Need Help? We are right here!
Search Results:
×A reverse proxy server, also known as a gateway server, acts as an intermediary between clients and the origin server. Generally, the clients are everyday internet users and the servers are resource providers that offer to view and access various websites and services.
The reverse proxy’s primary purpose is to protect the origin server by monitoring and filtering user requests before they reach the server. It receives HTTP endpoint requests forwarded to the origin server, essentially working as an endpoint at the network’s edge.


A reverse proxy is important for two main reasons; security and performance of the server. If both of these factors are taken care of, users are more likely to visit and use your website or web application, engage in it, trust it, and consider making purchases on it.
It is also important for medium-to-large businesses with a considerable amount of traffic to protect their websites and web applications from DDOS attacks. The larger the business, the more likely it is for a malicious entity to attack it.
Lastly, services of this size are expected to have 100% uptime. Any system overload or failure disrupts the user base and can have a serious impact on future traffic and revenue generation.
Protects the resource server
Regulates inbound traffic
Masks the origin server’s IP address
Improves user experience with global server load balancing and web acceleration
Improves server performance with load balancing, content caching, and rate limiting
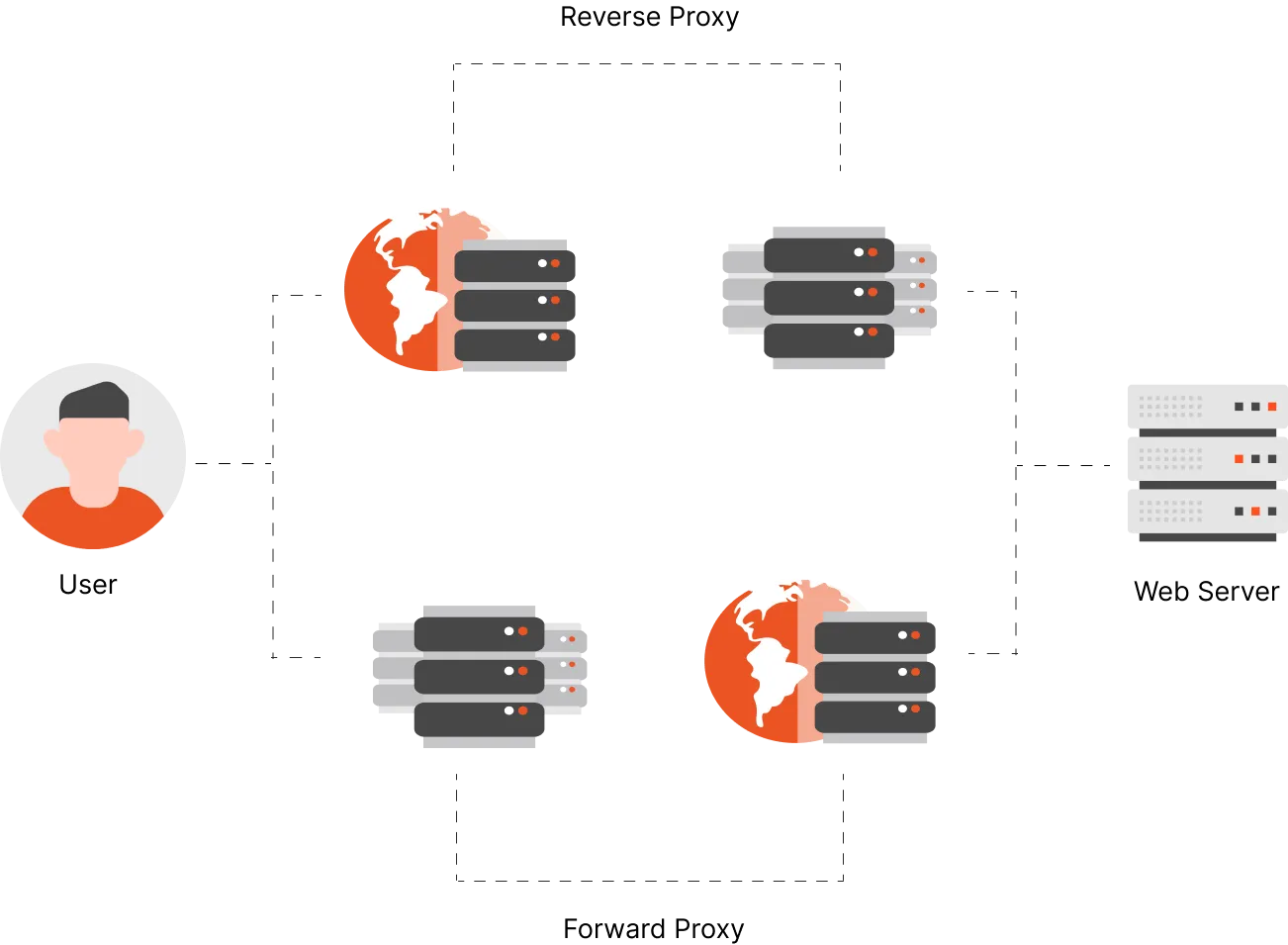
Protects the clients
Regulates outbound traffic
Masks the user’s IP address
Improves user experience by overcoming browser restrictions
Protects user identity and privacy with anonymity features

A reverse proxy server can protect your applications like Google Drive, Google Photos, Google Meet, Gmail, and much more in Google Workspace. Easily configure account security and access control for Google Business and Education.
Reverse Proxy provides URL Rewriting which helps improving the URL’s readability, hide the URL structure, redirect page traffic and a lot more. URL Rewriting improves page SEO and user experience when visiting a page, especially when the page is a revenue source.

Header-based Authentication allow user authentication on parameters set in HTTP header for SSO login into apps like Adobe Connect and benefits of providing customizability, without downloading third-party apps and maintain message integrity.
NFT Token Gating helps restrict access to content behind the ownership of Non-Fungible Tokens(NFTs). It can be further applied to restricting communities, memberships, social platforms, meetings, & webinars, etc. with NFT ownership.

Multi-factor authentication is an authentication method that requires user identity verification before authenticating and logging in. It enforces security policies, which include MFA, OTP over SMS/Email, and a lot more.

Reverse Proxy allows you to whitelist a range of IP addresses and block certain countries from accessing the Shopify site for controlling your Shopify site, set custom user restrictions, and secure Shopify admin login from malicious user access.

Load Balancing is used by high-volume websites to distribute numerous resource requests to different servers. It functions as a ‘traffic cop’, redirecting traffic to online servers in case one server goes down.
Global Server Load Balancing is where requests to a site are distributed to servers globally to reduce user load times in accessing the origin server’s content from different time zones, increasing site reliability.
Caching is for storing a version of a web page in a fast storage location and then displaying it in response to a request. It reduces the load on the origin server and improves load speed and user experience.
Reverse Proxy encrypts/decrypts your Secure Sockets Layer (SSL)/Transport Layer Security (TLS) communication taking the computational load off the origin server to reduce latency for distant users.
Compressing incoming and outgoing data, along with content caching, leads to Web acceleration. This and other features take the load off your origin server and boost site performance, resulting in web acceleration.
Monitoring and logging traffic is another perpetual task and resource-consuming but can be done by a reverse proxy server. It improves system security by filtering out harmful traffic and potential DDOS attacks.
For non-business-critical tasks. Just here for exploring and having fun.
For industry experts, but non-crucial and general use to corporate websites.
For upcoming business new to the market looking for a competitive edge.
For business tasks & corporate leaders looking for the most stable and best solutions in one place
|
Free
$0
The price is for one instance |
Pro
$15
The price is for one instance |
Business
$150
The price is for one instance |
Enterprise
Custom
The price is for one instance |
|
|---|---|---|---|---|
|
Number of Domains |
1 Domain | 5 Domains | 15 Domains | Unlimited/Custom |
| Security | ||||

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|
| Performance | ||||

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|
| Authentication & Authorization | ||||

|

|

|

|
|

|

|
Up to 100 users | More than 101+ | |

|

|

|

|
|

|

|

|

|
|
| Advanced Security | ||||

|

|

|

|
|

|

|

|

|
|

|

|

|

|
|
| (Email + call support) | (Email + Video call + 12x5 Support) - $1 /user/ month | (Email + Video call + 24x7 Support) |
The purpose of a reverse proxy server is to filter and direct resource requests to the backend server. By doing so, it protects the main server from malicious attacks and takes load off of it. Reverse proxies also mask the location and IP address of external sites and make them look like they are part of the main domain.
A content delivery network is a bunch of distributed servers that allow easy access to cached mirrored pages for geographically distant clients. It can be used in conjunction with a reverse proxy server to take the load off the origin server and create a robust infrastructure for your website or web application.
Load balancing is a feature of reverse proxy servers which distributes the load of resource requests to multiple servers. This takes the load off the main server and allows it to perform other tasks, ensuring it doesn’t go down in the process.
An Application Programming Interface (API) allows you to access resources and run commands on another platform without having direct access to the site’s UI by logging into it. It is different from a reverse proxy server, or gateway server, which filters incoming requests coming to the main server and protects it from attacks.
A reverse proxy server is a must-have for businesses of any size that are serving users beyond a local level. It protects the resource server from malicious attacks, makes sure it doesn’t get overloaded, and provides a host of other features that let you configure access levels, monitor and log traffic, and accelerate web response times for a better user experience.
In this blog, we will see how you can easily secure user login to Adobe Connect to safeguard login to your session meetings by using a reverse proxy [...]
Keycloak is an open source Identity and Access Management (IAM) system which can easily secure your apps and services [...]
The most effective way to protect your videos is by setting up a reverse proxy and setting video restriction mode for the videos [...]
Google Workspace holds the entire collection of data that a company generates by storing [...]