Need Help? We are right here!
Search Results:
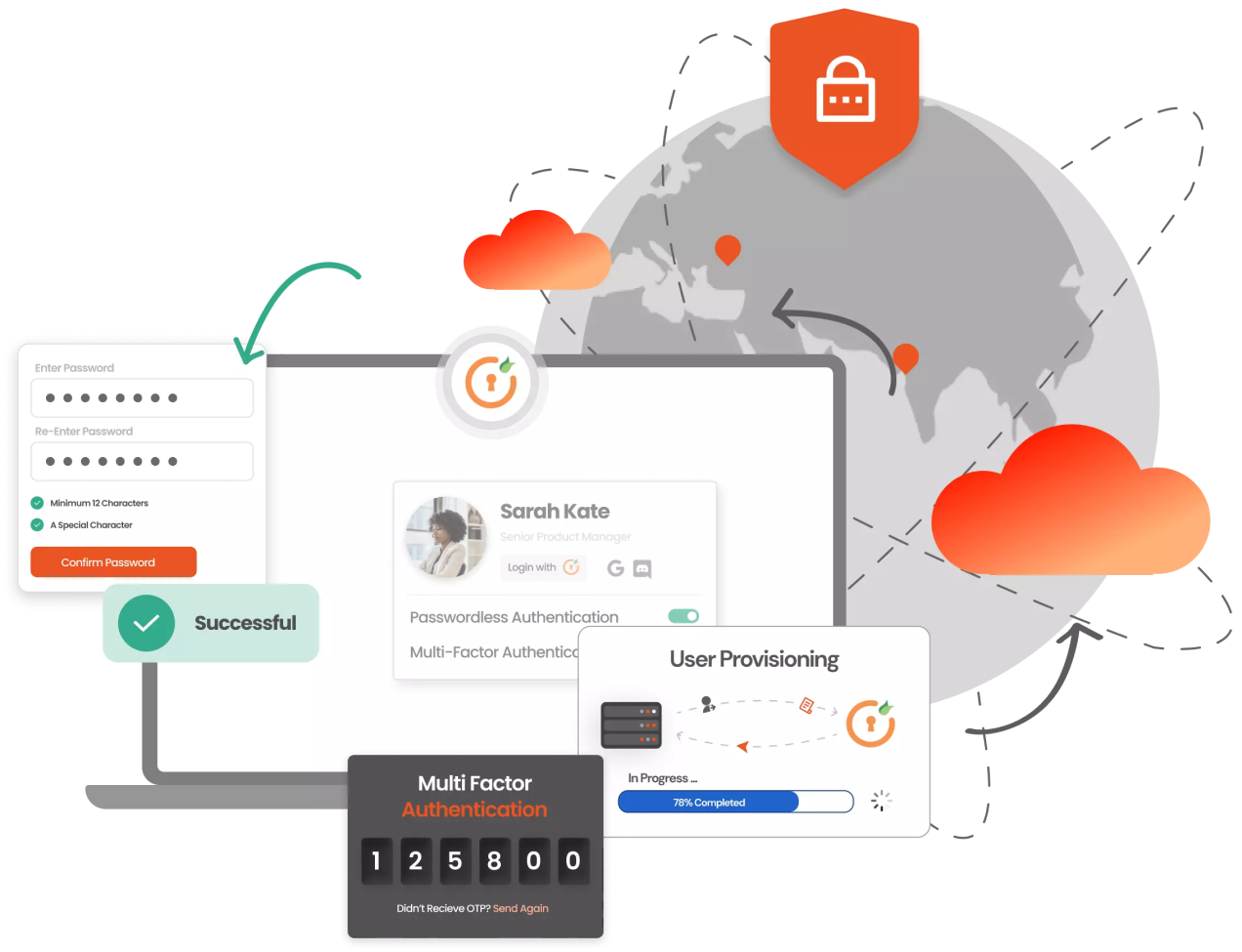
×Multi-Factor Authentication (MFA) is an authentication method that requires the user to provide two or more verification factors to gain access to critical enterprise resources and applications on the cloud or on-premise. MFA is a core component of a strong Identity and Access Management (IAM) policy, which prevents unauthorized access and cyber-attacks.
Hackers exploit vulnerabilities in VPNs using tactics like stolen credentials, malware, weak passwords, and social engineering. By implementing Multi-Factor Authentication (MFA) for VPNs, you can significantly reduce unauthorized access and breach of privacy.
miniOrange VPN MFA supports:
Multi-Factor Authentication (MFA) is a powerful solution to fortify the security of Windows, RDP, Linux, and MacOS platforms. The miniOrange MFA module seamlessly integrates with Microsoft Remote Desktop Web Access (RD Web), ensuring MFA access. The MFA implementation isn't restricted to Windows—it also spans to Linux and MacOS.
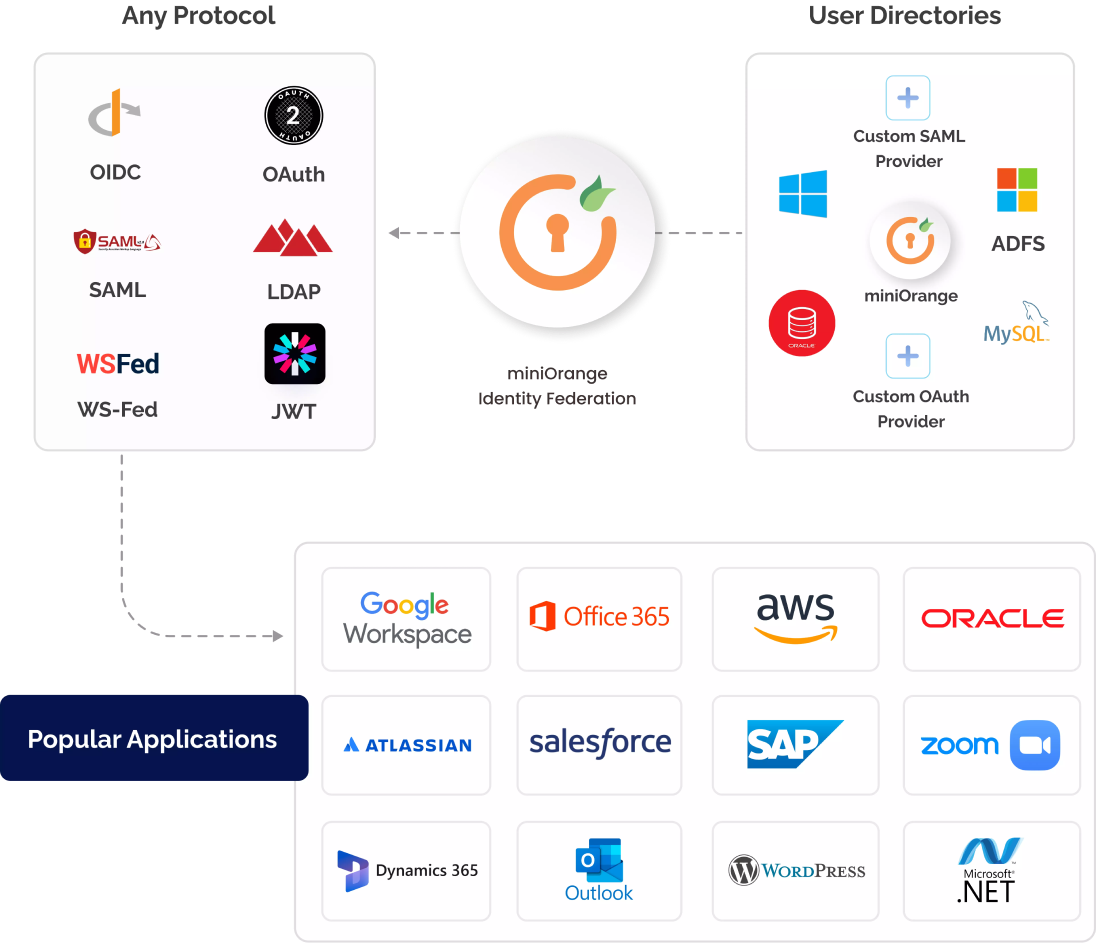
miniOrange MFA solution safeguards various application types — Cloud, On-Premises, & In-House, while supporting all authentication protocols like SAML, Radius, Open ID, and JWT. Replace outdated password-based authentication with modern MFA security. Even if your custom app built on PHP, .NET, React, Angular, or Node.js, lacks support for standard protocols, miniOrange seamlessly integrates MFA, enhancing security across your app landscape.
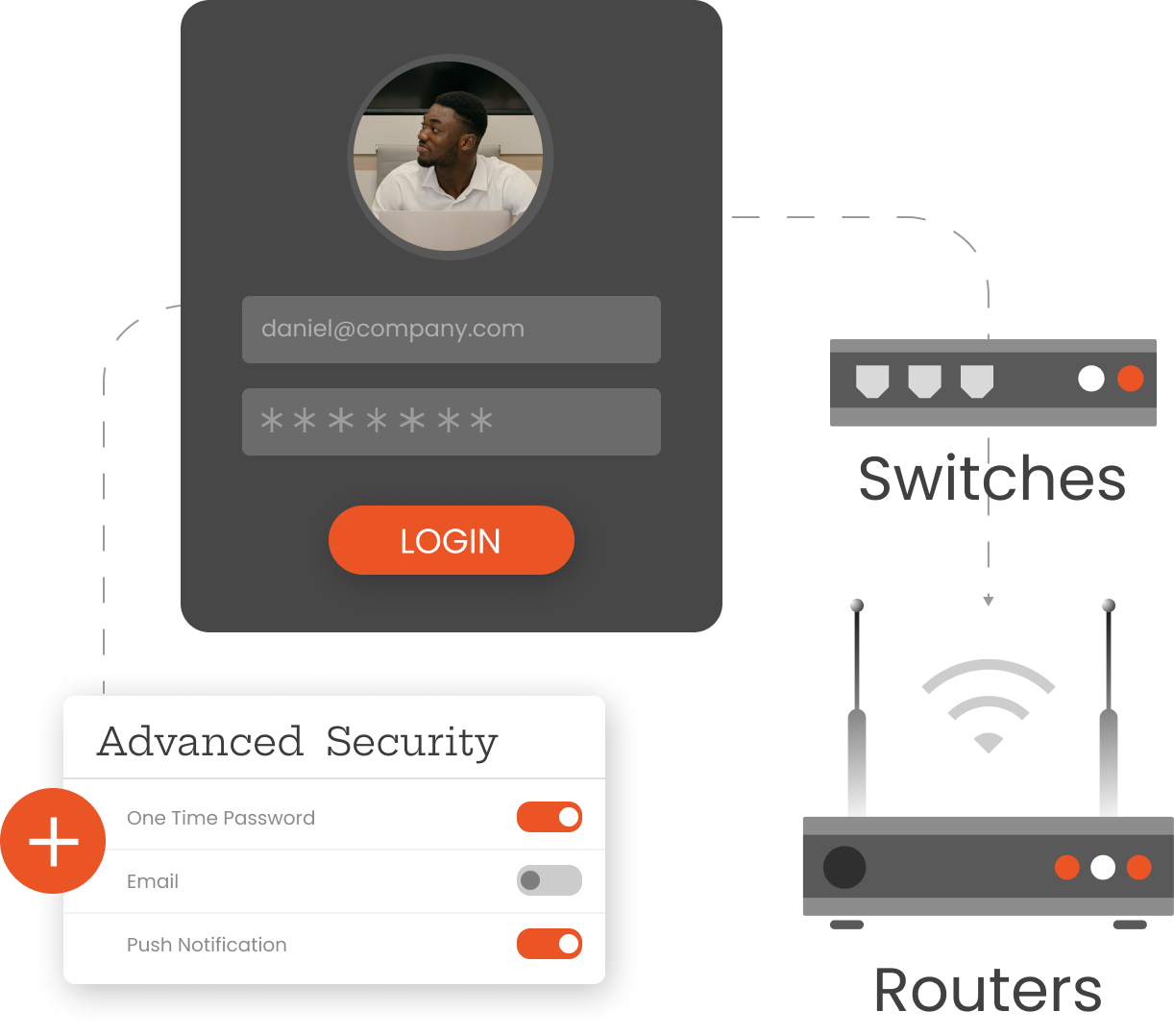
Implement MFA security for firewalls, switches, routers, and other network devices with the miniOrange MFA solution that extends beyond VPNs, and fortifies your entire corporate network. Leverage Radius & TACACS protocols with miniOrange to encrypt switches and routers based on your network's hardware capabilities and add Multi-Factor Authentication to enhance the security posture.
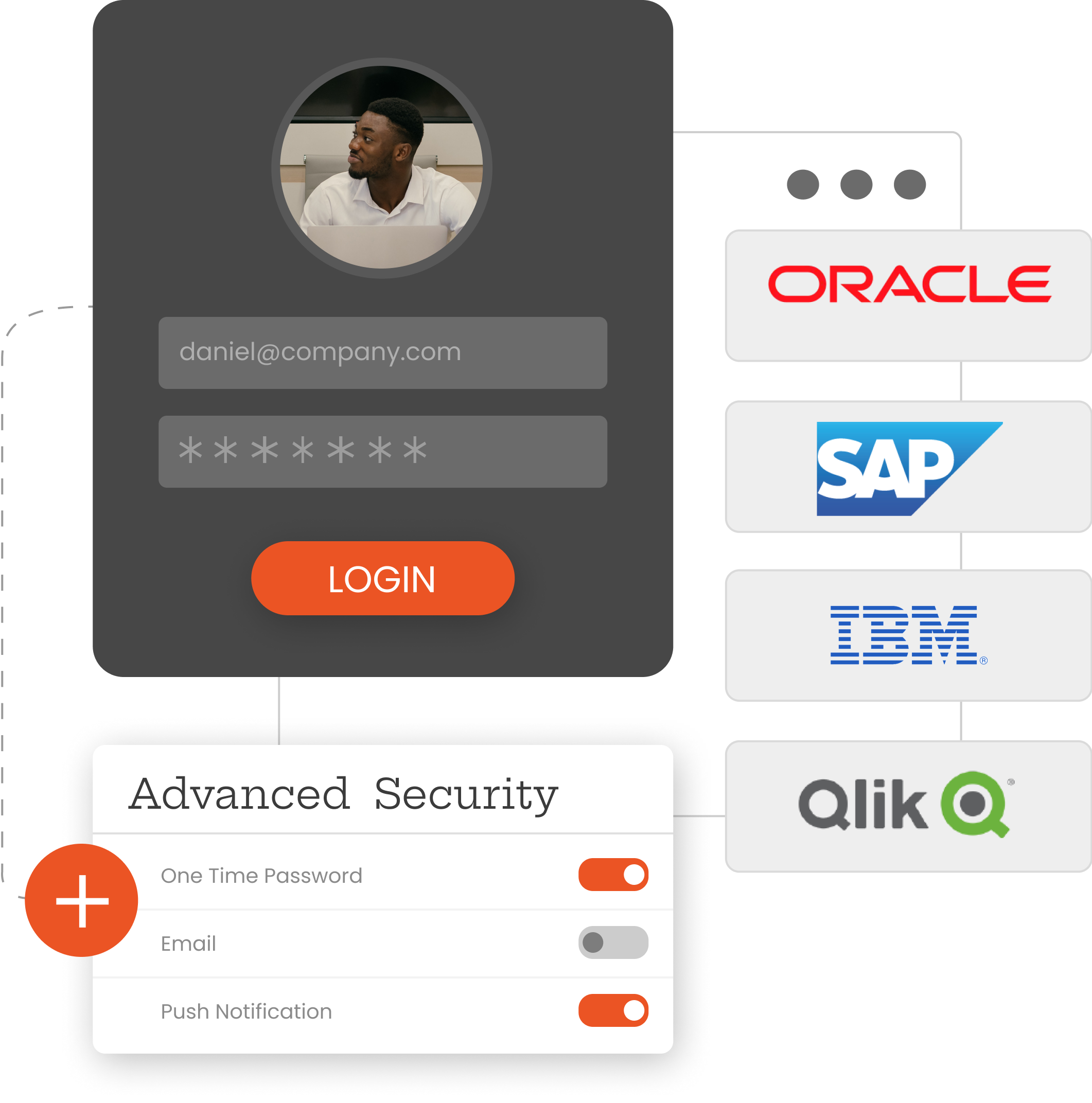
Safeguard valuable historical data and meet compliance requirements with MFA services and secure legacy applications like Oracle EBS, QlikView, PeopleSoft, & Siebel CRM. Our advanced Multi-Factor Authentication solution seamlessly integrates with these legacy systems, delivering modern security without operational disruptions.








Identity solutions from miniOrange can be easily deployed in your organization's existing environment.
Implementing MFA Security boosts trust among employees, customers, and partners by preventing unauthorized access and ensuring privacy protection.
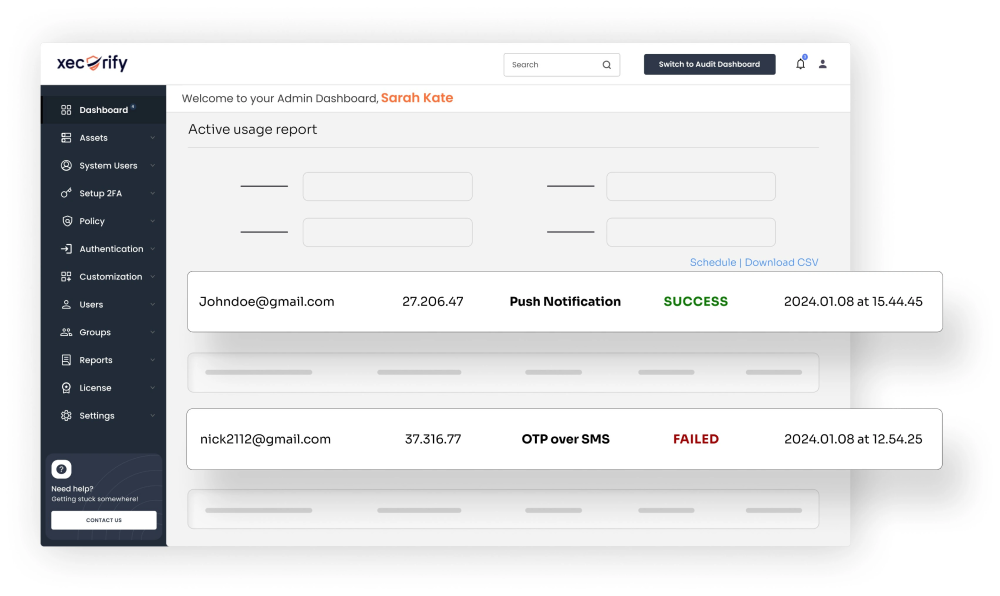
MFA reduces security breaches and IT helpdesk calls by removing password-related vulnerabilities, hence, minimizing the workload on security teams.
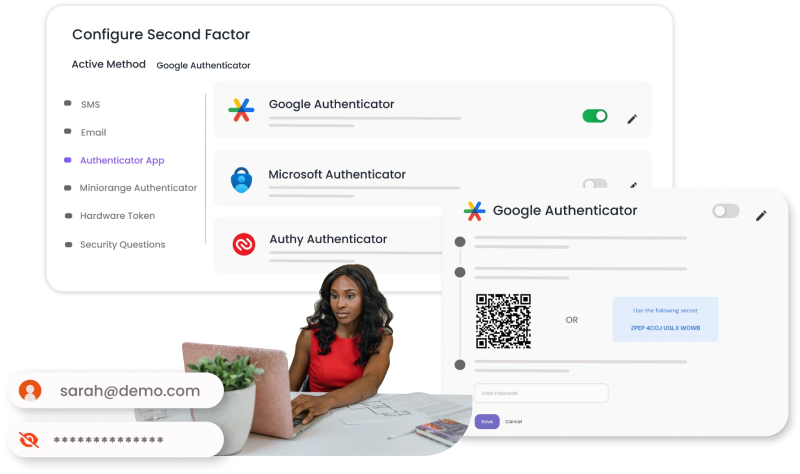
Make login flexible and easy for your users with 15+ MFA methods to choose from. Custom MFA policies improve user productivity along with robust security.
Yes, our solution supports external and in-house SMS or Email gateways as well. We also have our own miniOrange gateway, which you can leverage in case you don’t have any existing gateway.
In the miniOrange dashboard, admins can modify existing email templates or add a custom email template for the Email verification method. You can personalize the user experience with your branding on login pages, email templates, etc.
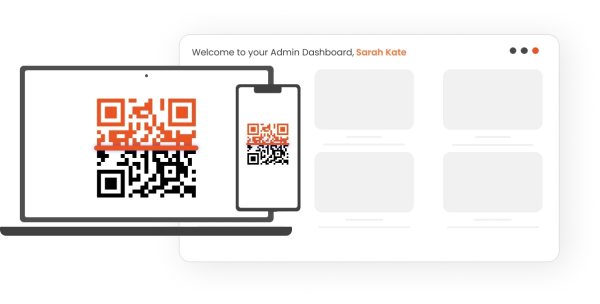
Admins can easily set up 2FA methods during user onboarding from the 15+ MFA methods supported by miniOrange. You can also prompt users to set up 2FA during their first login. The 2FA methods for different users or user groups can be easily managed from the miniOrange dashboard.
If your organization is using an in-house authentication mechanism or any third-party authentication system, then miniOrange can enable MFA using custom connectors which can work smoothly with your existing authentication setup.
Knowledge Factor (something you know): Knowledge factors include multiple passwords, PIN codes, and answers to security questions. Anything you can remember, type, say, do, execute, or otherwise recall when needed is considered a knowledge element.
Possession Factor (something you have): This factor suggests that you possess a particular physical object that a hacker would not acquire. This category includes smart cards, mobile phones, physical tokens, key fobs, and keychains.
Inherence Factor (something you are): The Inherence factor might include something that is a part of or unique to your physical body like a fingerprint, a retinal test, voice or facial recognition, or any other sort of biometrics. As the name suggests, it is something that a person inherits.
Identity, Access, and Beyond