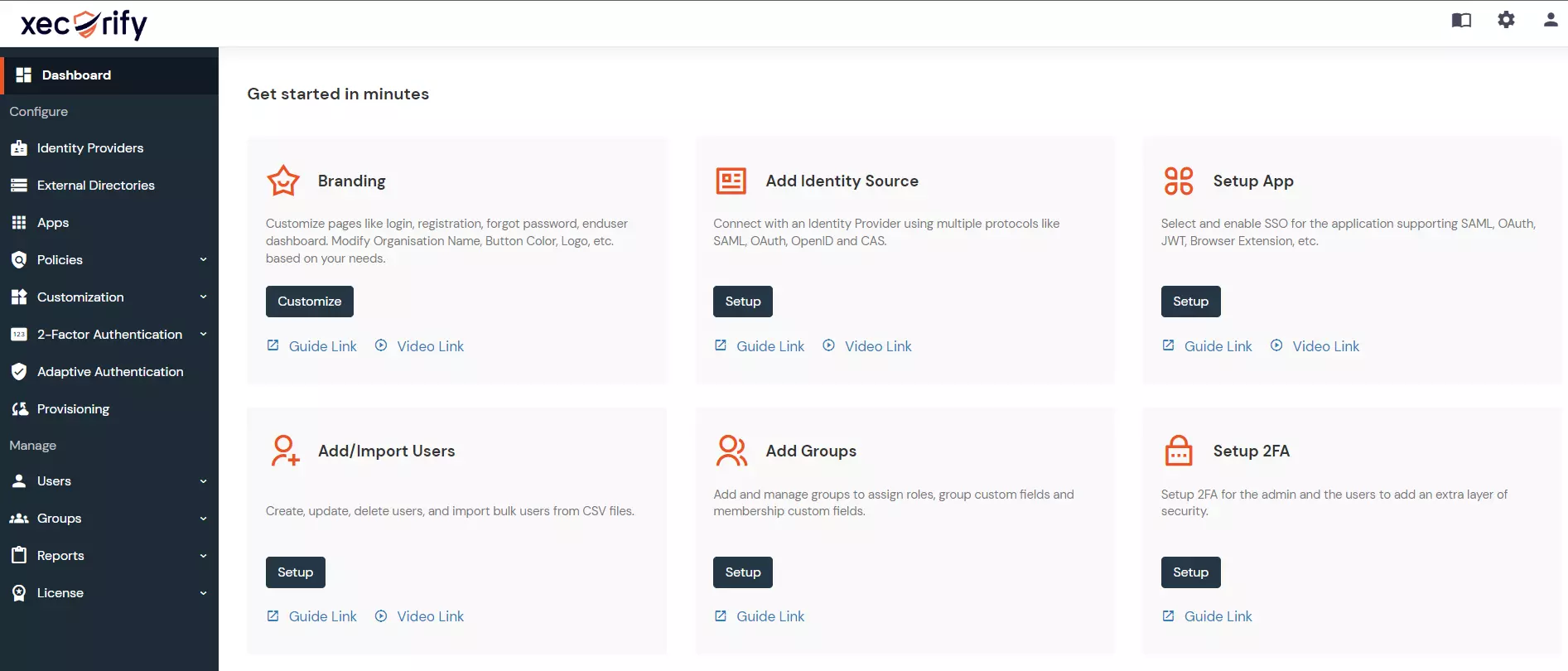
- Login into miniOrange Admin Console.
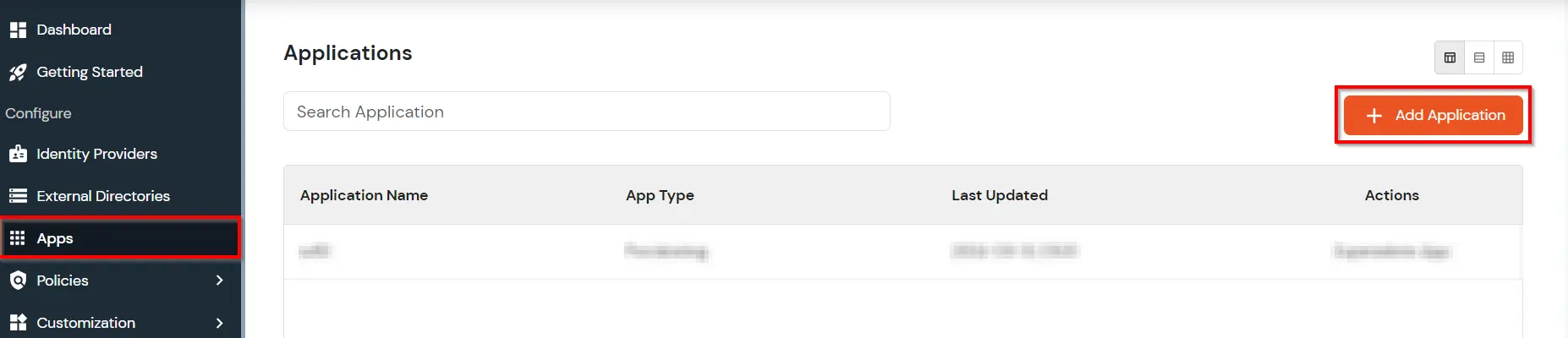
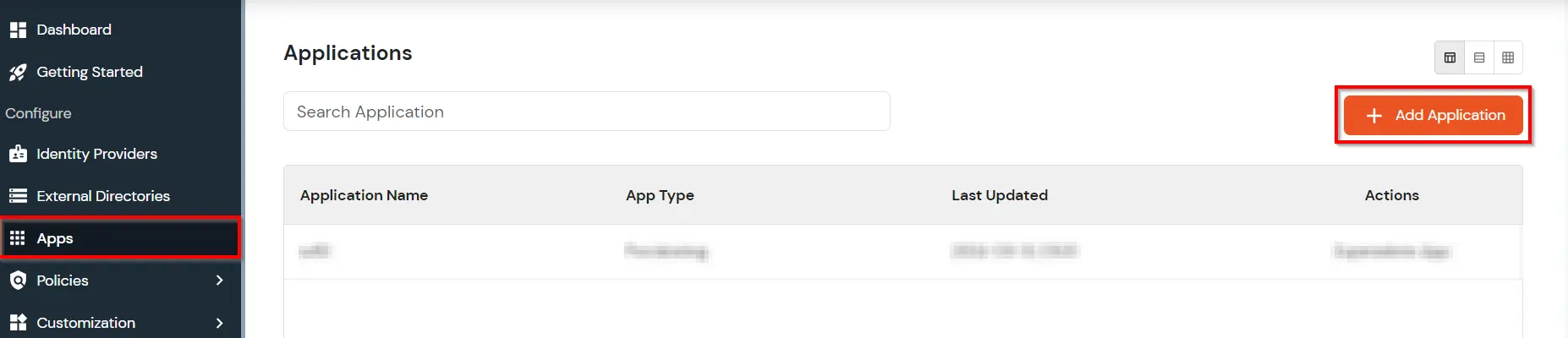
- Click on Apps. It shows a list of all configured applications and option to modify them. Click on Add Application.
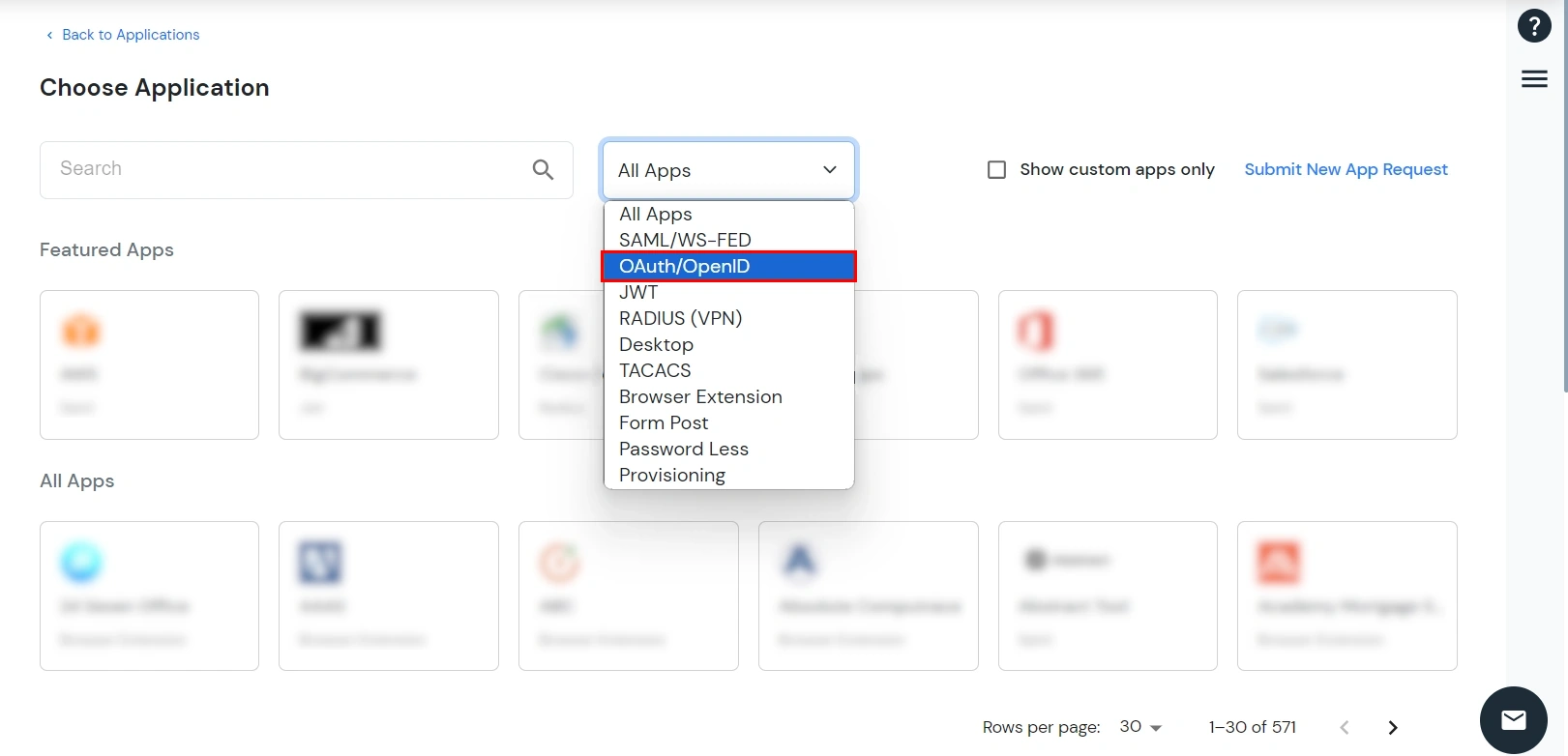
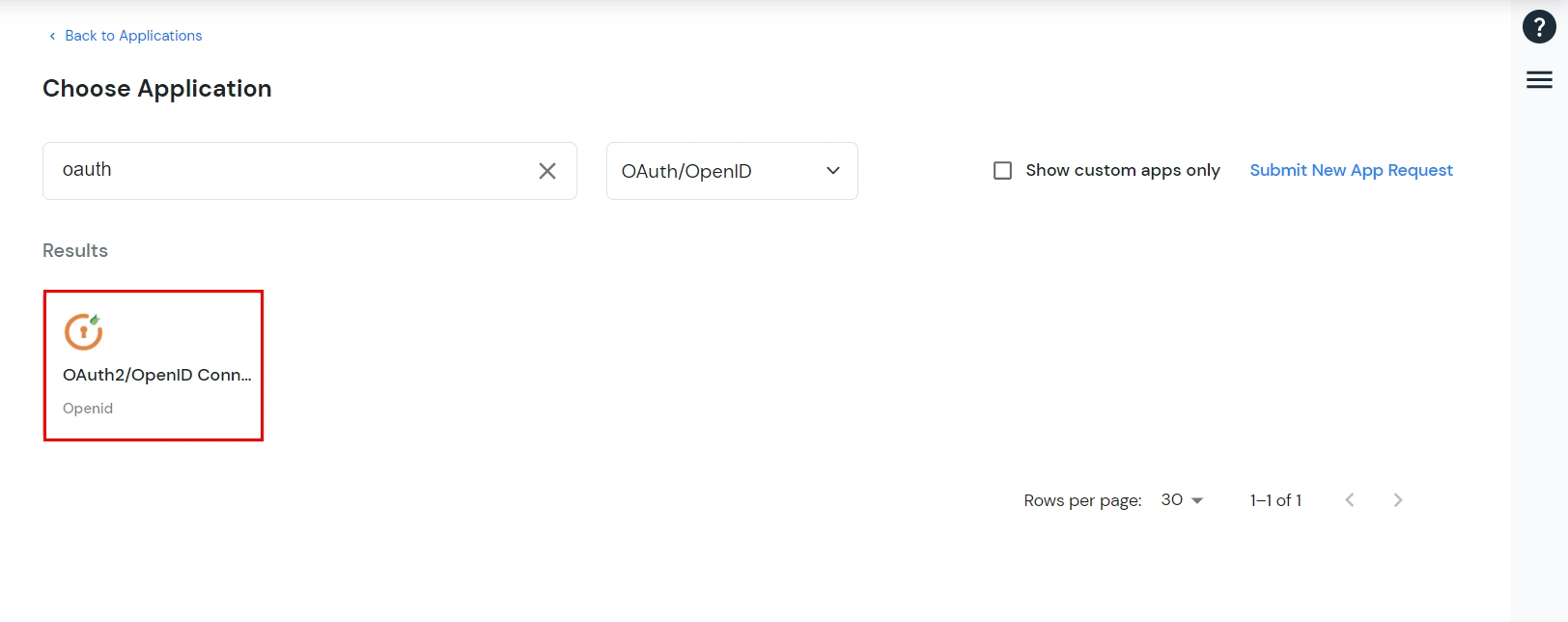
- Under Choose Application, select OAuth/OpenID from the All Apps dropdown.
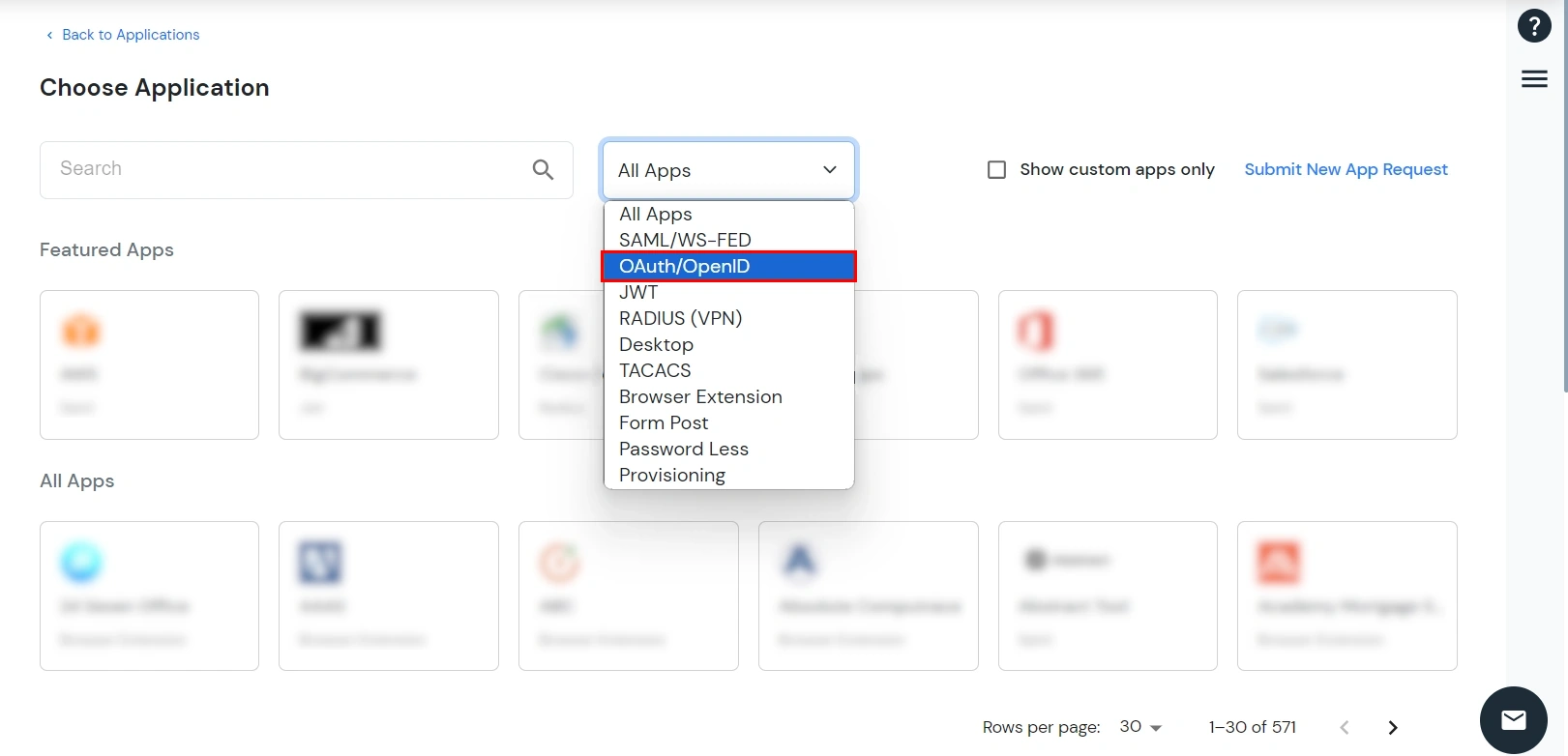
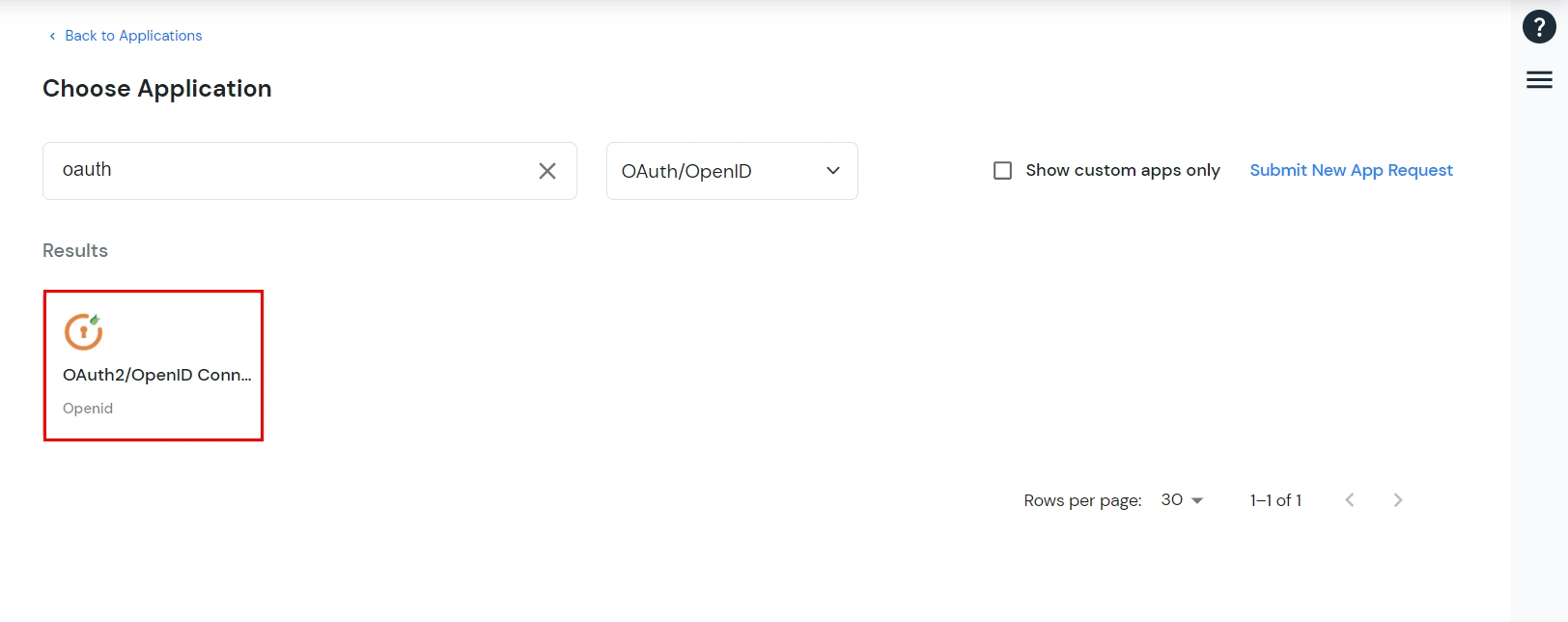
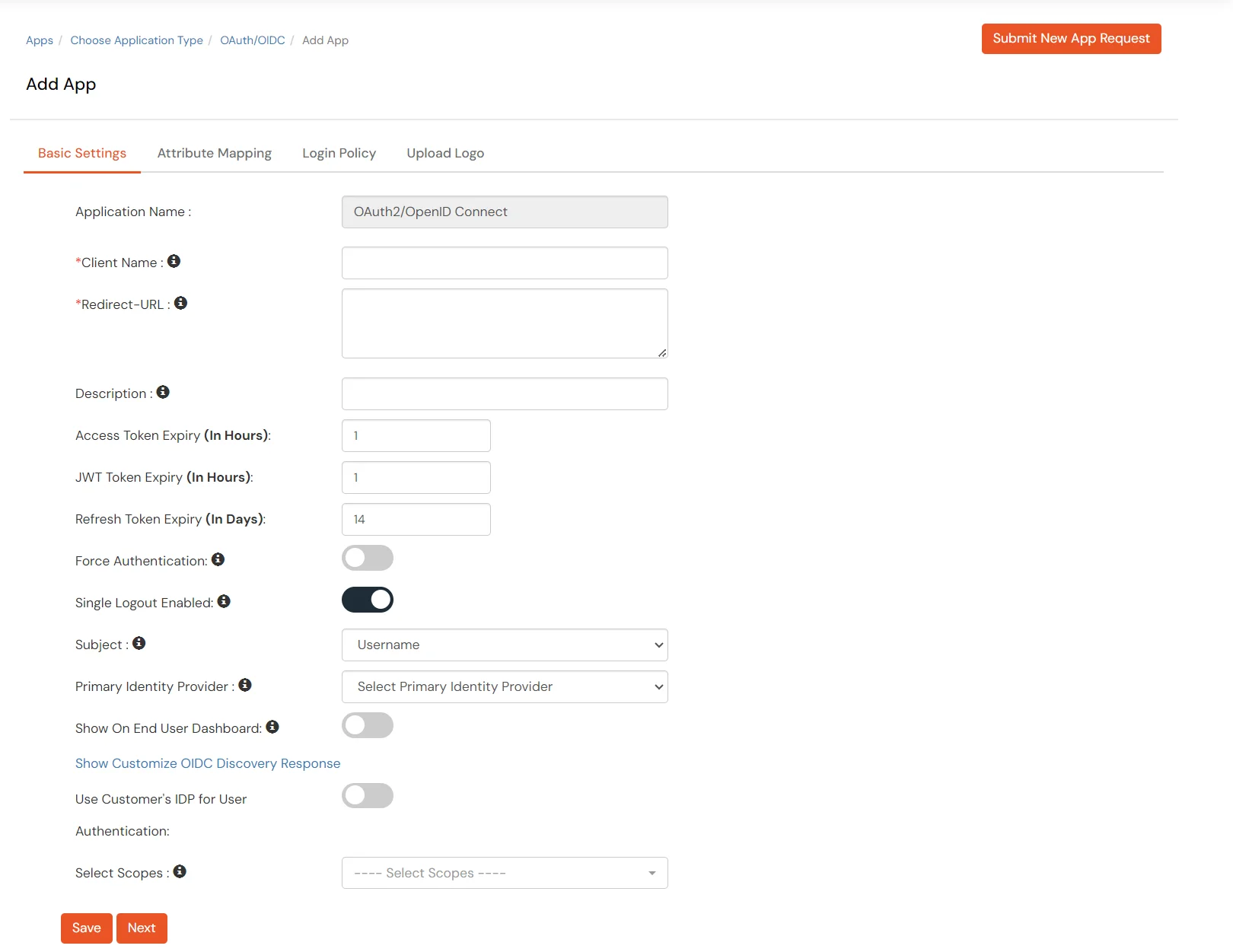
- Search for your application from the list, if your application is not found. Search for oauth and you can set up your app via OAuth2/OpenID Connect.
- Enter the Client Name. Make sure Redirect-URL is in this format
https://<mycompany.domain-name.com>
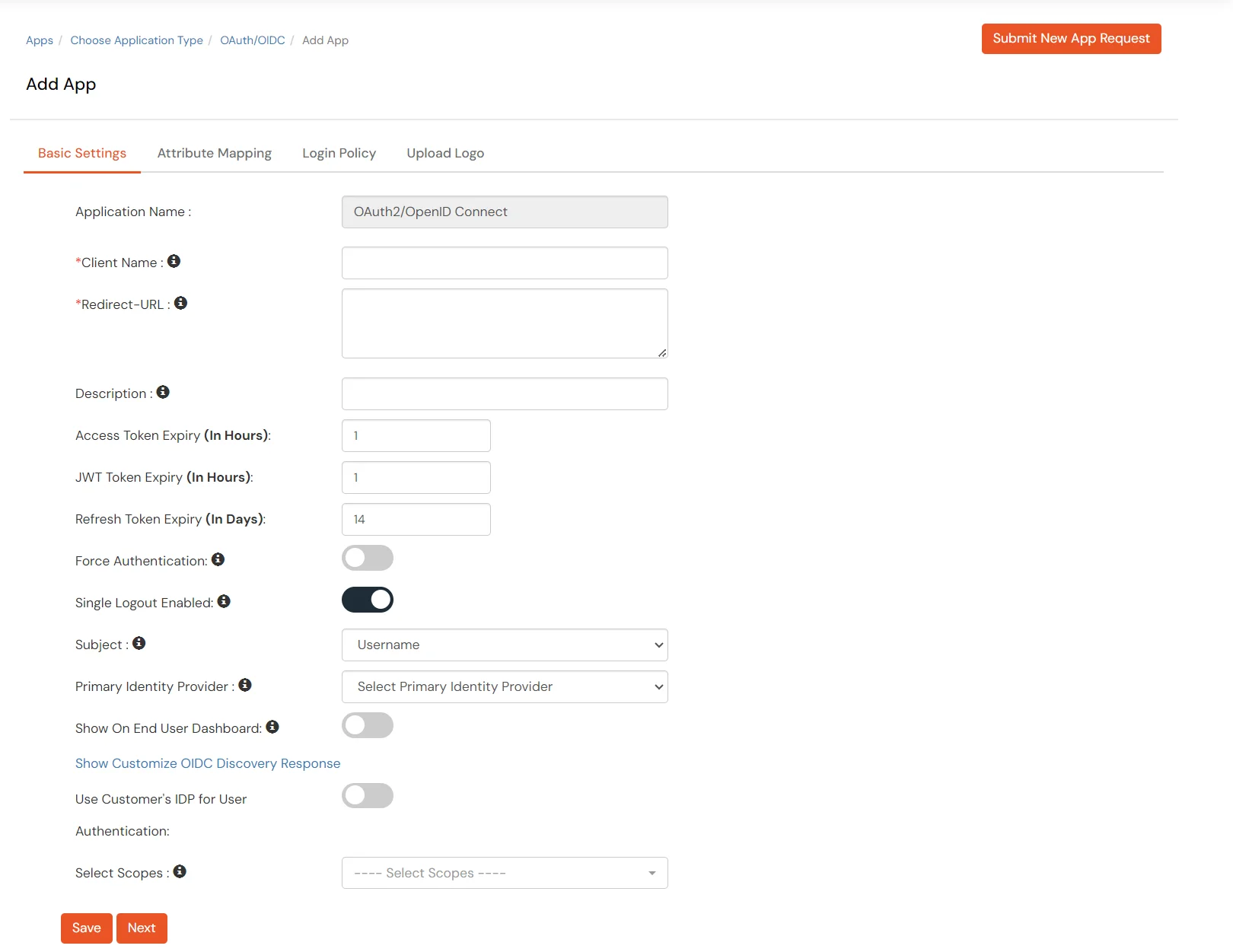
- Add Description if required. You can also configure the
Access/JWT/Refresh token expiry time.
- Access Token Expiry: For how long the provided access token should be valid from creation. [In Hours] A new access token has to be generated after the expiry.
- JWT Token Expiry: For how long the generated JWT token should be valid. [ In Hours ]
- Refresh Token Expiry: For how long the generated refresh token should be valid. [In Days] You will have to generate a new refresh token after the mentioned no. of days.
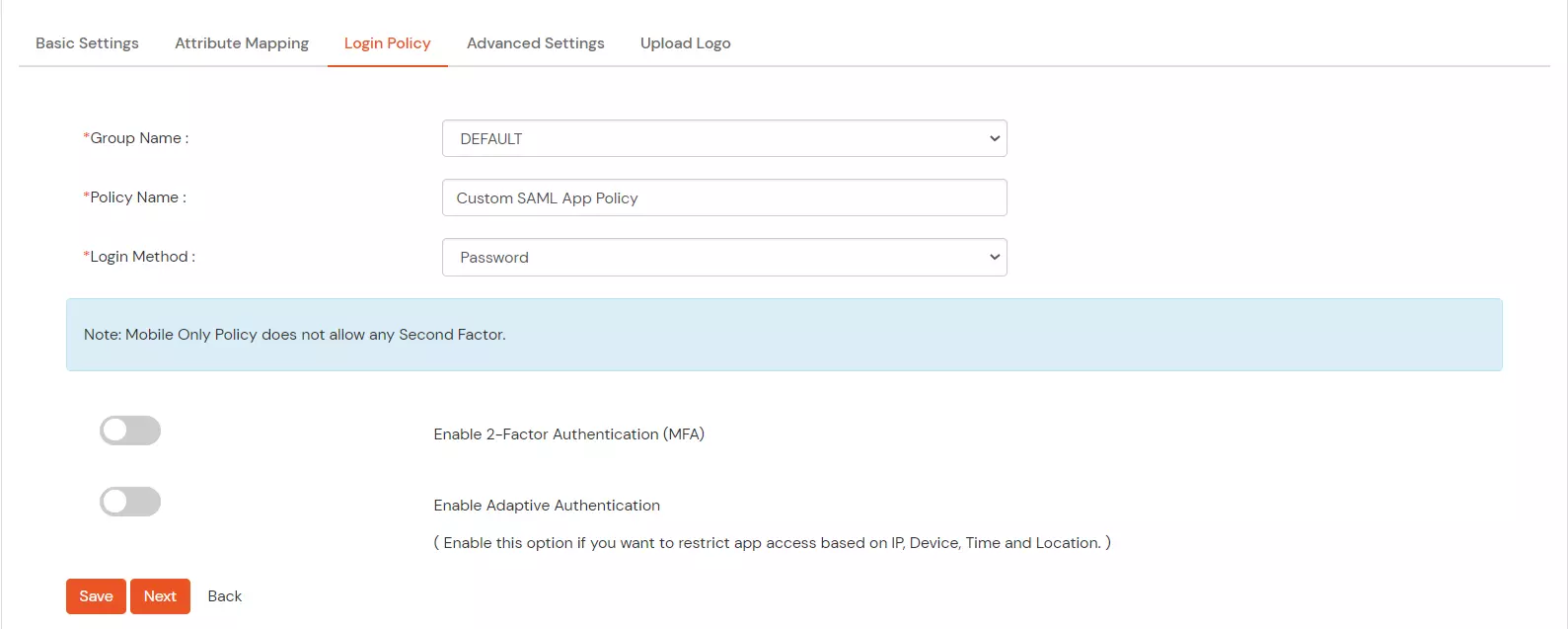
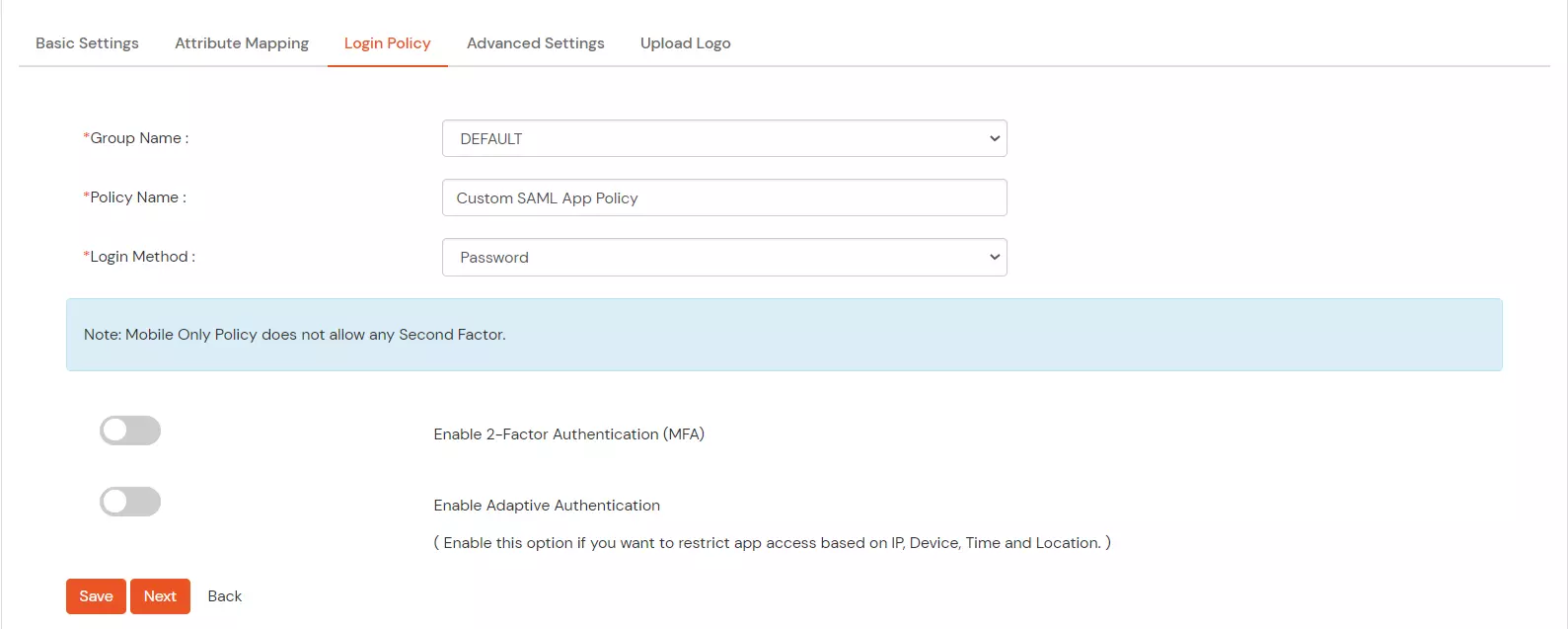
- Adding an Authentication Policy for the application :
- Select a Group Name from the dropdown – the group which should have access to the OAuth SSO using this app.
- Give a policy name for Custom App in Policy Name.
- Select the Login Method Type for authentication like Password, Mobile, etc.
- Enable
2 Factor/Adaptive for authentication if required.
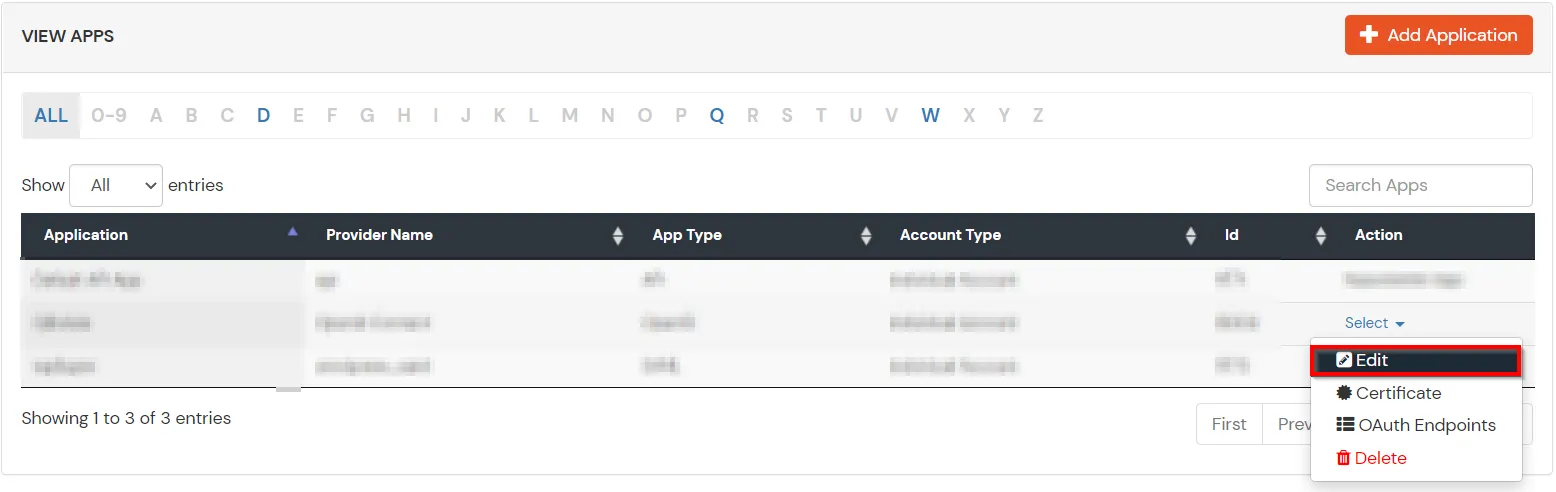
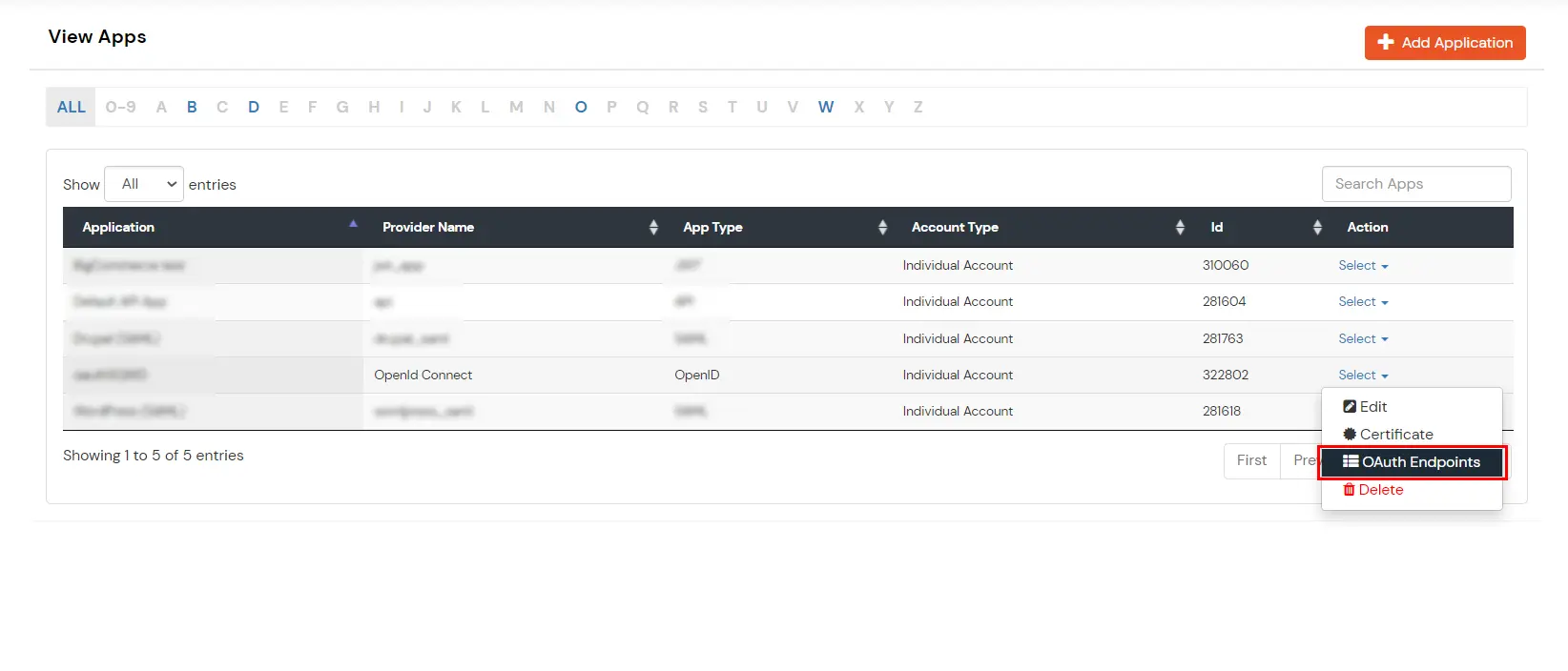
- Getting required app details/updating app information:
- Go to the Apps section from the side menu. From the list of apps configured, locate the app you created. You can see the Select > > Edit option present in front of that specific app.
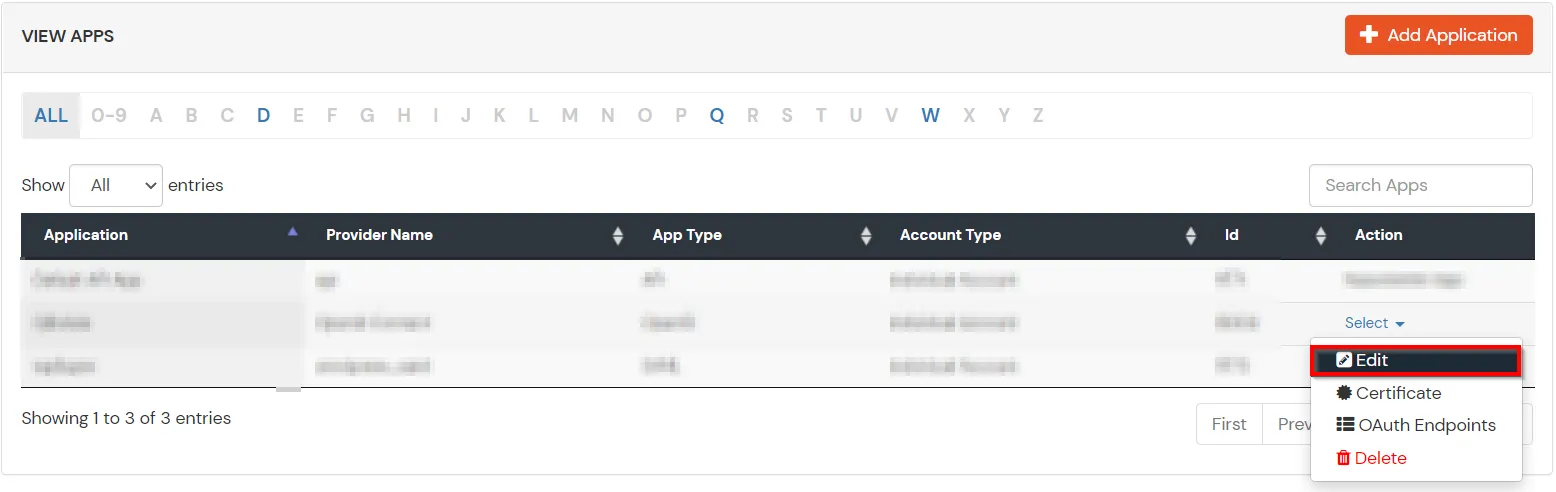
- You can edit any of the above-mentioned details in case you want to change them.
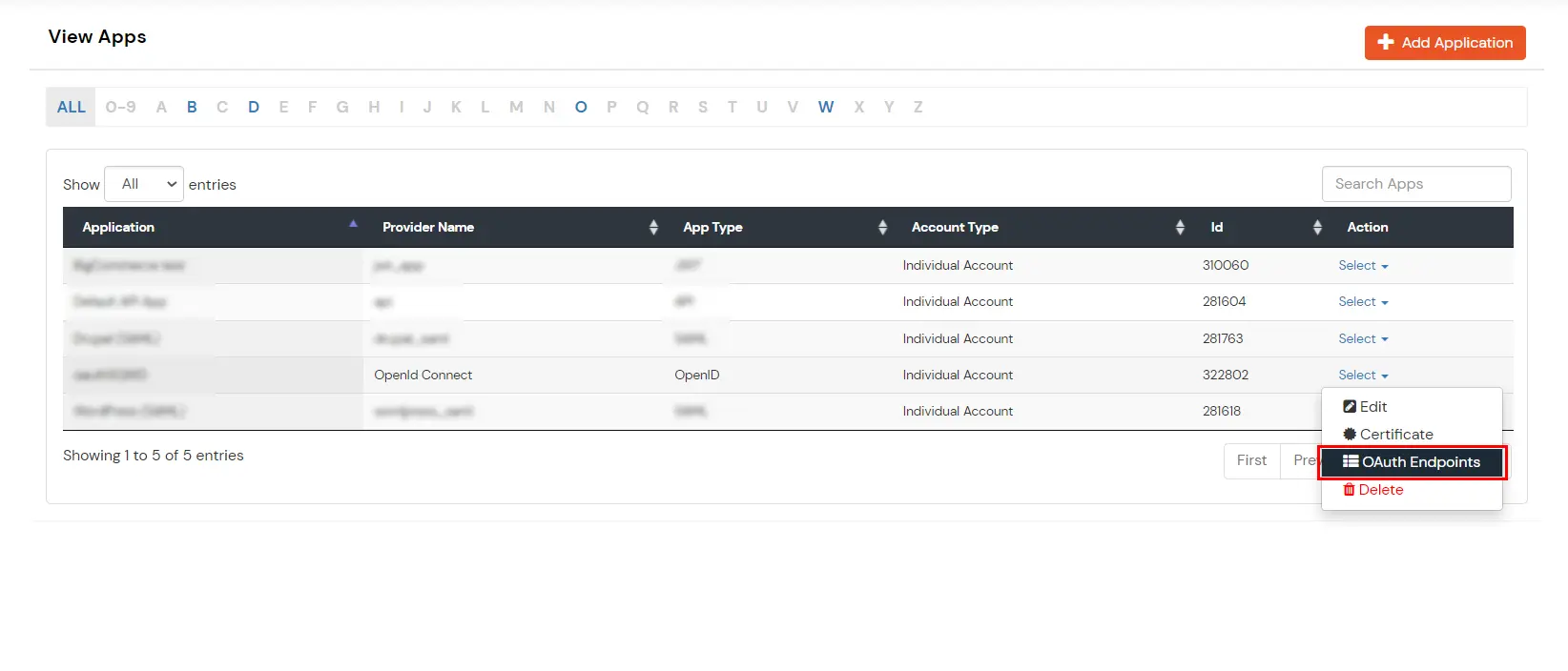
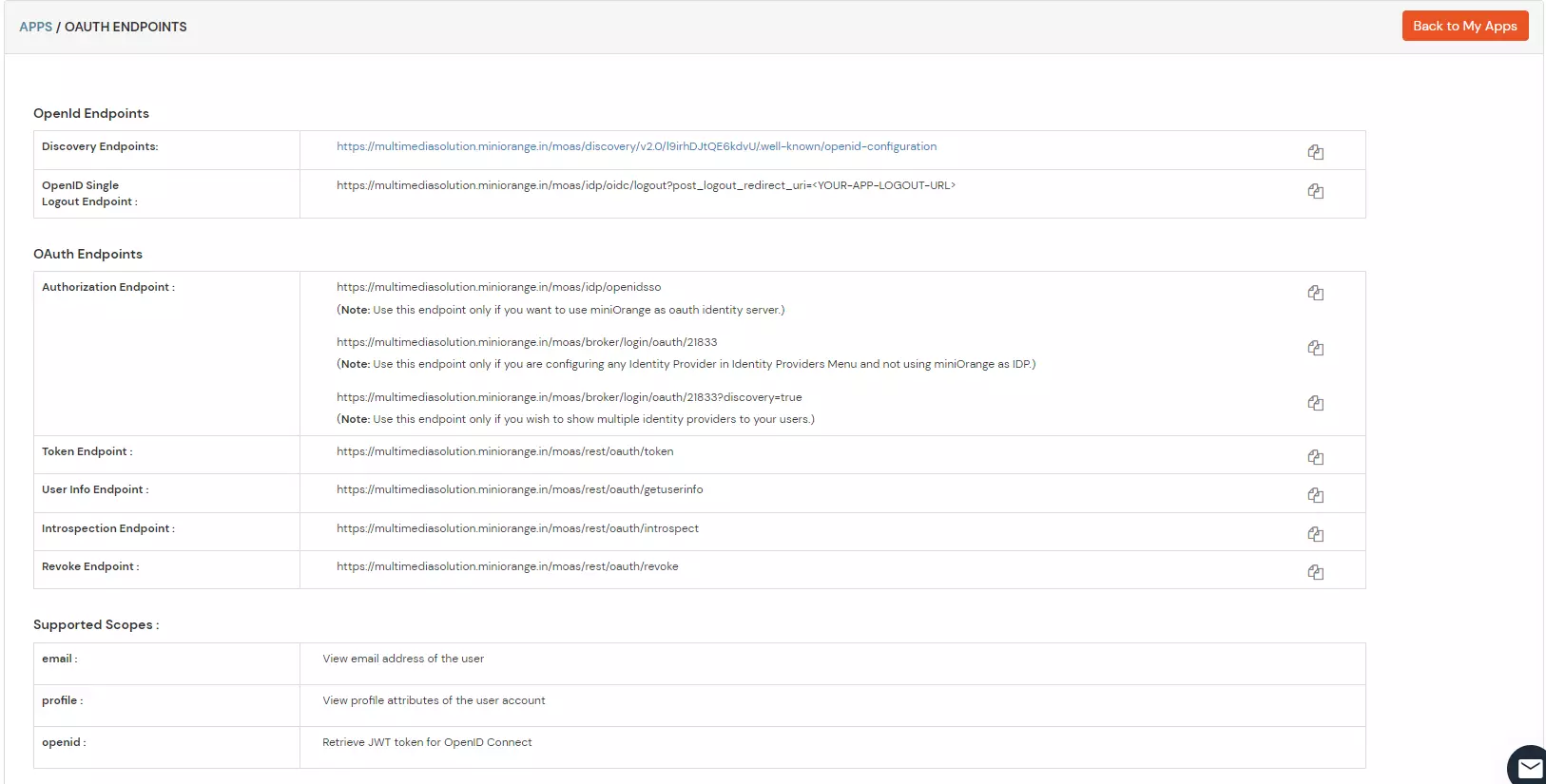
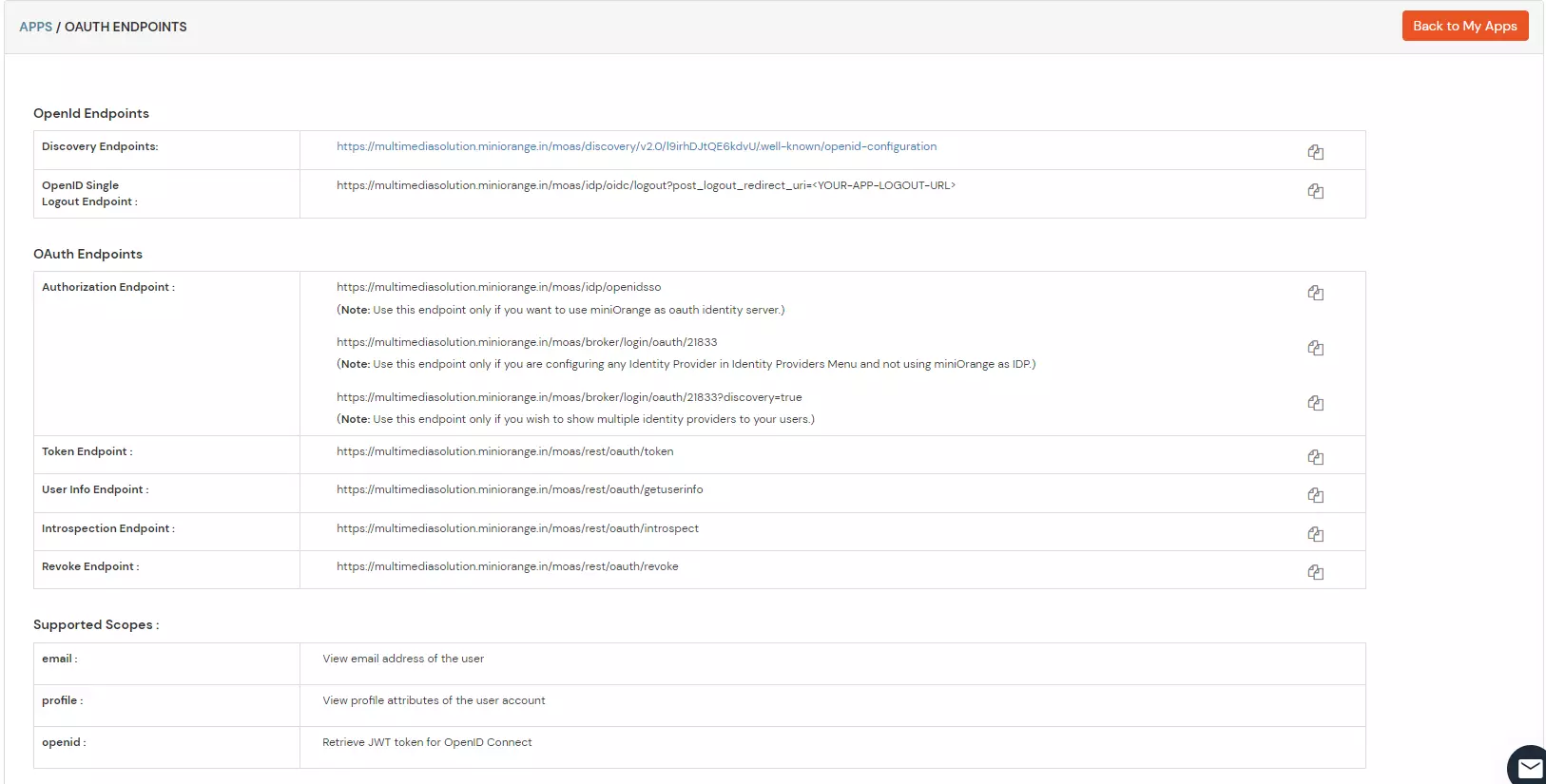
- OAuth Endpoints:
- Authorization Endpoint
[ https://<your-domain>.xecurify.com/moas/idp/openidsso ]:
- This endpoint is used to authenticate the end user with their miniOrange credentials. This authenticates the users and returns a response back to the redirect_url based on the parameters passed in the request. [Mainly the authorization code]
- This endpoint takes the following parameters :
- Client_id :client_id of the application as configured in the previous steps
- Redirect_uri:The callback URL where you want to return the response
- scope :scope of authorization or level of access, you can send a single or multiple scopes separated by ‘+’. e.g “email+openid”. We support the following scopes :
- Email : returns the email address of the user in the response
- Profile : returns user profile information in the response
- OpenID : returns the id_token containing user profile details.
- This returns the authorization code and the state parameters in the response.
- Token Endpoint
[ https://<your-domain>.xecurify.com/moas/rest/oauth/token ]:
- This endpoint returns the following :
- Id_token Contains user attributes and signatures which you have to validate with provided public certificate.
| iss |
https URI that indicates the issuer |
| sub |
identifier of the user at the issuer |
| aud |
client_id of the requesting client |
| nonce |
the nonce parameter value received from the client |
| exp |
expiration time of this token |
| iat |
time when this token was issued |
| auth_time |
time the authentication happened |
| at_hash |
the first half of a hash of the access token |
- Access_token :Valid for 1 hour and can be used to access user info or other endpoints until it is expired.
- This endpoint takes the following parameters in the request:
- Client_id : client_id of the application as configured in the previous steps.
- Client_secret : client_secret of the application as configured in the previous step.
- Redirect_url : The callback url where the response should be posted.
- Code : The authorization code received from the authorization endpoint.
- Grant_type : The OAuth grant you want to use for the request.
- User Info Endpoint
[ https://<your-domain>.xecurify.com/moas/api/oauth/getuserinfo ]: [Required in case of OAuth Only]
- This API can be used to fetch user profile information with an access token that was assigned to the user. A GET request is sent to the user info endpoint.
- You need to send the access token in the authorization header to receive the user details.
- Single Logout URL :
[ https://<your-domain>.xecurify.com/moas/idp/oidc/logout?post_logout_redirect_uri ]:
- This endpoint removes the active user session from the miniOrange IDP and redirects the user to the URL mentioned in the post_logout_url parameter.
- Click here for a detailed setup guide if you want to authenticate your users via any external Identity Provider like Active Directory, Okta, OneLogin, etc. or any other custom IDPs.