Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
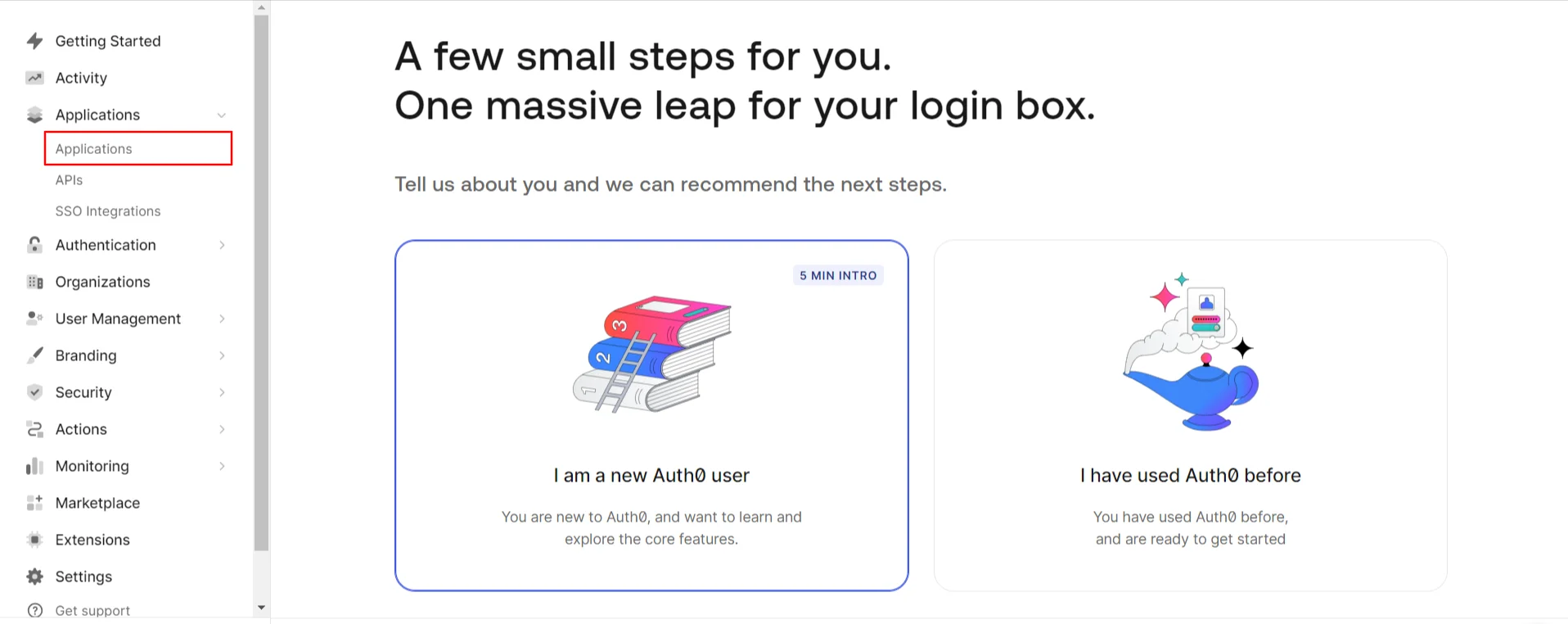
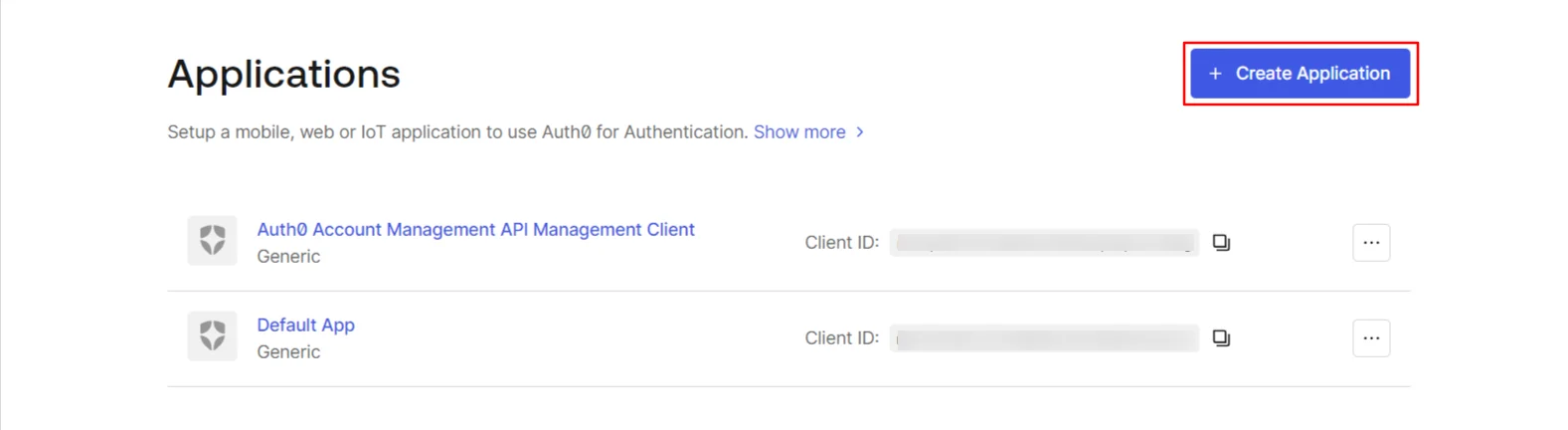
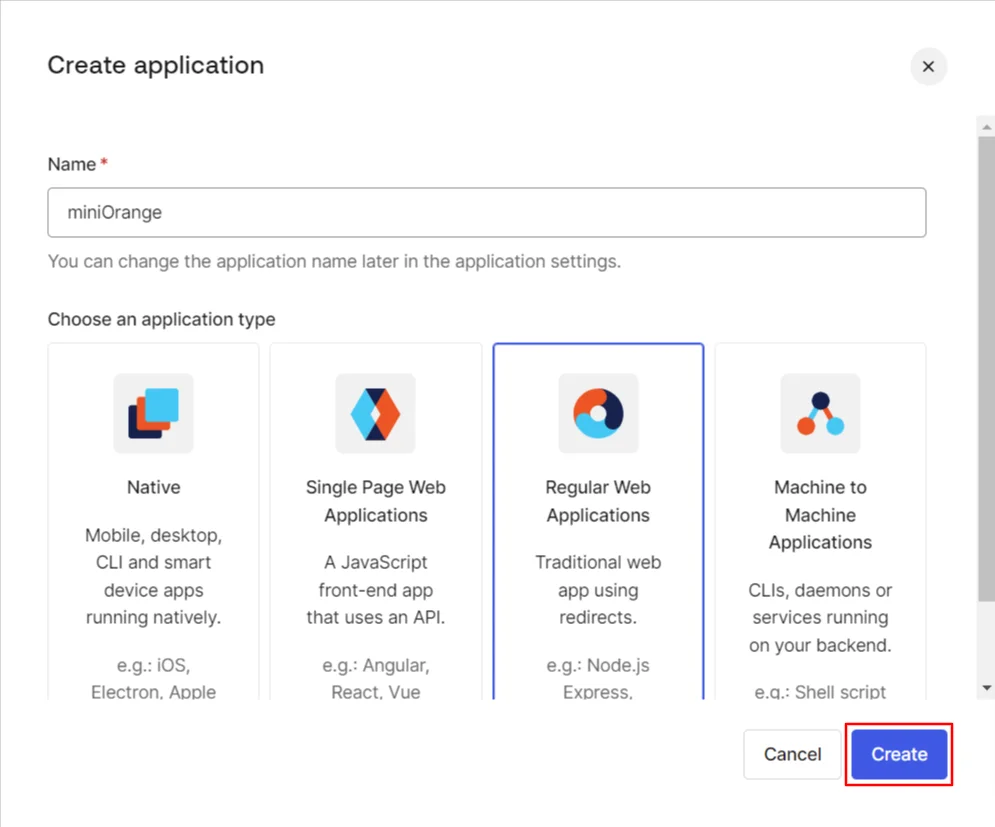
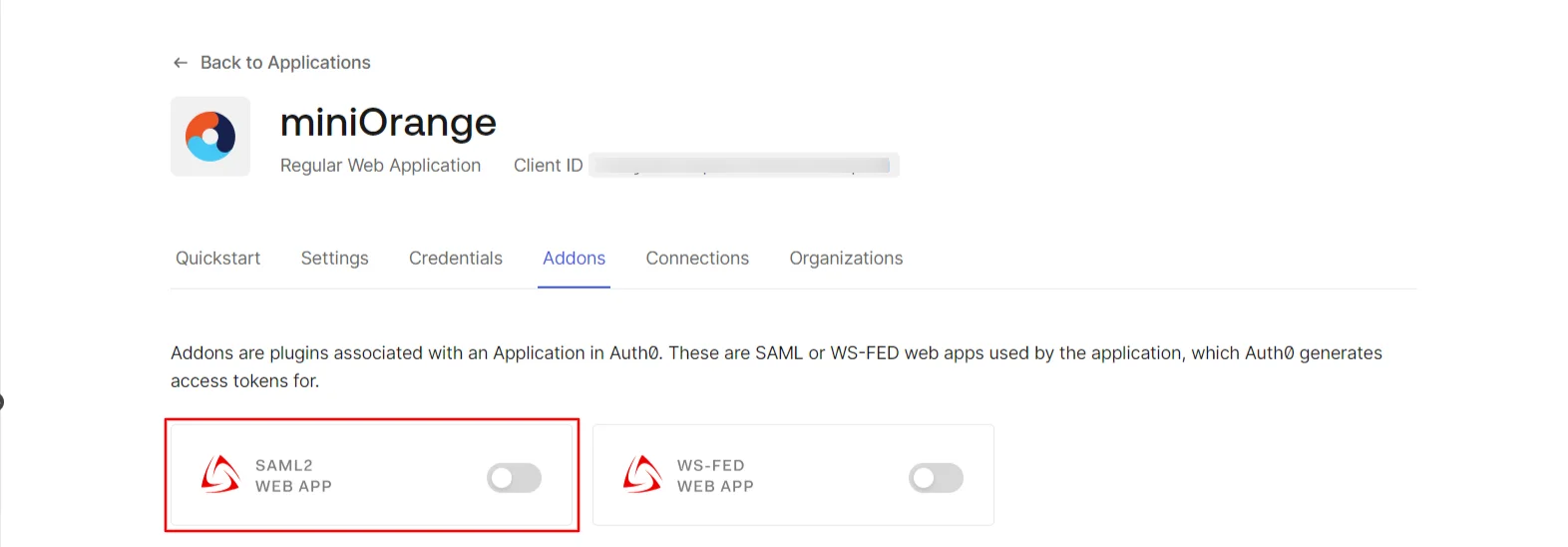
×miniOrange Identity Broker service solution enables cross protocol authentication. You can configure Auth0 as an IDP for Single Sign-On (SSO) into your applications/websites. Here, Auth0 will act as an Identity Provider (IDP) and miniOrange will act as a broker.
We offer a pre-built solution for integrating with Auth0, making it easier and quick to implement. Our team can also help you set up Auth0 as SAML or OIDC IDP to login into your applications.
miniOrange offers free help through a consultation call with our System Engineers to configure SSO for different apps using Auth0 as IDP in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
Please make sure your organisation branding is already set under Customization >> Login and Registration Branding in the left menu of the dashboard.
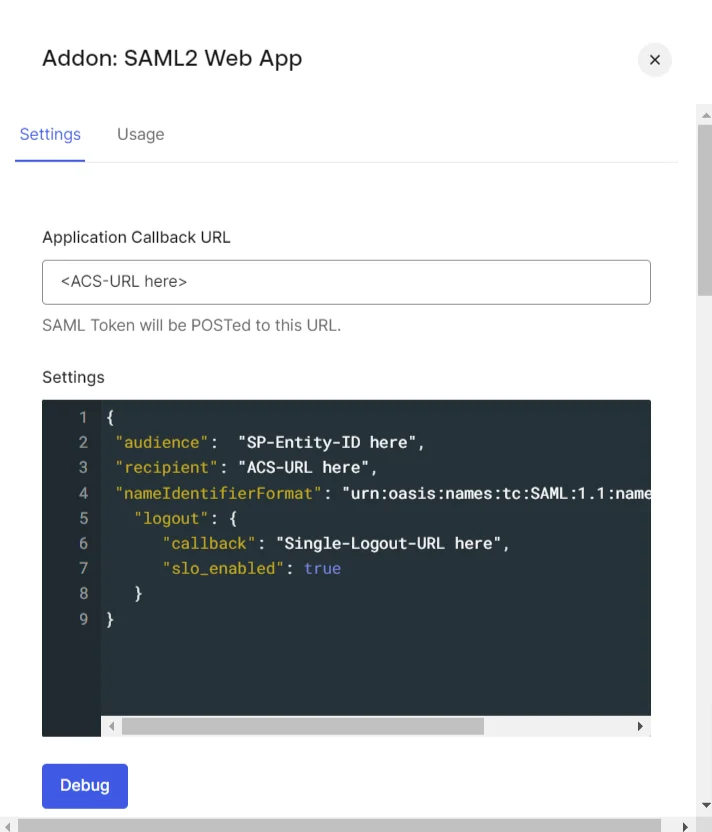
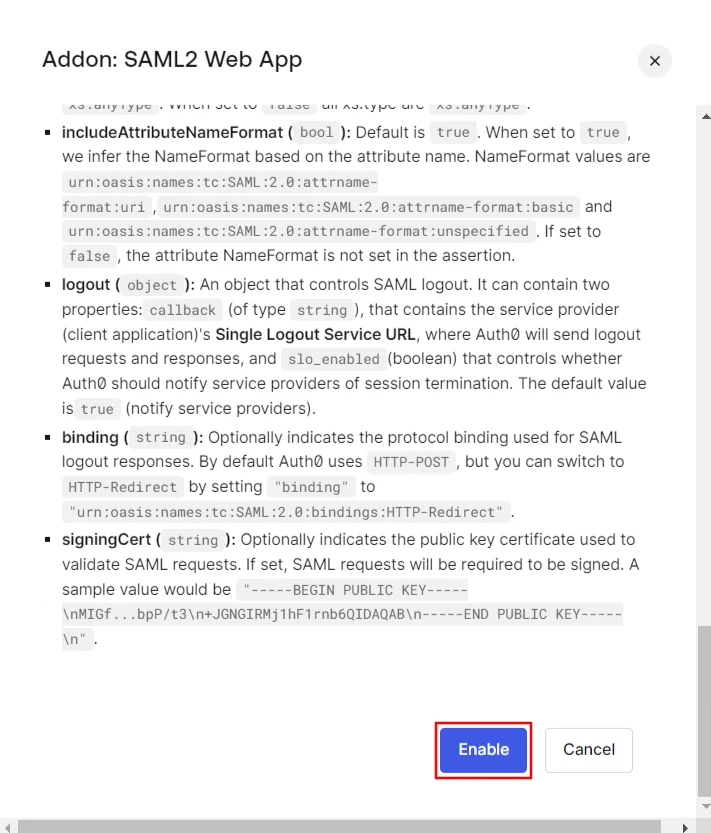
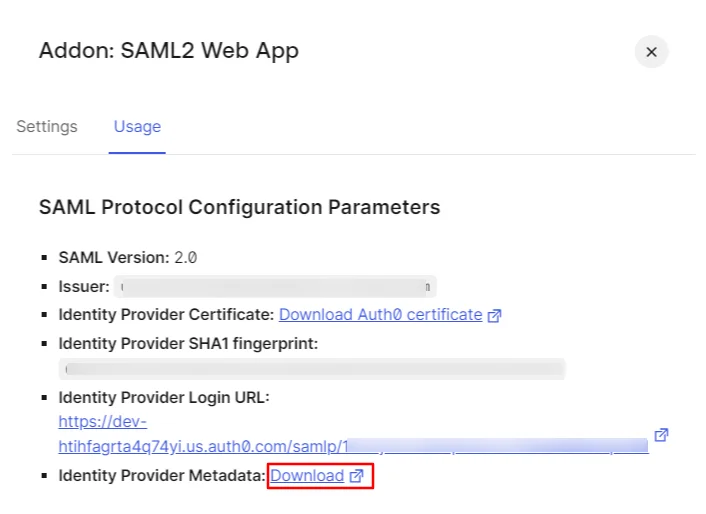
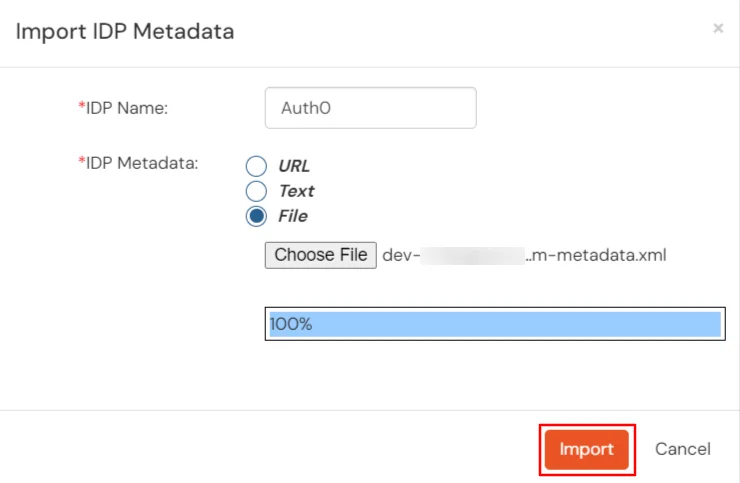
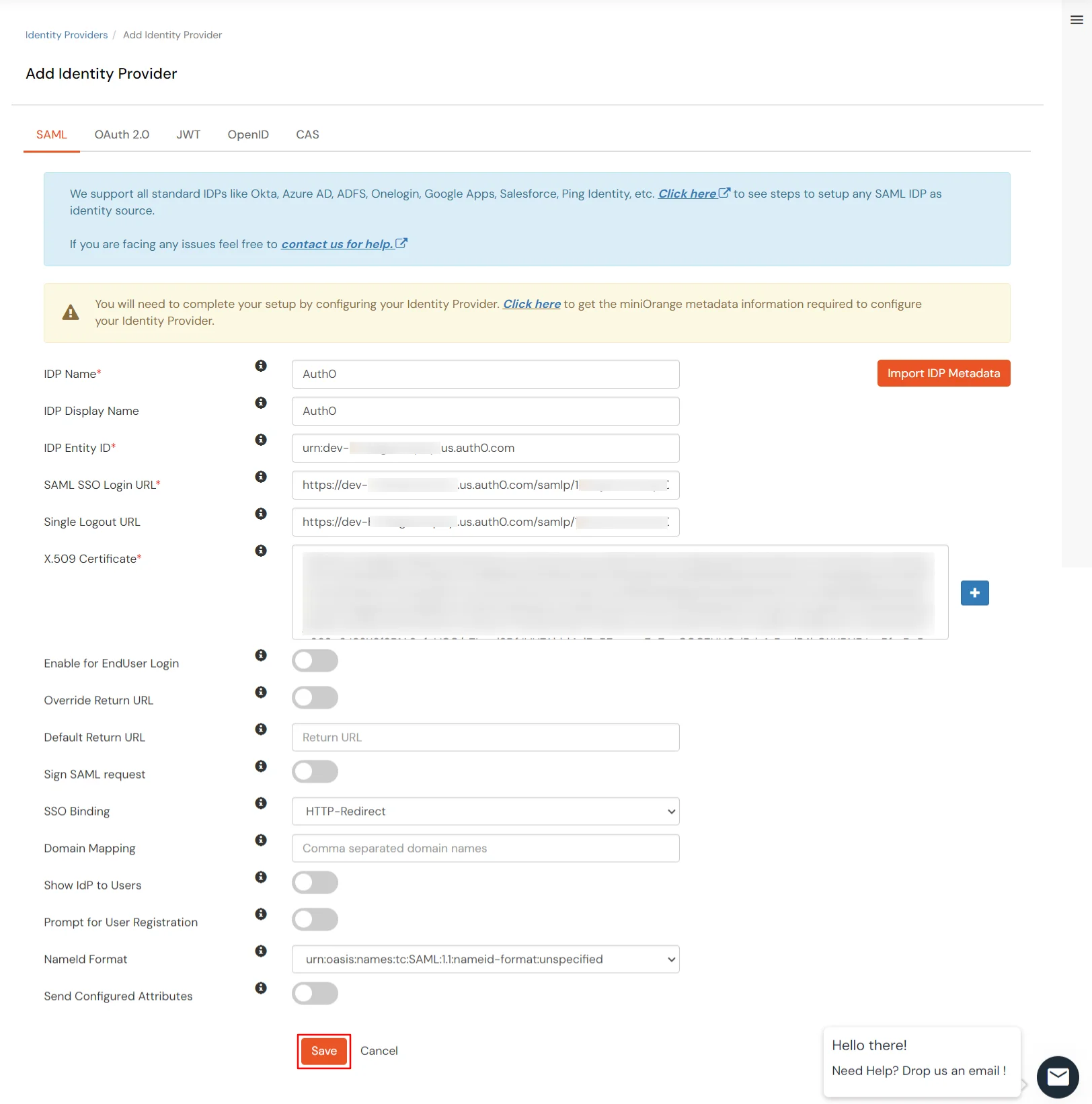
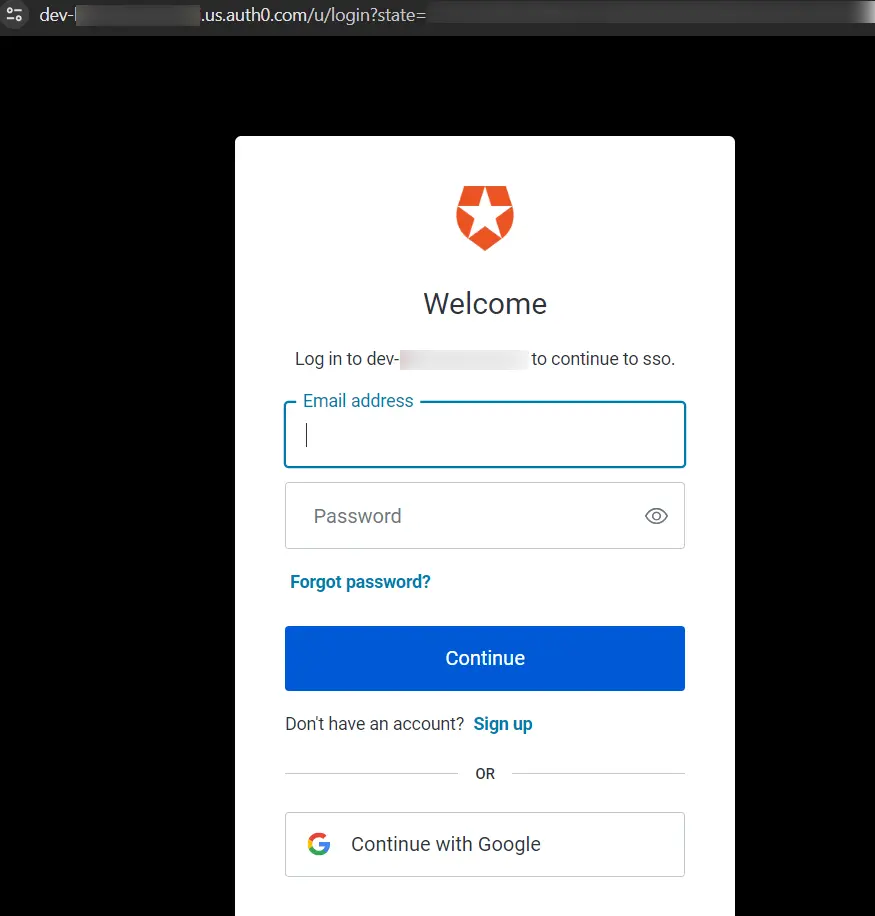
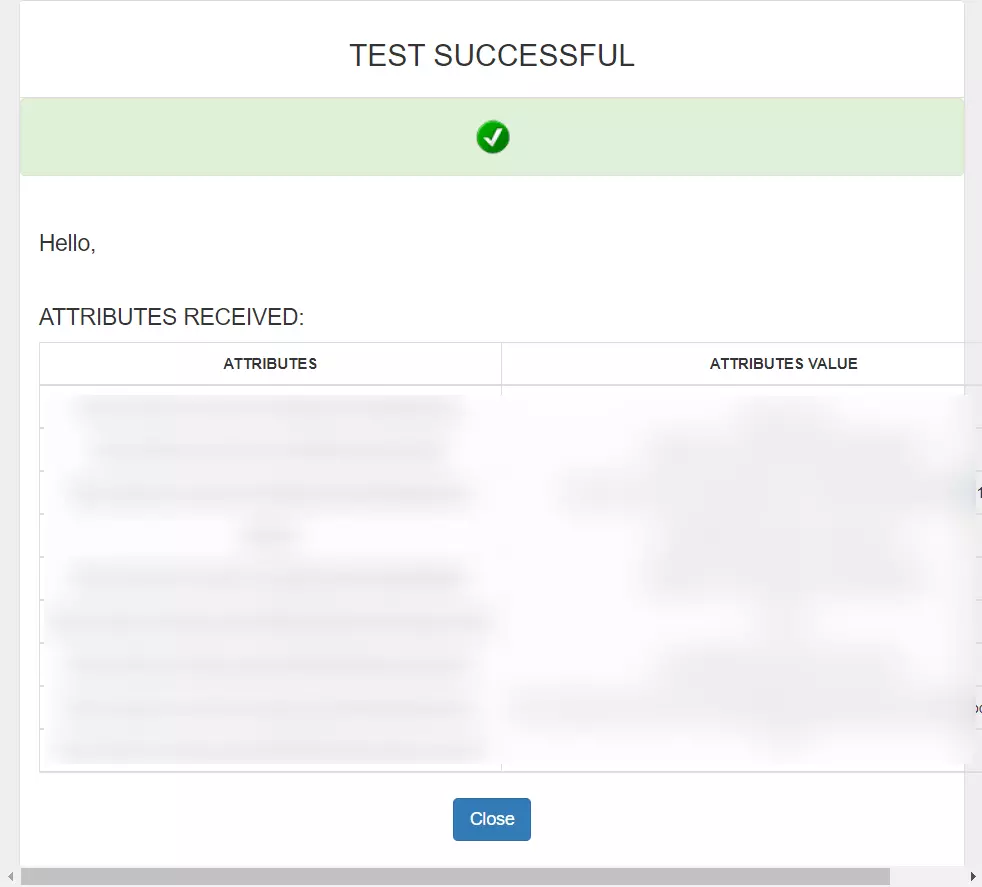
Mentioned below are steps to configure Auth0 as IDP via SAML and OAuth configuration. Follow the steps accordingly based on your requirement (SAML or OAuth).




Follow the steps to configure Auth0 as IdP by OAuth configuration.
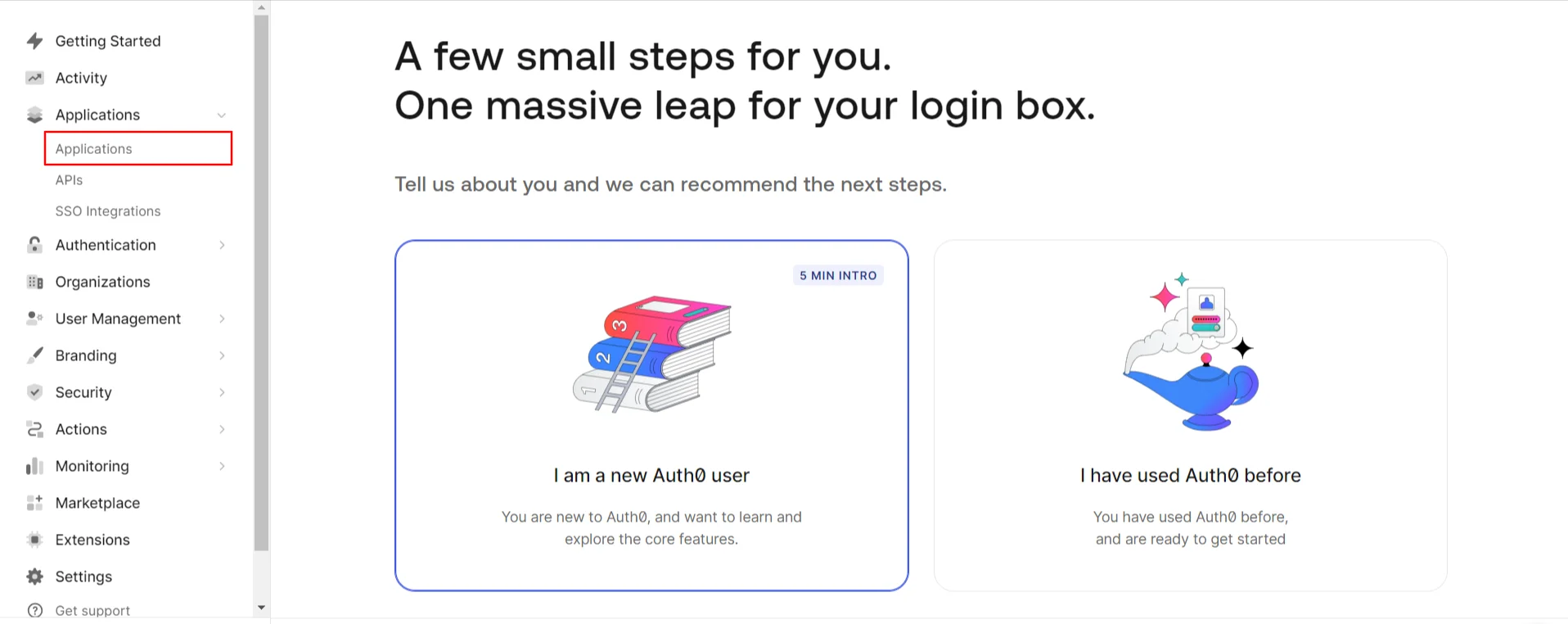
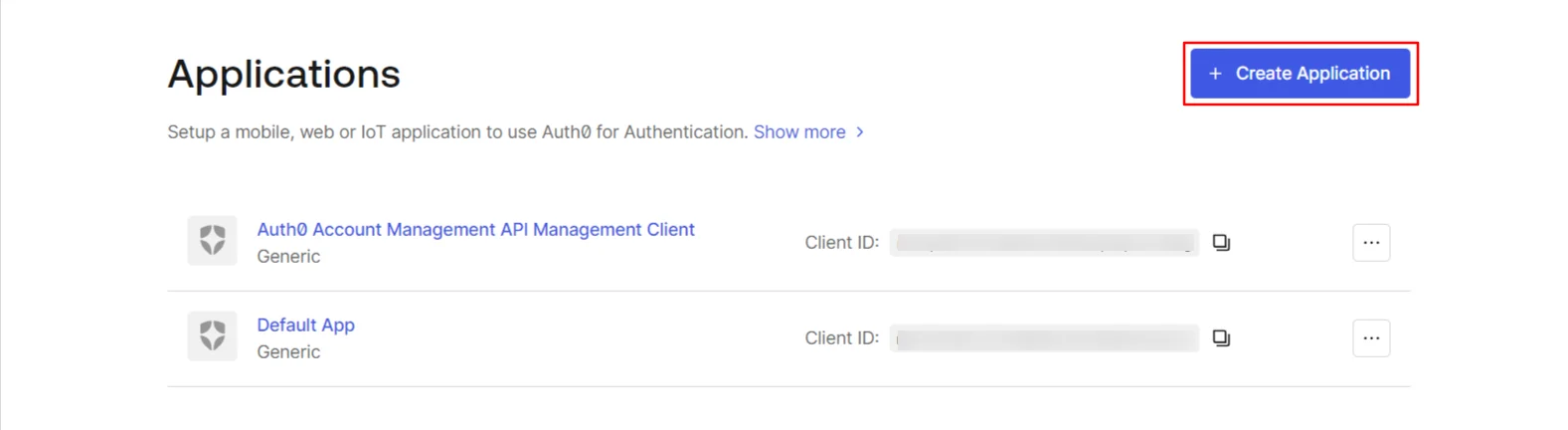
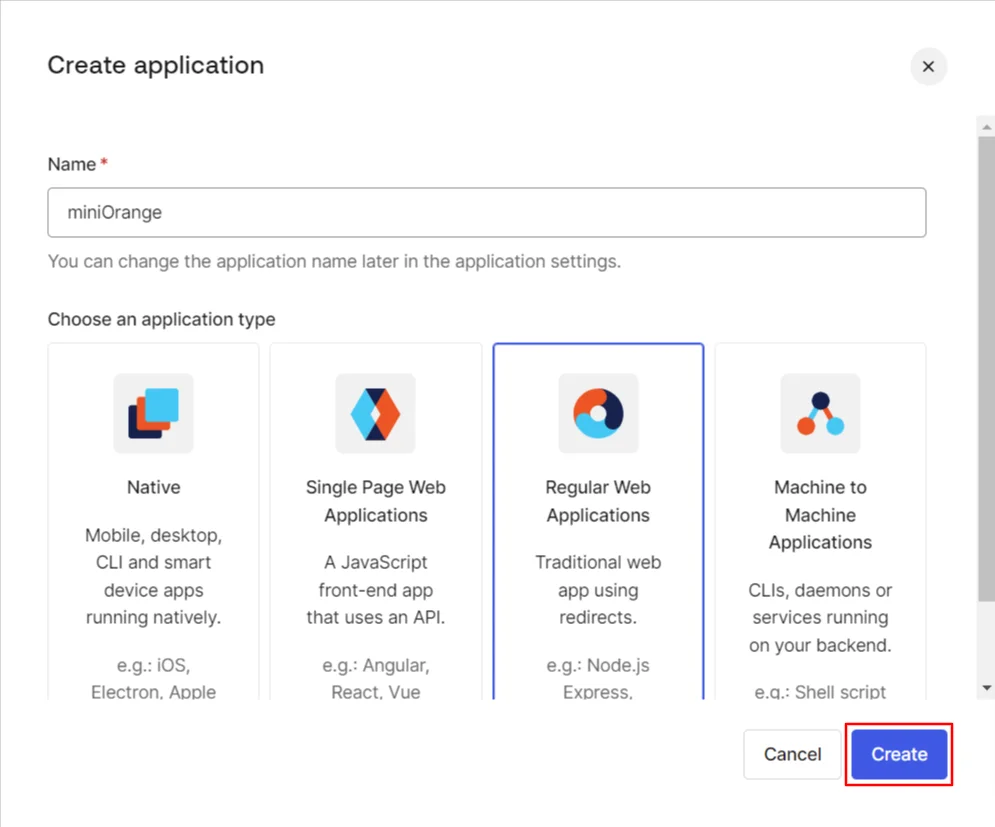
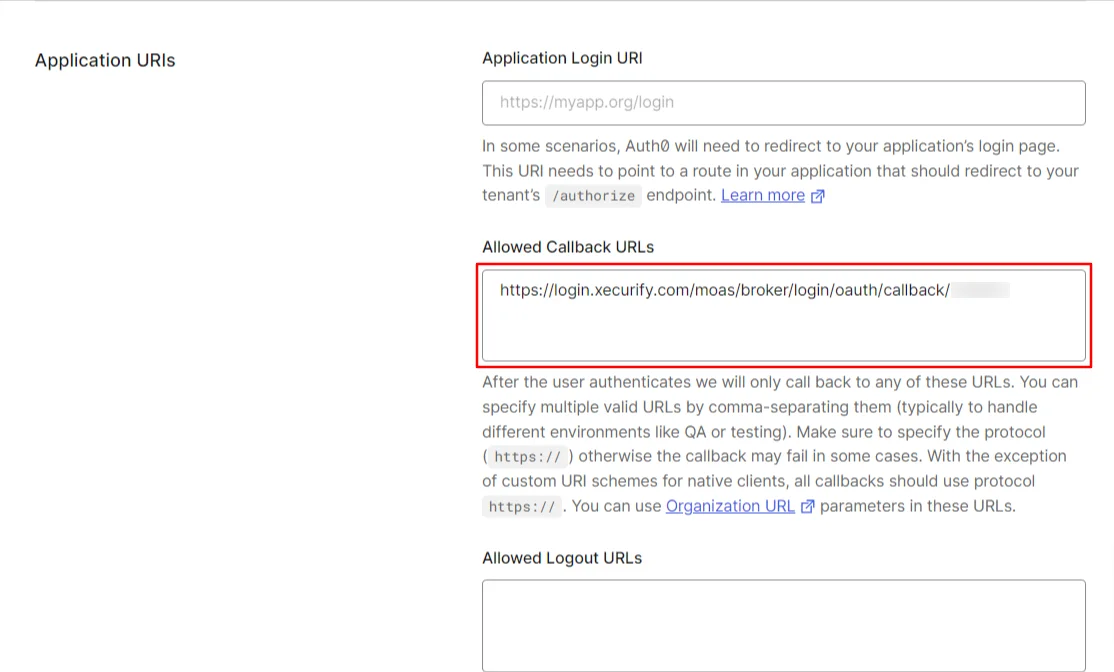



Follow the steps to configure Auth0 as IdP by OAuth configuration.


| IDP Name | Custom Provider |
| IDP Display Name | Choose appropriate Name |
| OAuth Authorize Endpoint | https://{your-base-url}/as/authorization.oauth2 | OAuth Access Token Endpoint | https://{your-base-url}/as/token.oauth2 | OAuth Get User Info Endpoint (optional) | https://{your-base-url}/idp/userinfo.oauth2 |
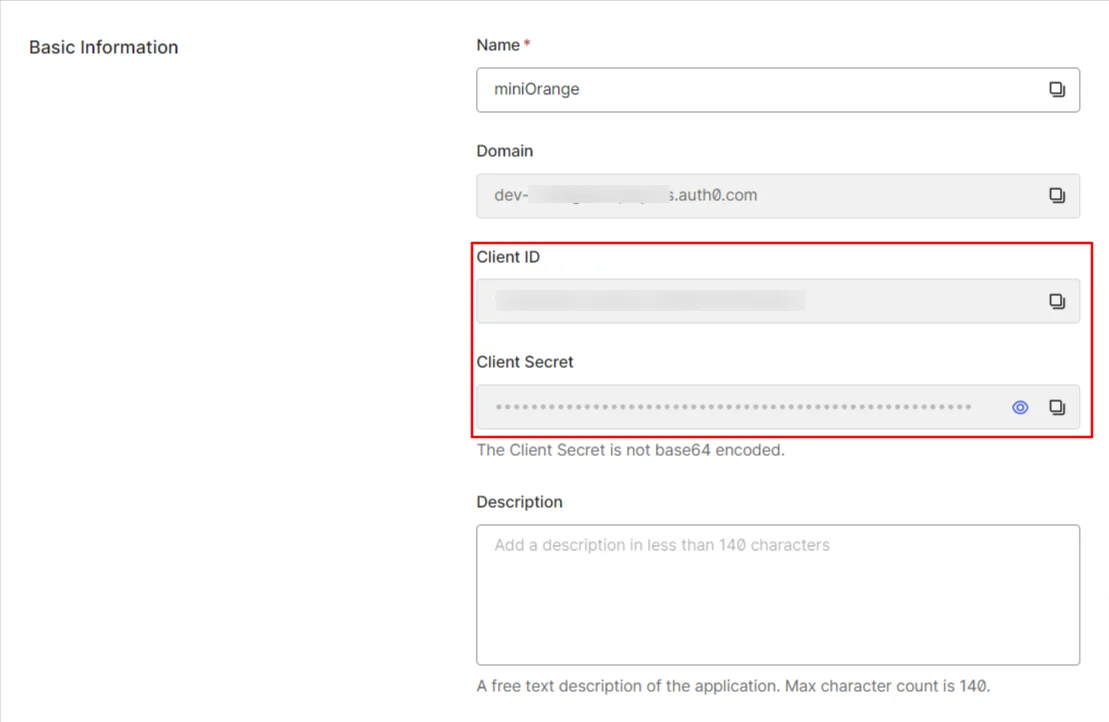
| Client ID | From step 1 |
| Client secret | From step 1 |
| Scope | auto |
If you have already configured your application in miniOrange you can skip the following steps.




| Service Provider Name | Choose appropriate name according to your choice |
| SP Entity ID or Issuer | Your Application Entity ID |
| ACS URL X.509 Certificate (optional) | Your Application Assertion Consumer Service URL |
| NameID format | Select urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress |
| Response Signed | Unchecked |
| Assertion Signed | Checked |
| Encrypted Assertion | Unchecked |
| Group policy | Default |
| Login Method | Password |





| Client Name | Add appropriate Name |
| Redirect URL | Get the Redirect-URL from your OAuth Client |
| Description | Add if required |
| Group Name | Default |
| Policy Name | As per your Choice |
| Login Method | Password |


Note: Choose the Authorization Endpoint according to the identity source you configure.
https://{mycompany.domainname.com}/moas/idp/openidssohttps://{mycompany.domainname.com}/broker/login/oauth{customerid}


In case you are setting up SSO with Mobile Applications where you can't create an endpoint for Redirect or Callback URL, use below URL.
https://login.xecurify.com/moas/jwt/mobile



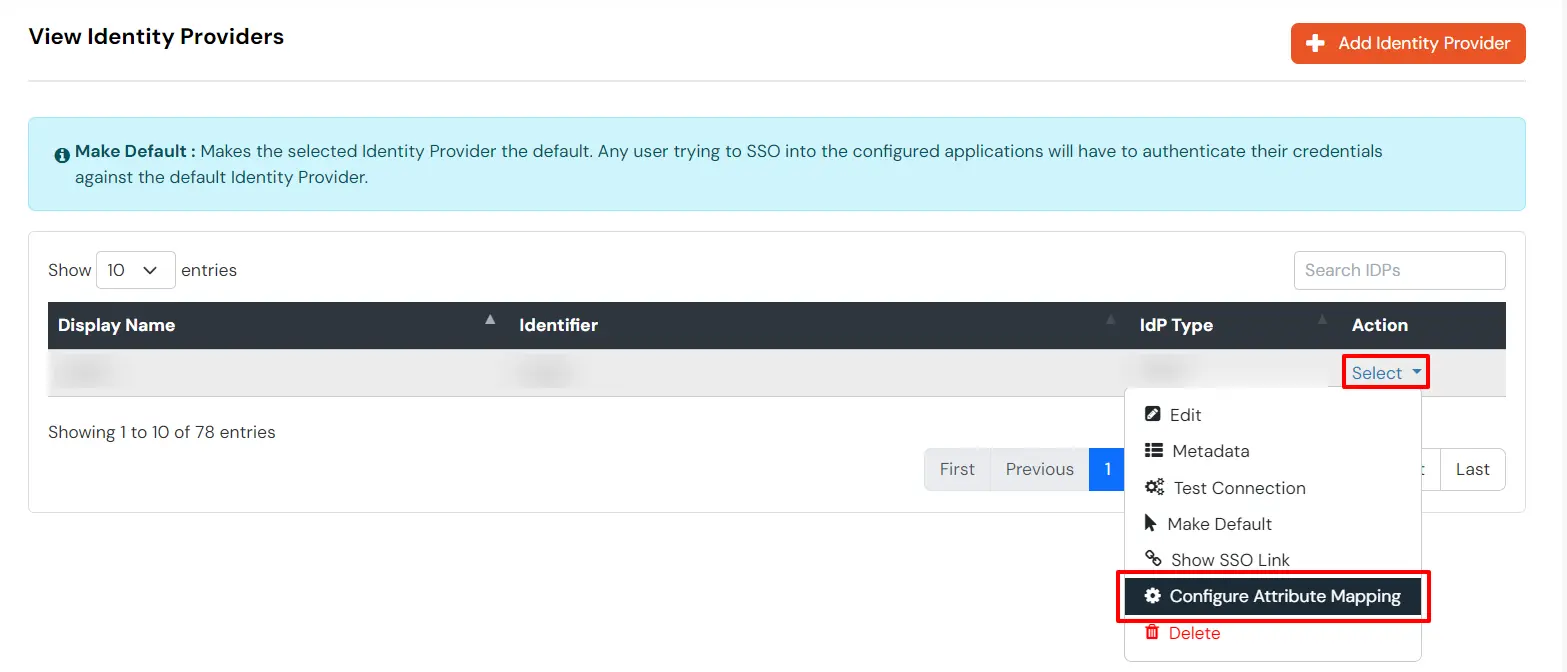
You can follow this guide, if you want to configure multiple IDPs (Identity Providers) and give users the option to select the IDP of their choice to authenticate with.
You receive these error message when you try to SSO in to an application that has been set up to use as External IdP using OAuth based Single Sign-On (SSO).
Users can’t log in through Auth0.
To fix the issue, follow these steps:
Users are sent to the wrong page after logging in.
To fix the issue, follow these steps:
Users frequently get logged out or see token expiration messages.
To fix the issue, follow these steps:
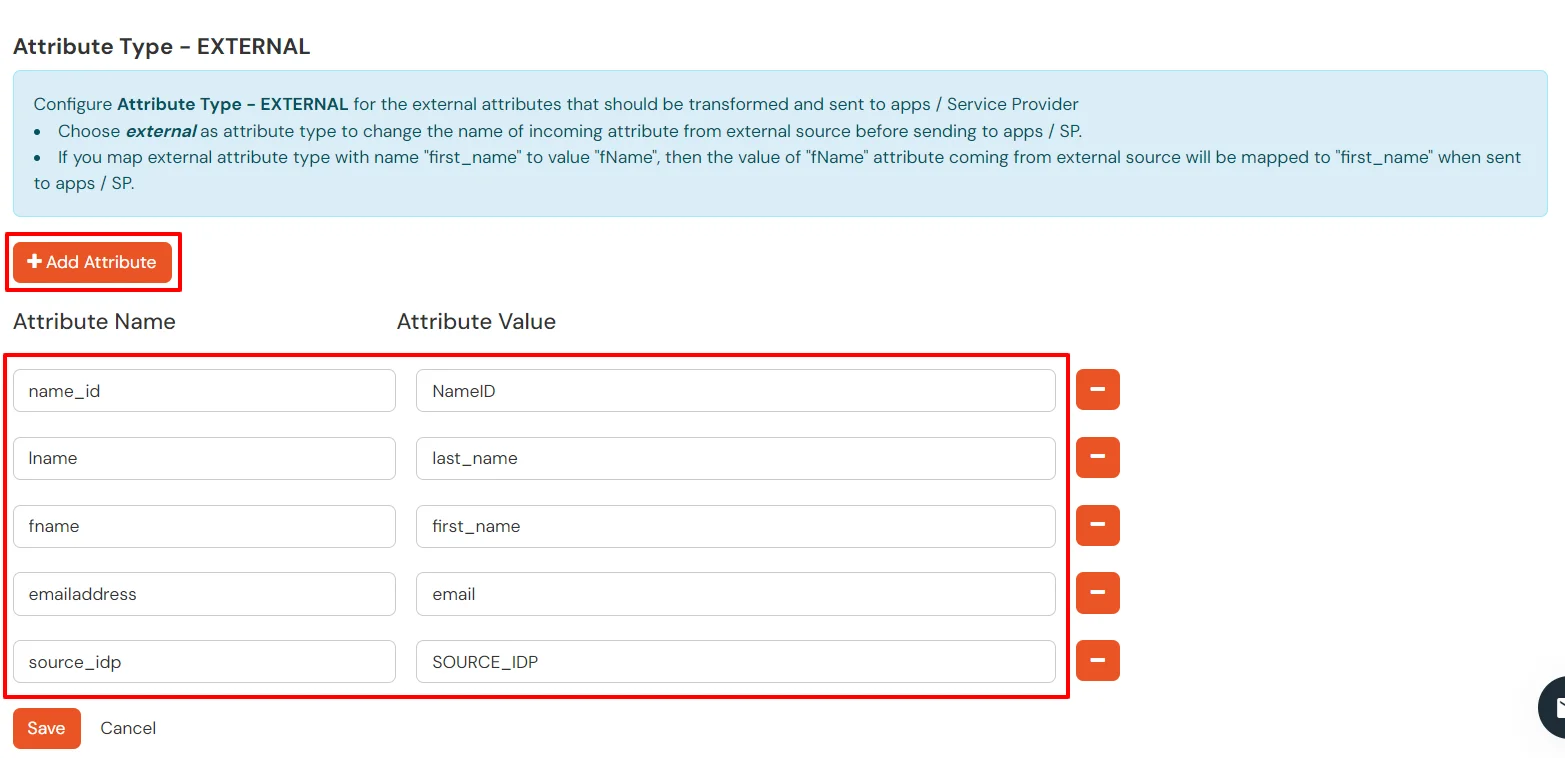
User profile data isn’t being displayed.
To fix the issue, follow these steps:
This happens when the Service Provider (SP) and Identity Provider (IdP) certificates don’t match or signature validation fails.
To fix the issue, follow these steps:
SAML assertions should have an audience that matches the SP’s entity ID.
To fix the issue, follow these steps:
Missing attributes can cause failures.
To fix the issue, follow these steps:
The Assertion Consumer Service (ACS) URL must be correctly set in the IdP for the response to be sent to the right place.
To fix the issue, follow these steps:
Our Other Identity & Access Management Products