Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
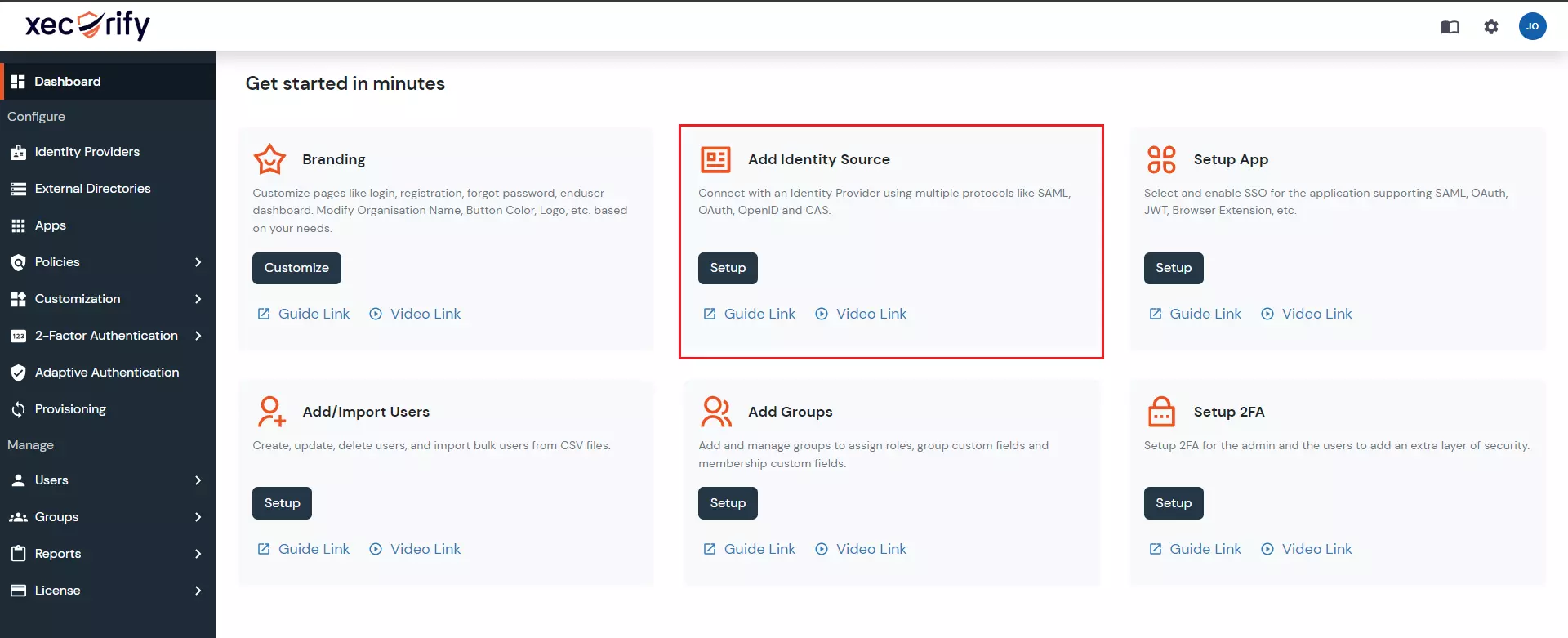
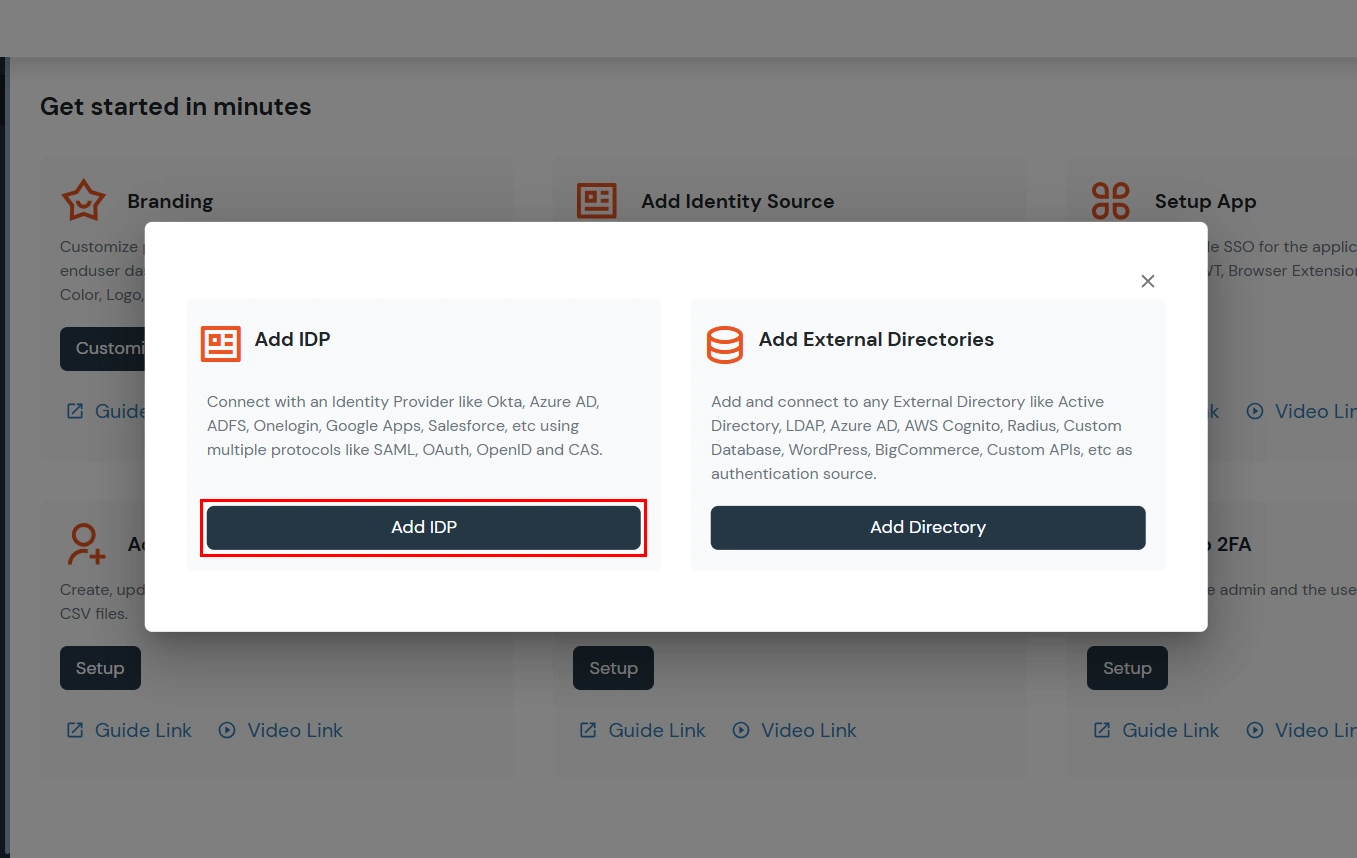
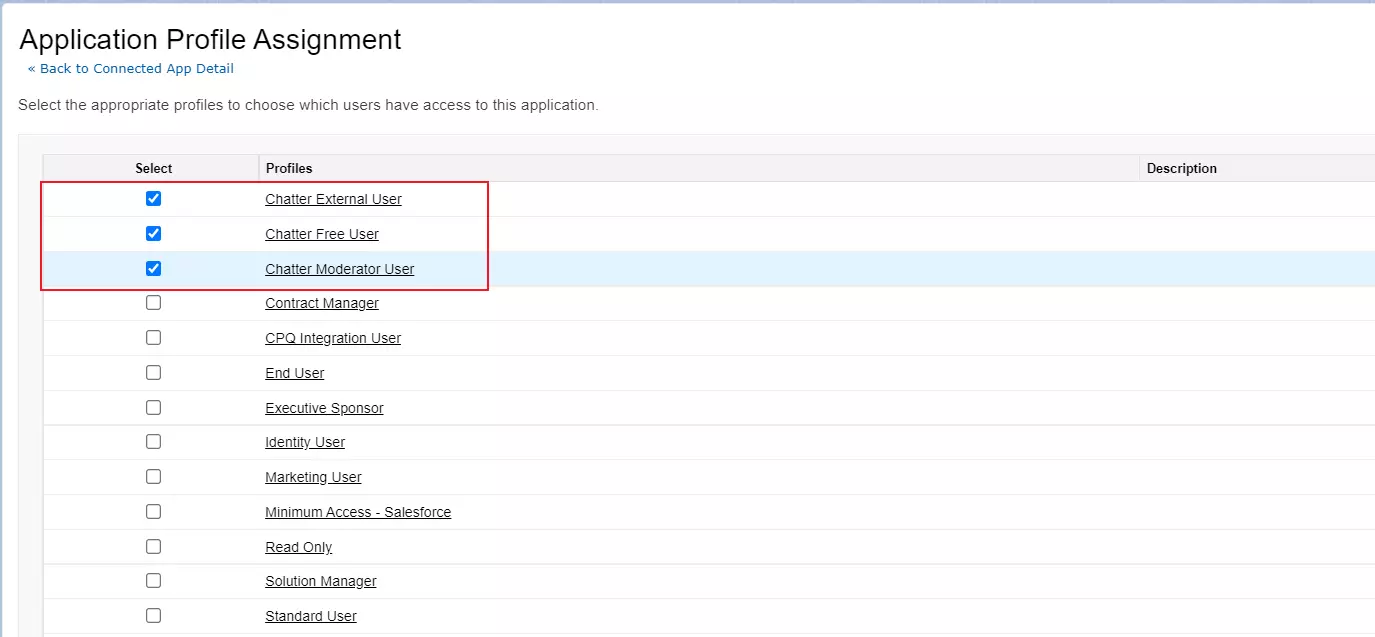
×Configure Salesforce as IDP to Single Sign-On (SSO) into multiple applications by loging using Salesforce as Identity Provider. Here, users can login to all applications (SPs) using their Salesforce login credentials by configuring Salesforce as an Identity Provider (IdP). miniOrange will act as an Identity Broker which forms a trusted connection between IDP and multiple SPs by enabling cross-protocol authentication. This provides easy and secure login access to users by using only one set of login credentials.
miniOrange offers free help through a consultation call with our System Engineers to configure SSO for different apps using Salesforce as IDP in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
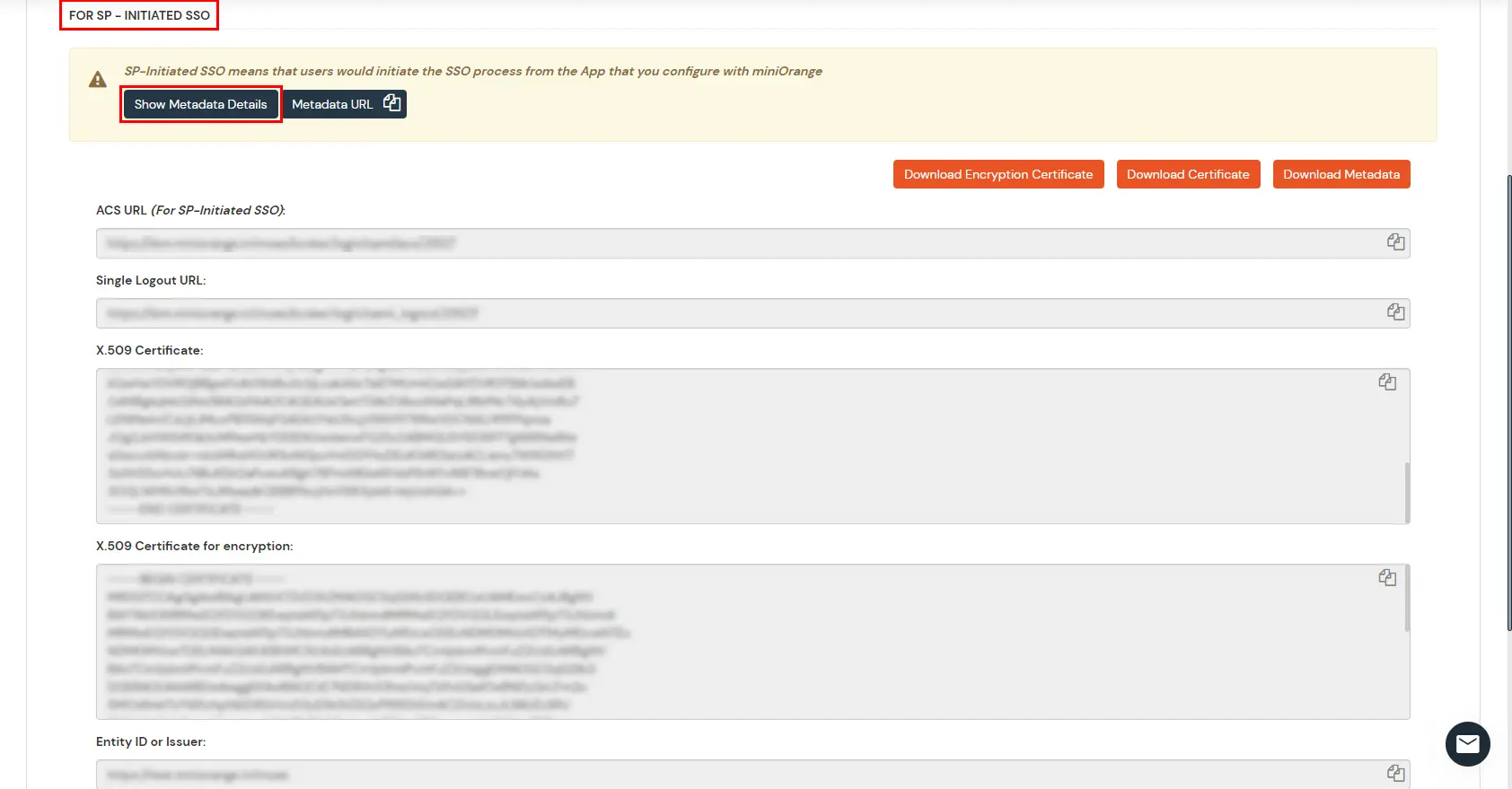
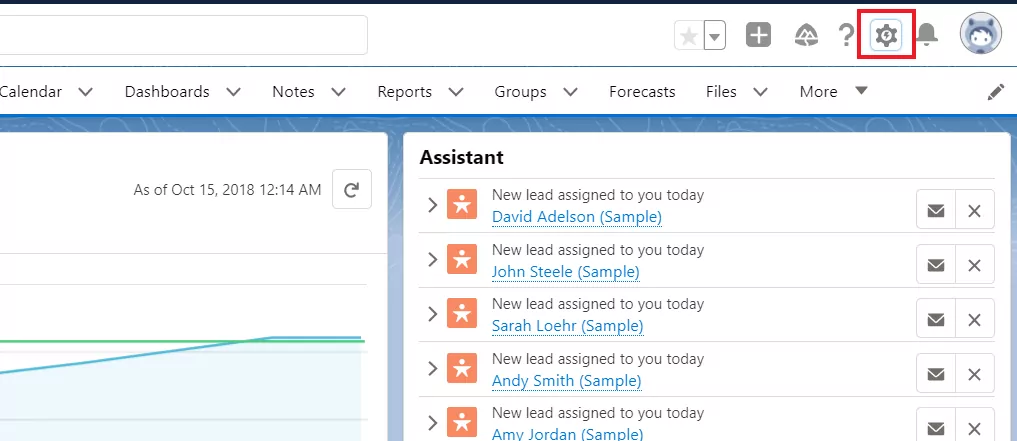
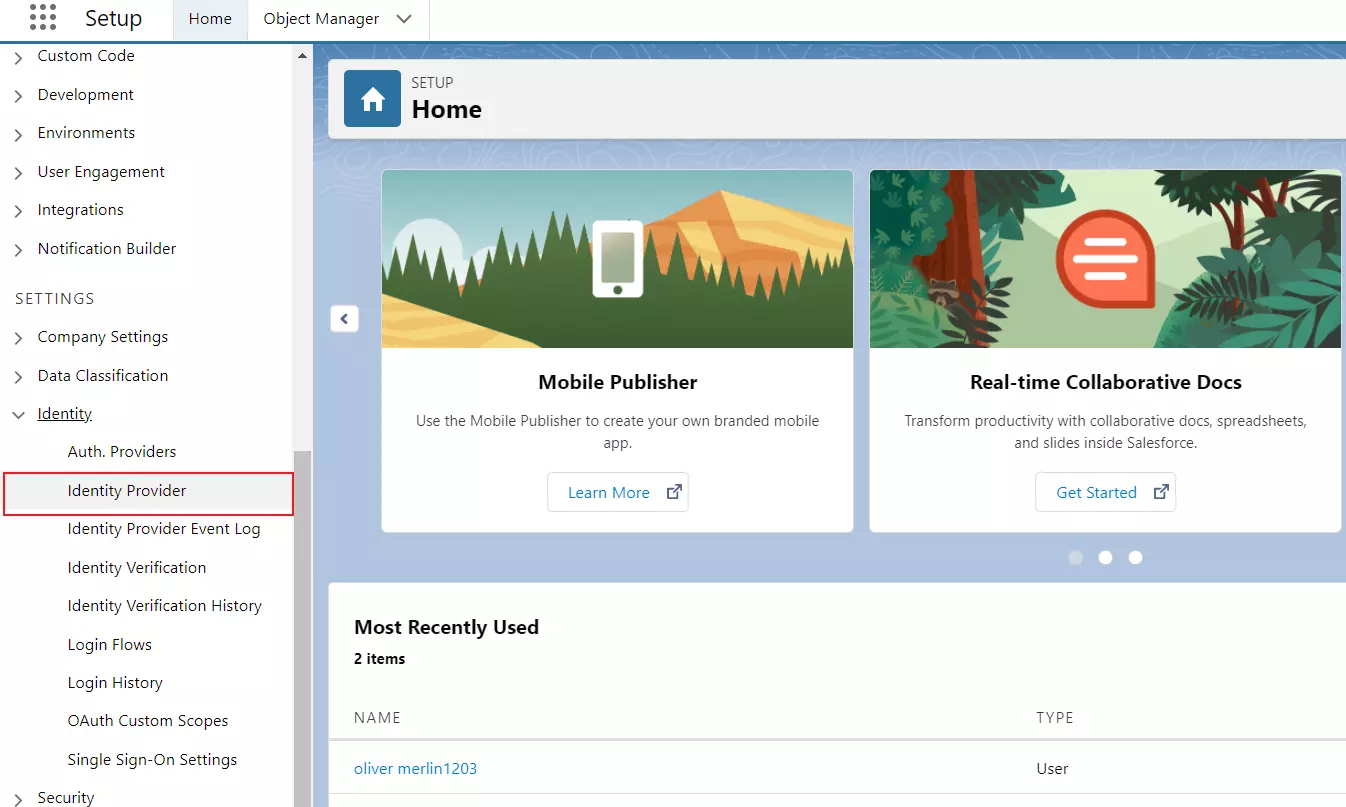
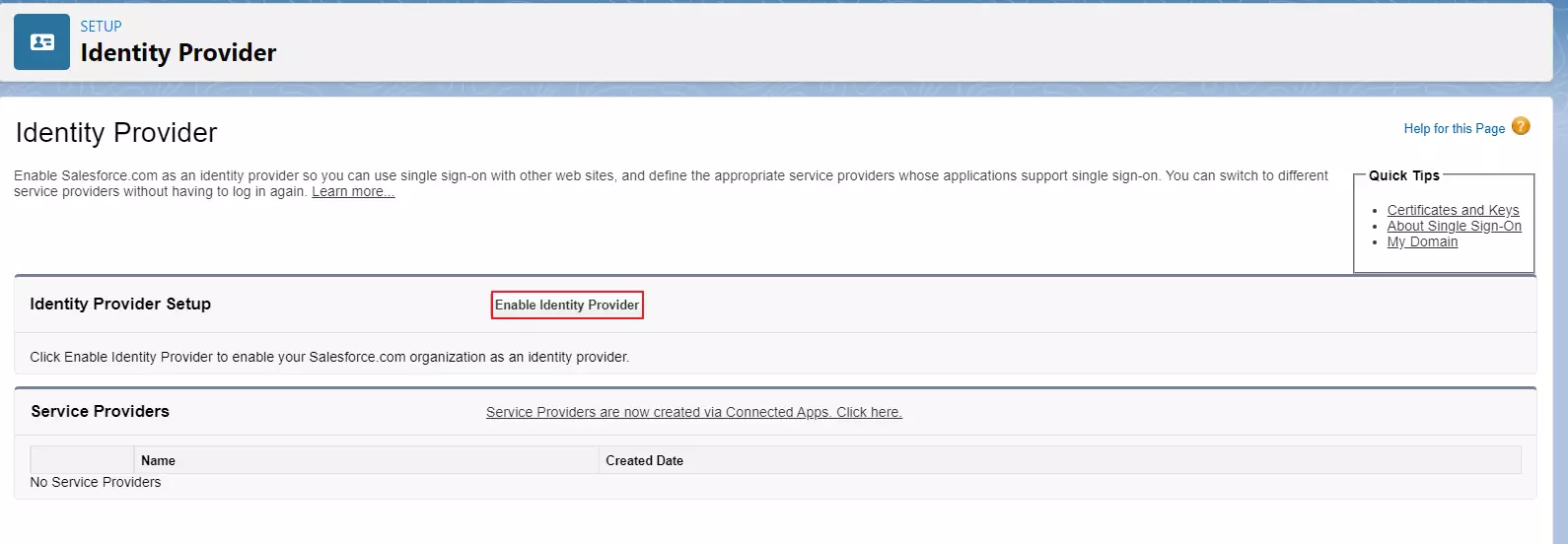
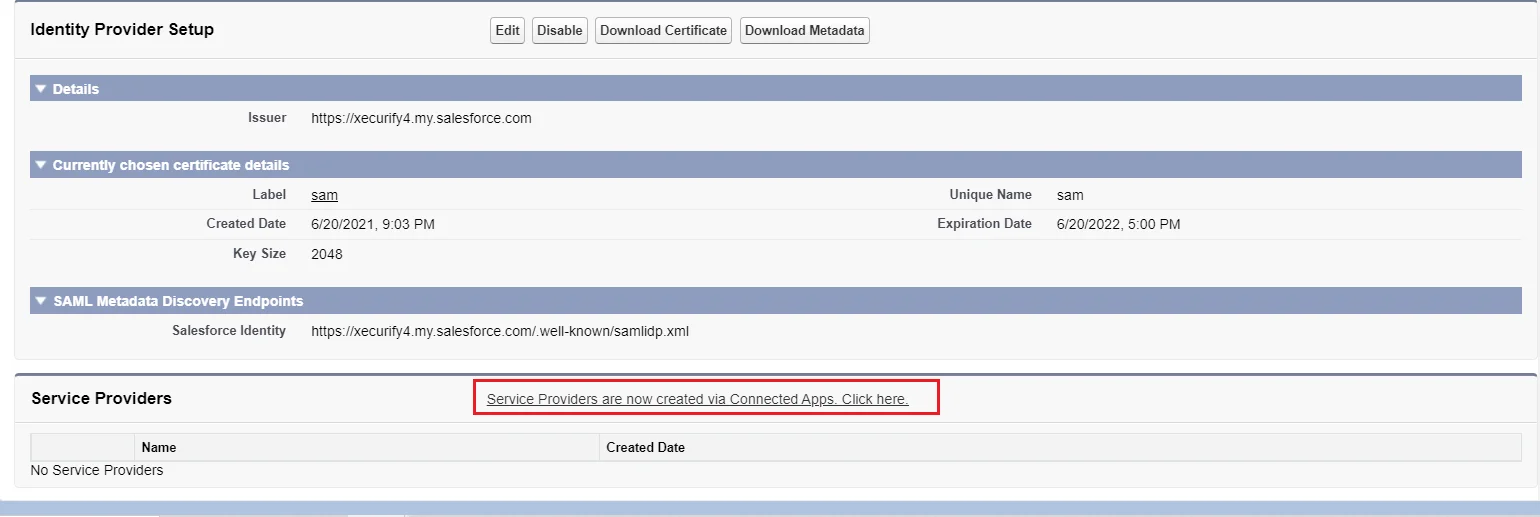
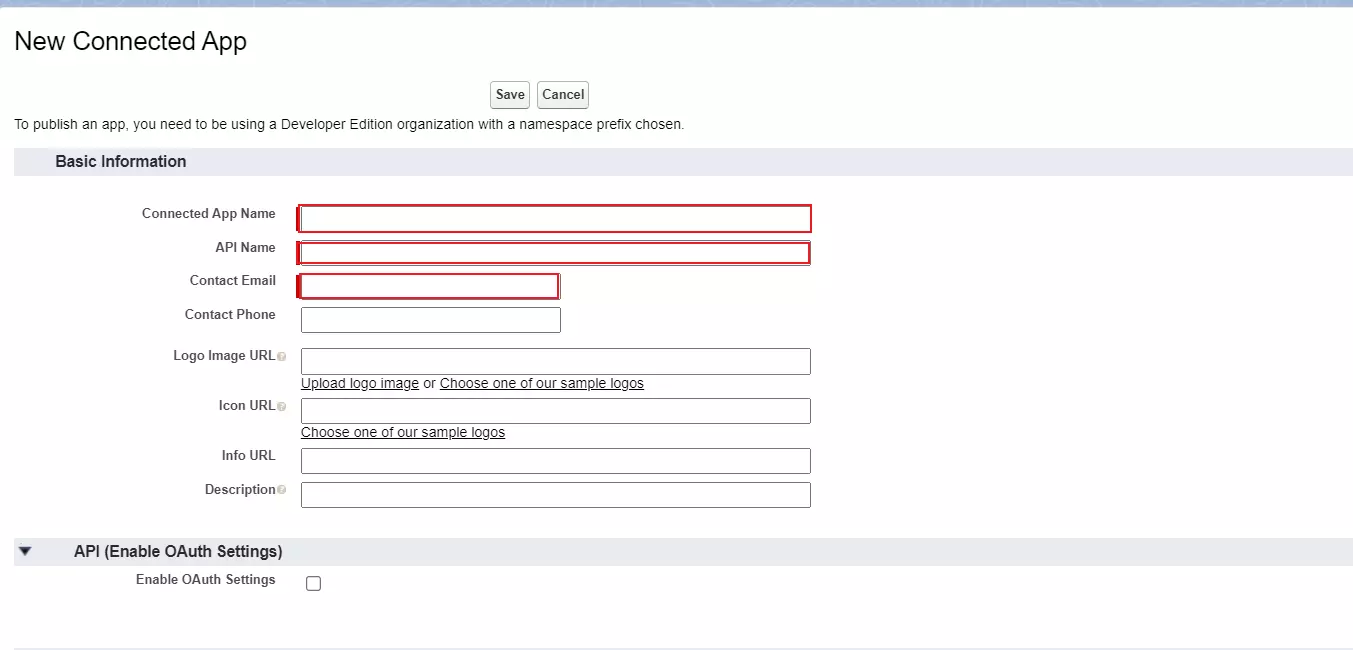
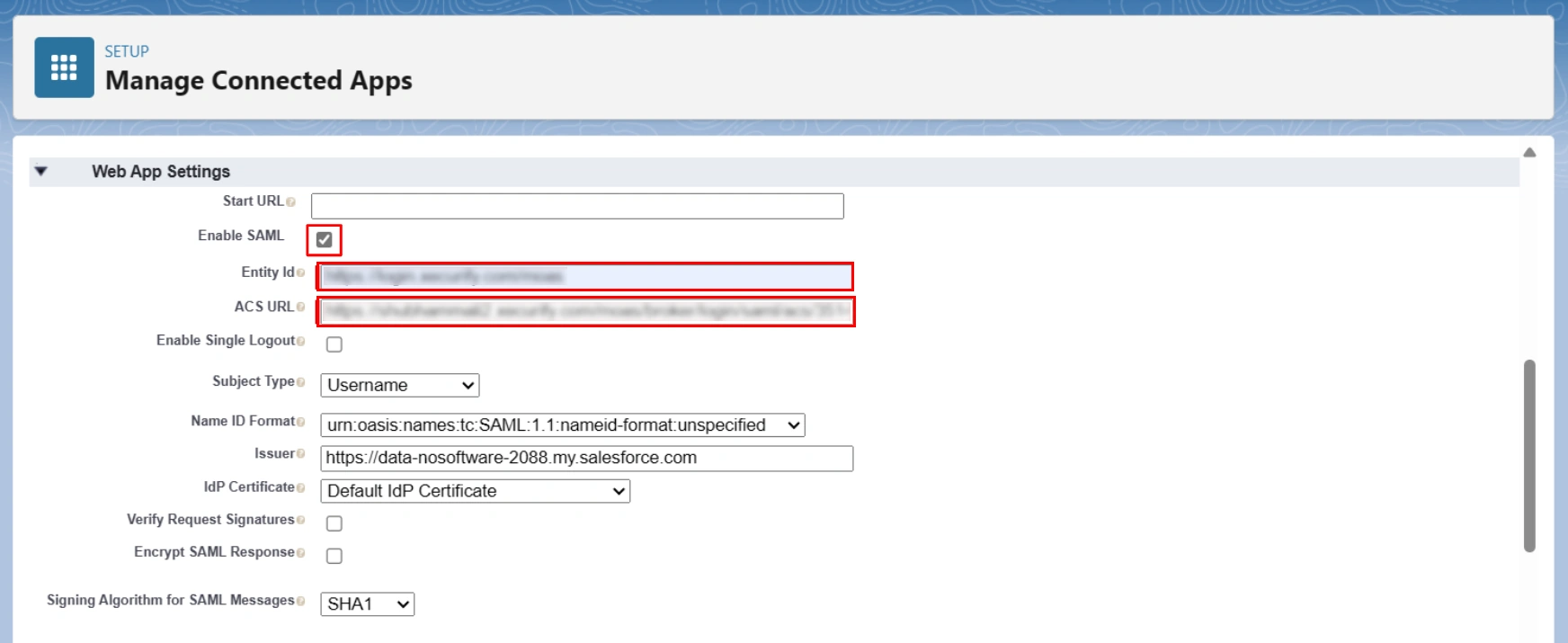
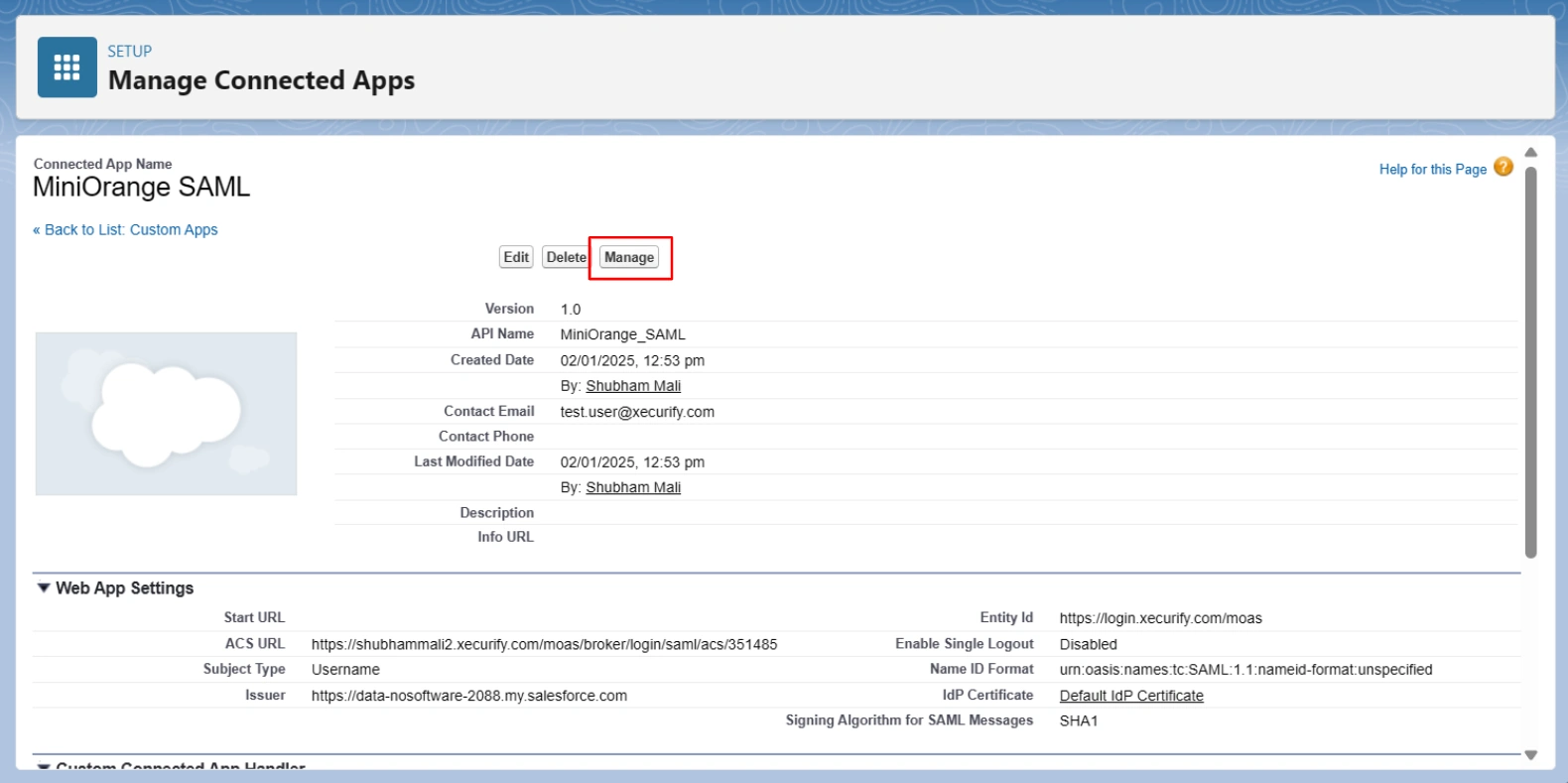
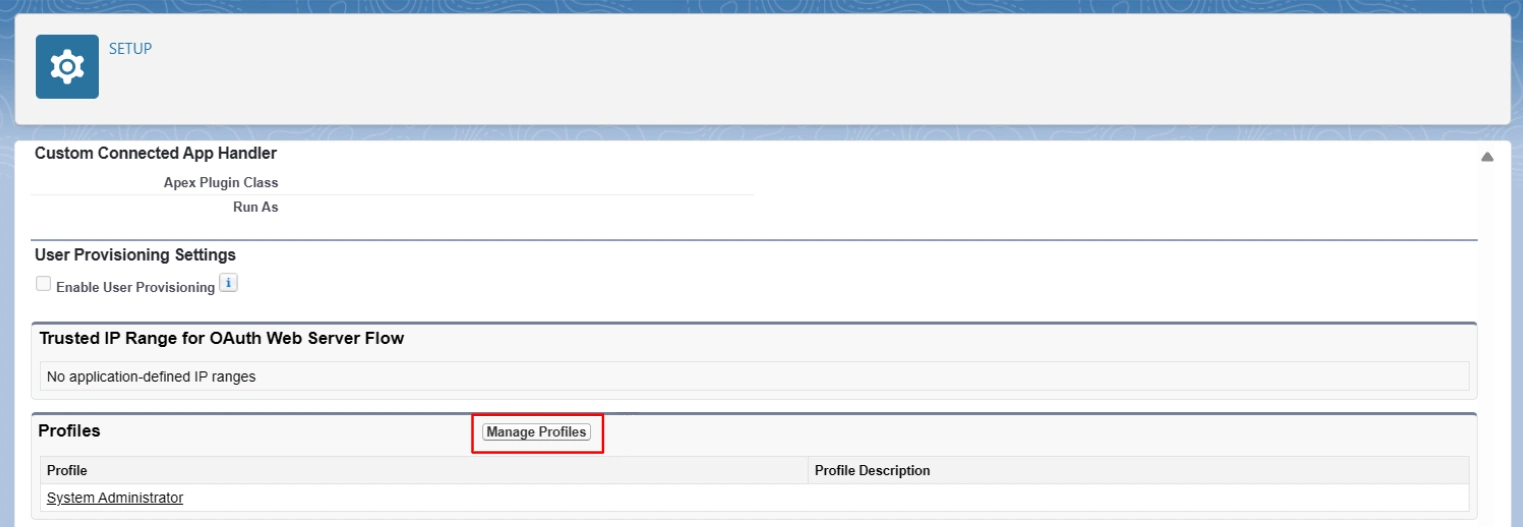
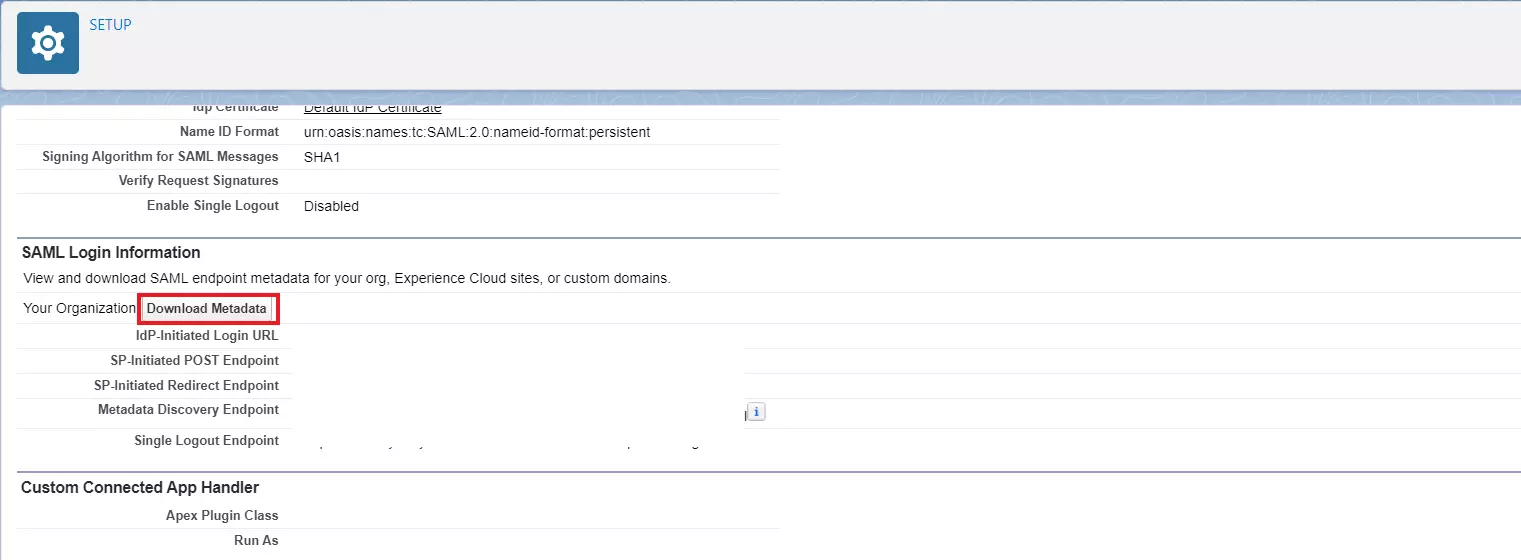
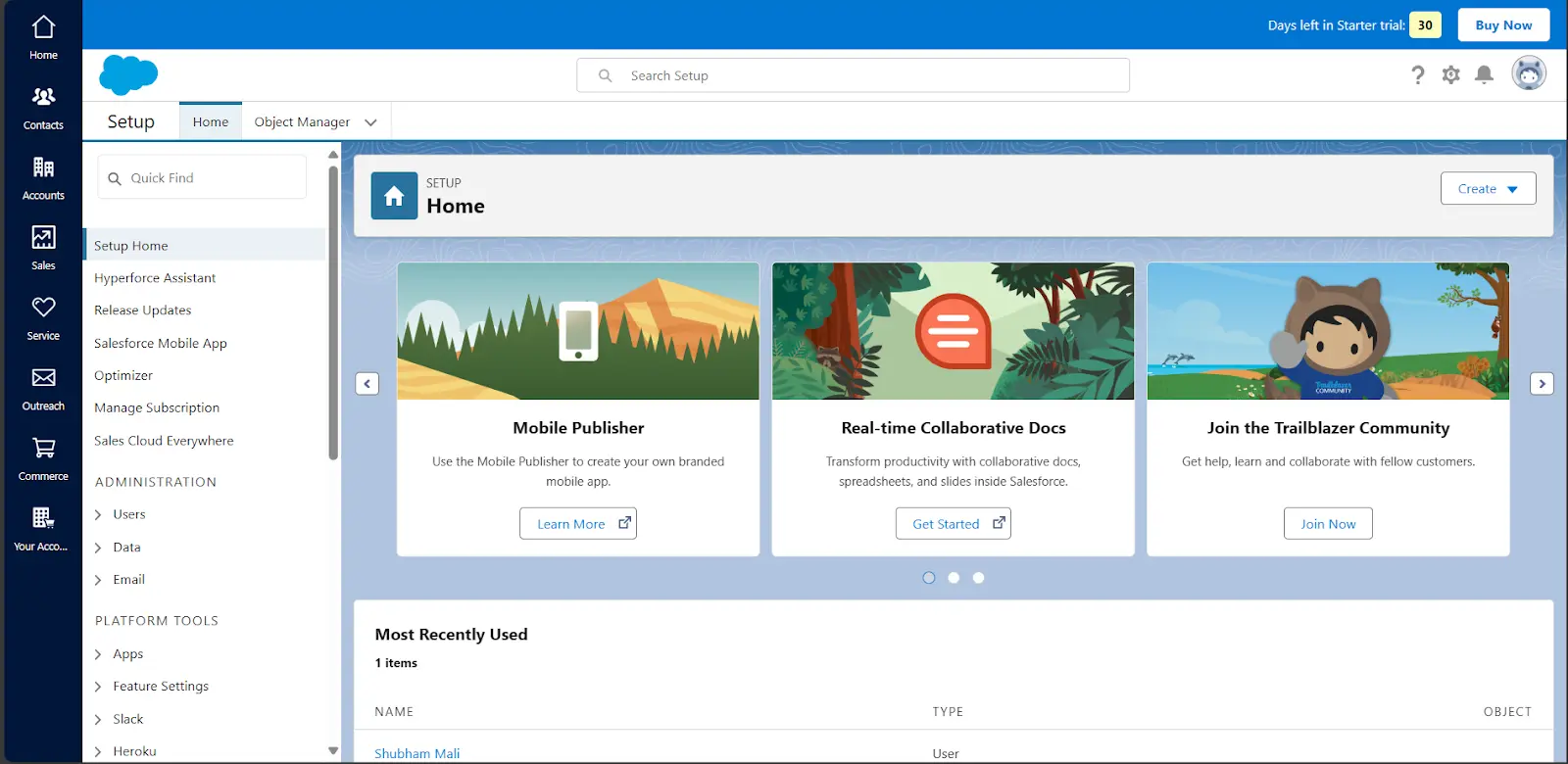
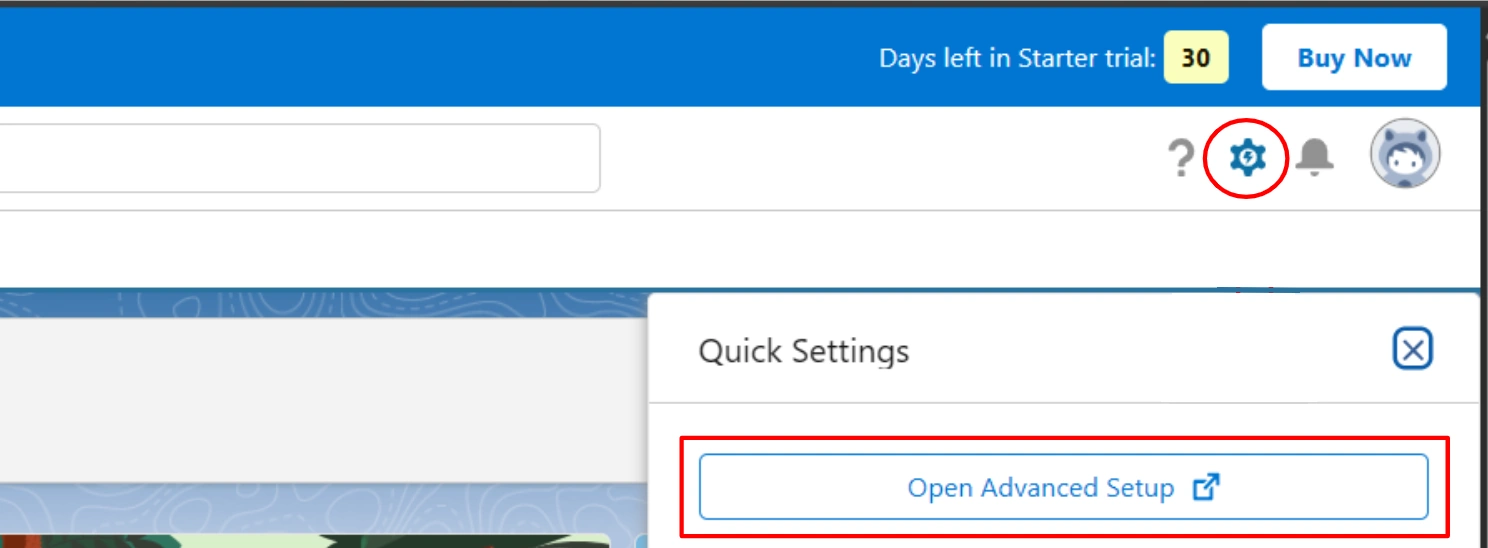
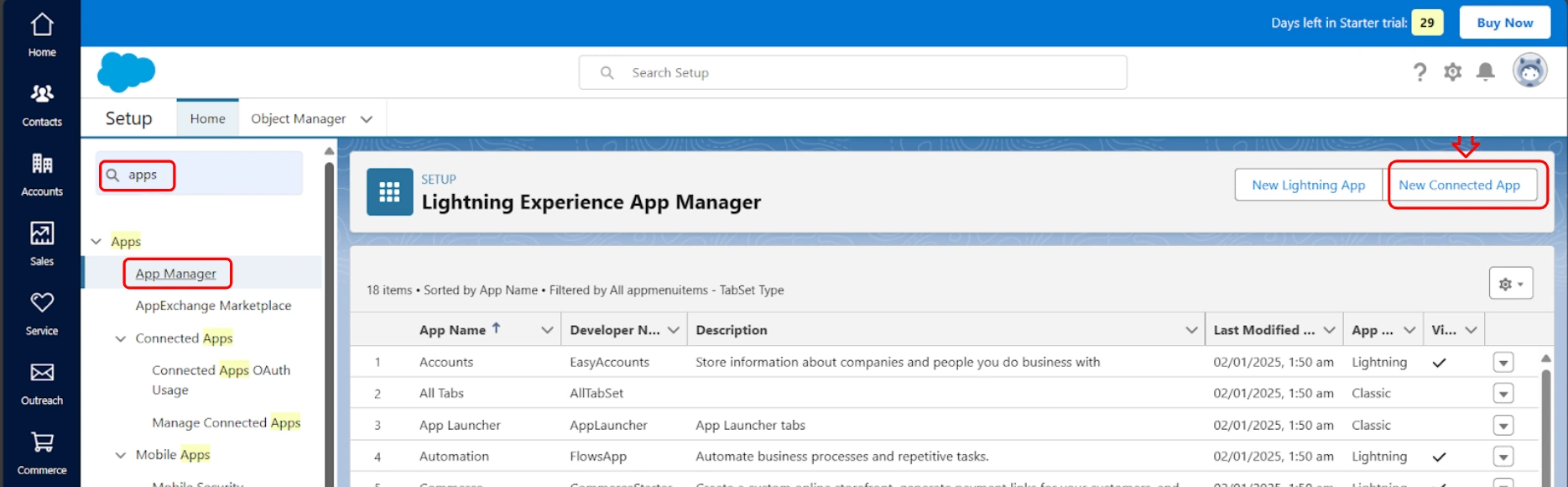
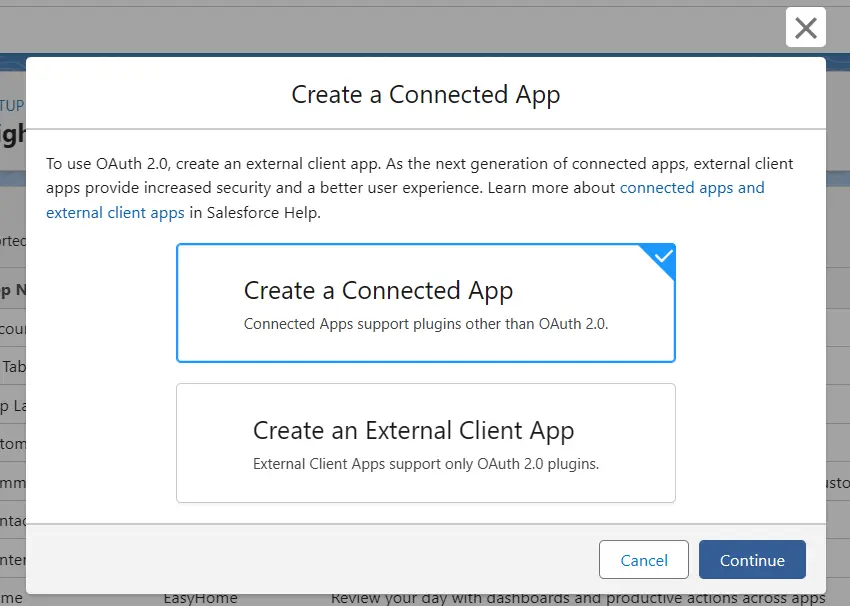
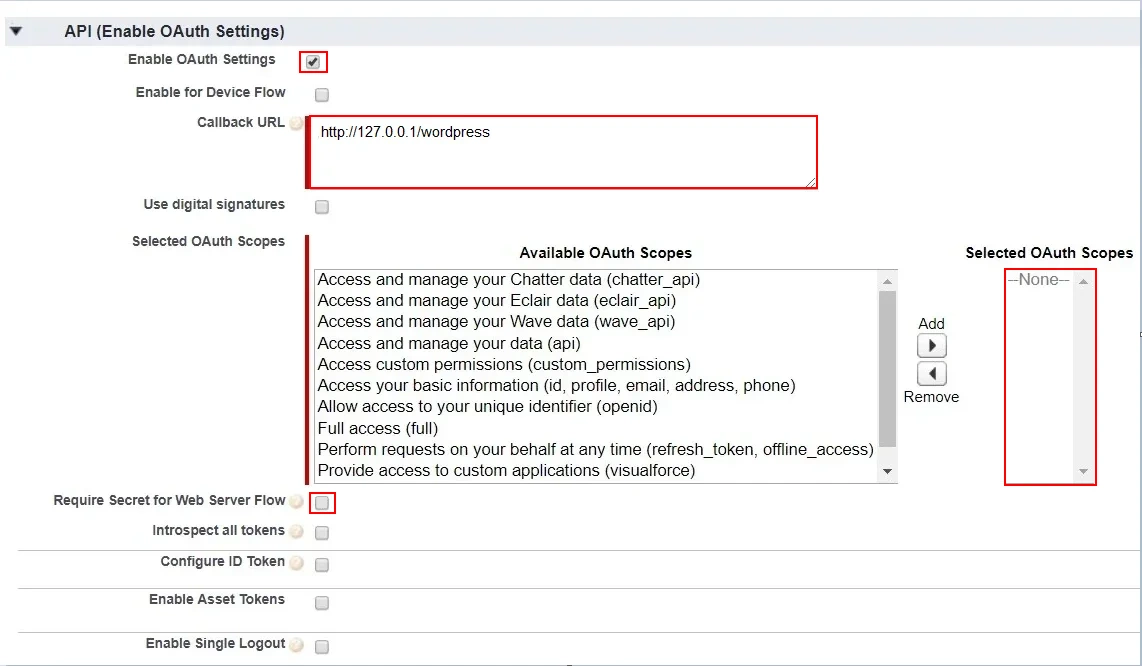
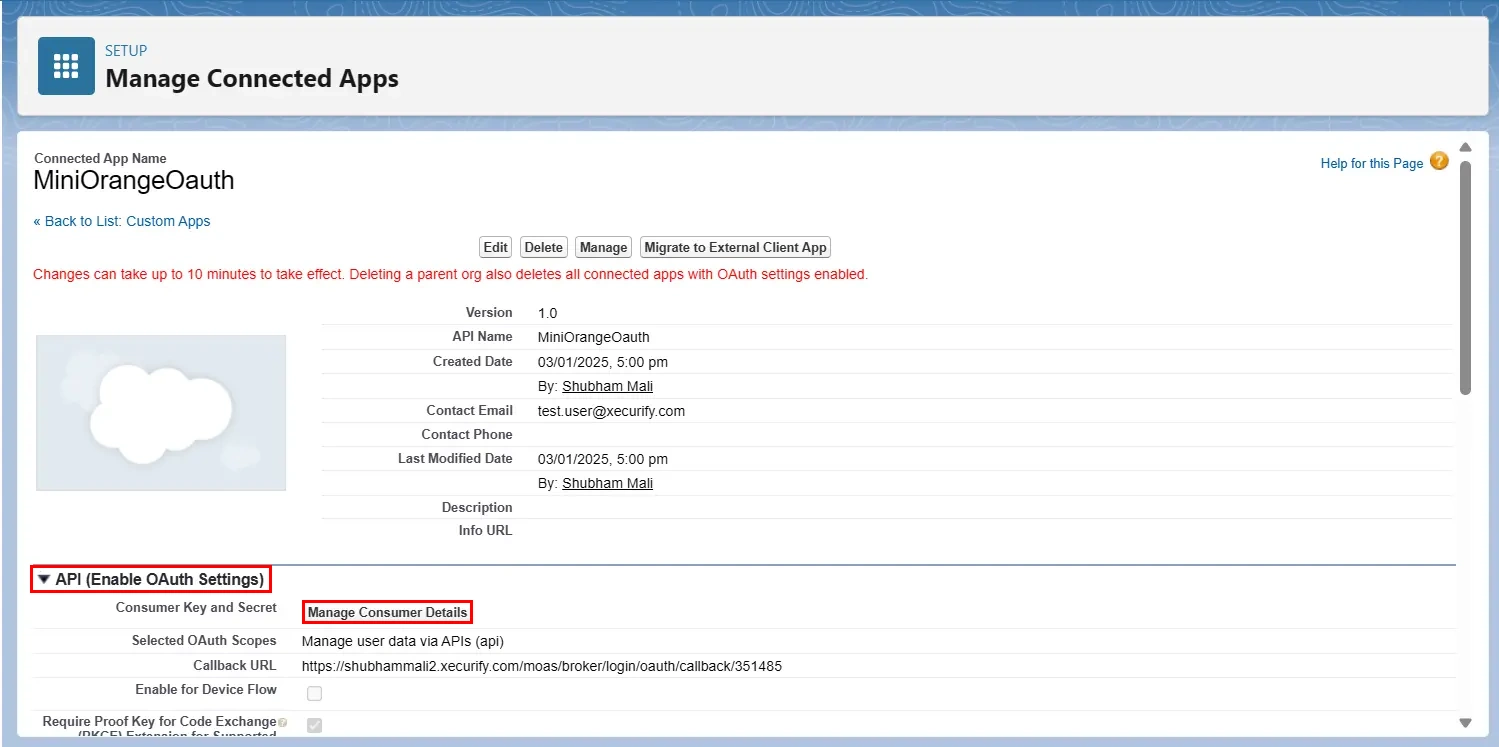
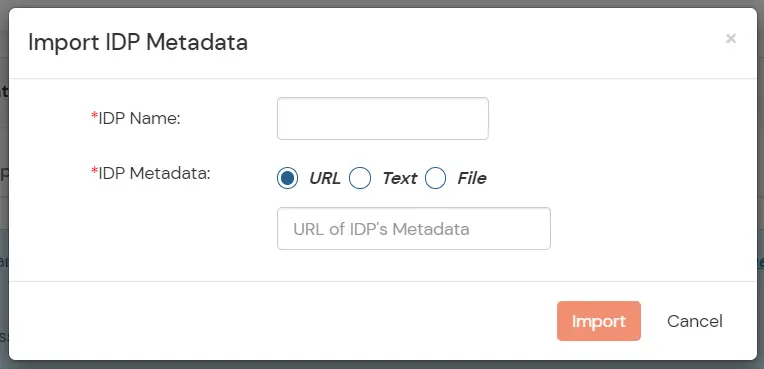
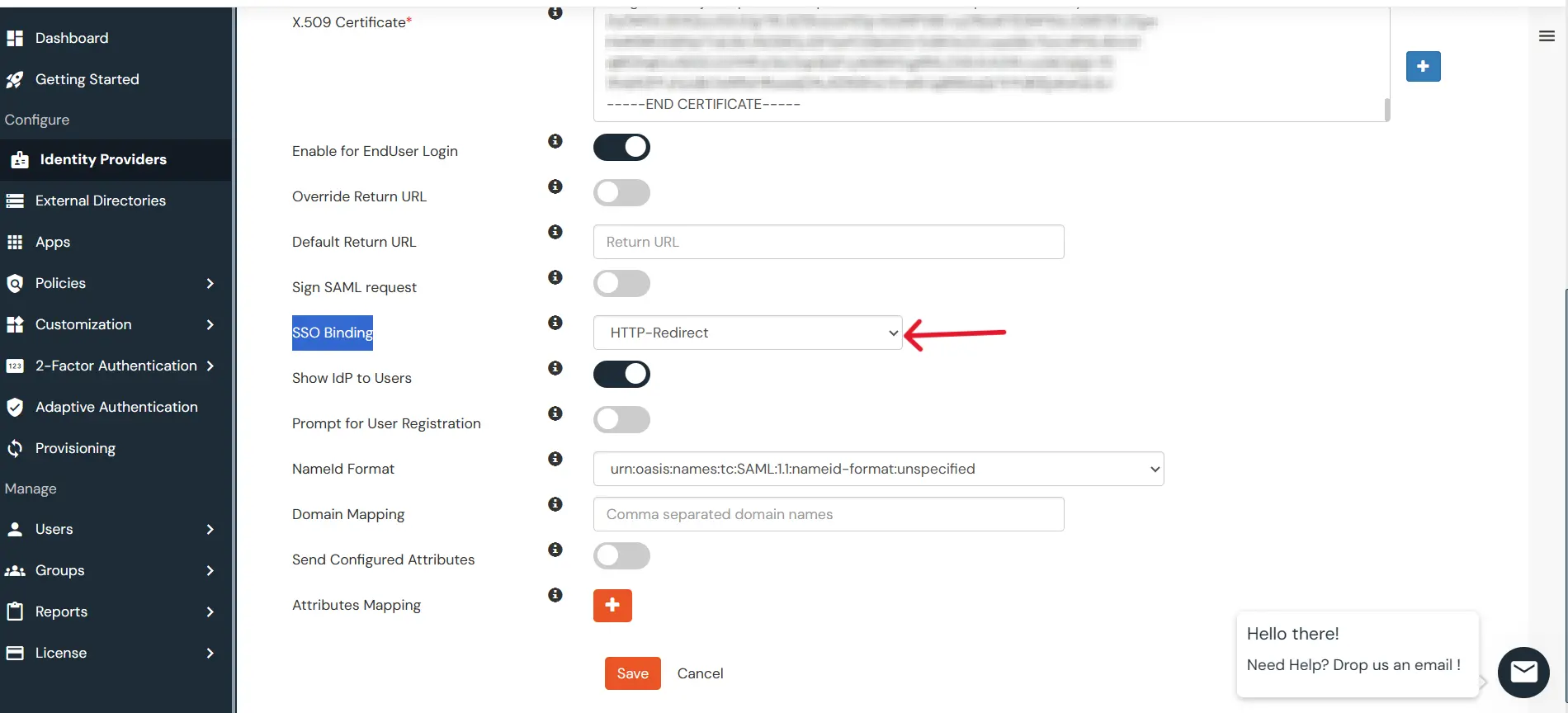
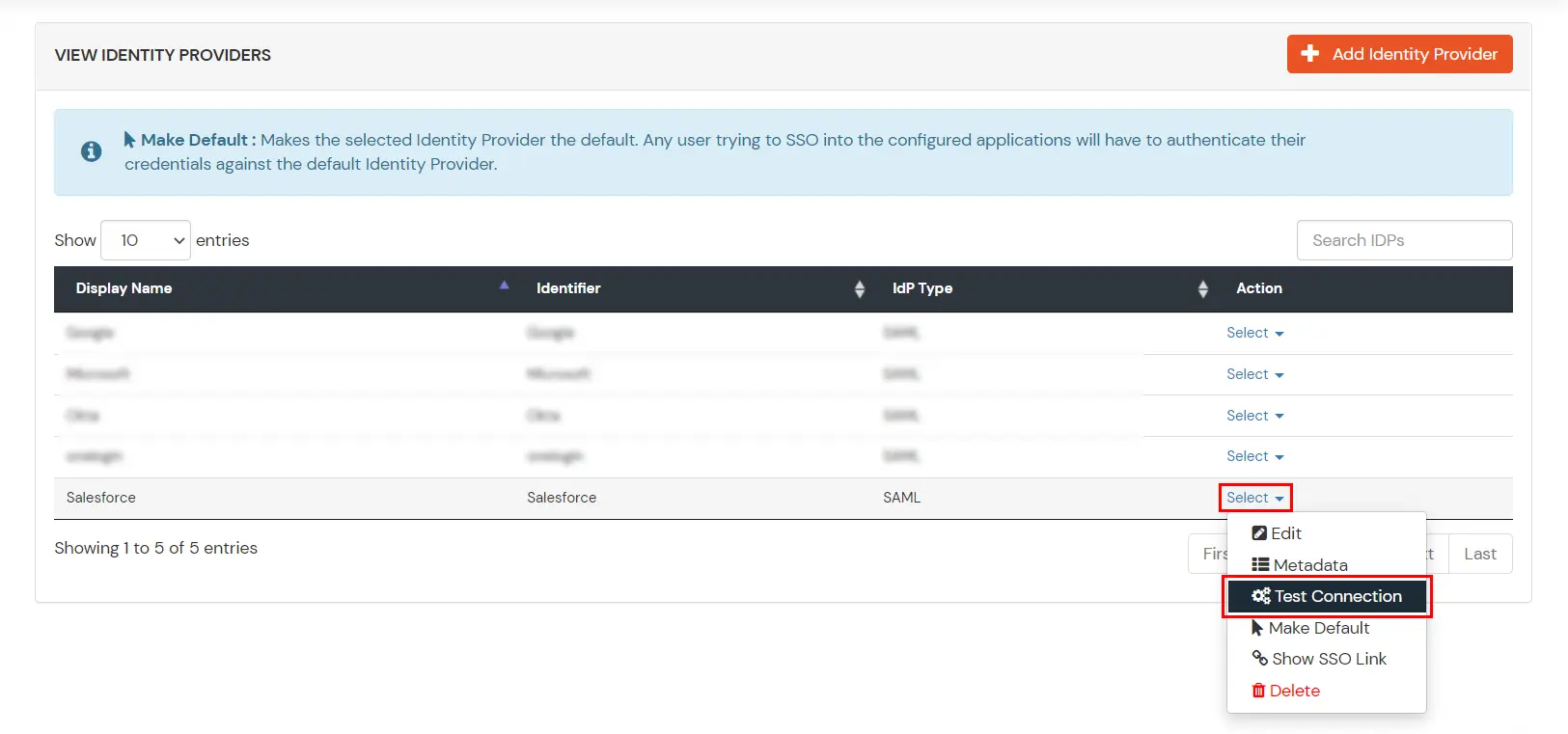
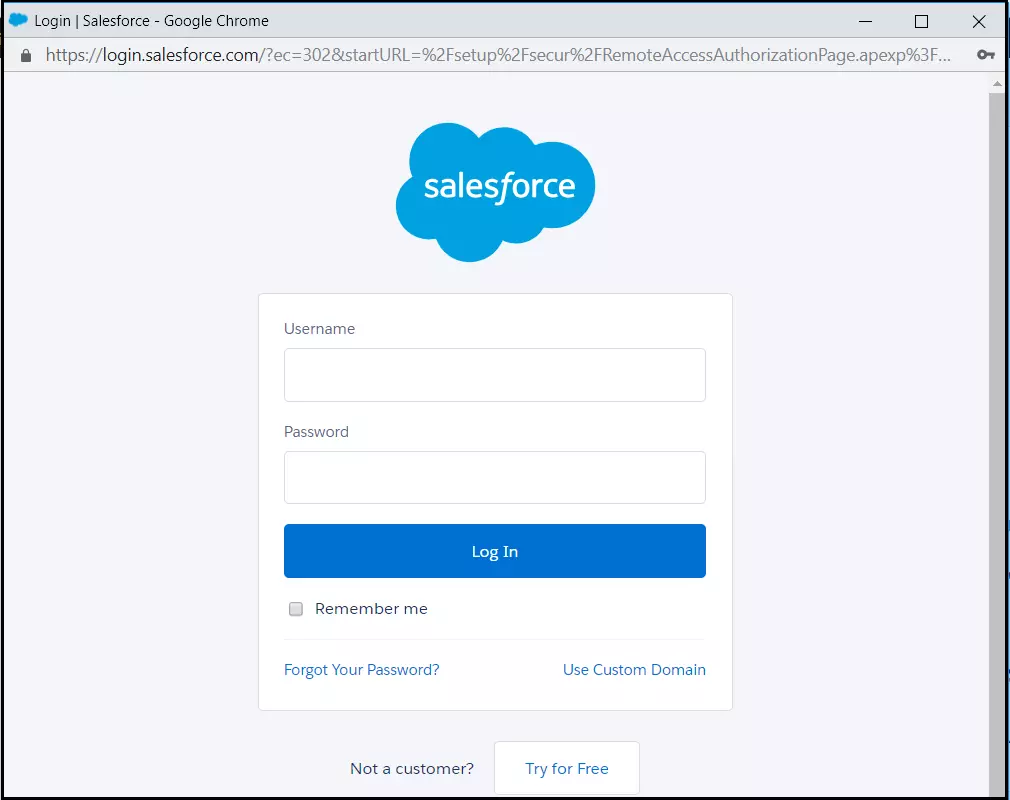
Mentioned below are steps to configure Salesforce as IDP via SAML and OAuth configuration. Follow the steps accordingly based on your requirement (SAML or OAuth).



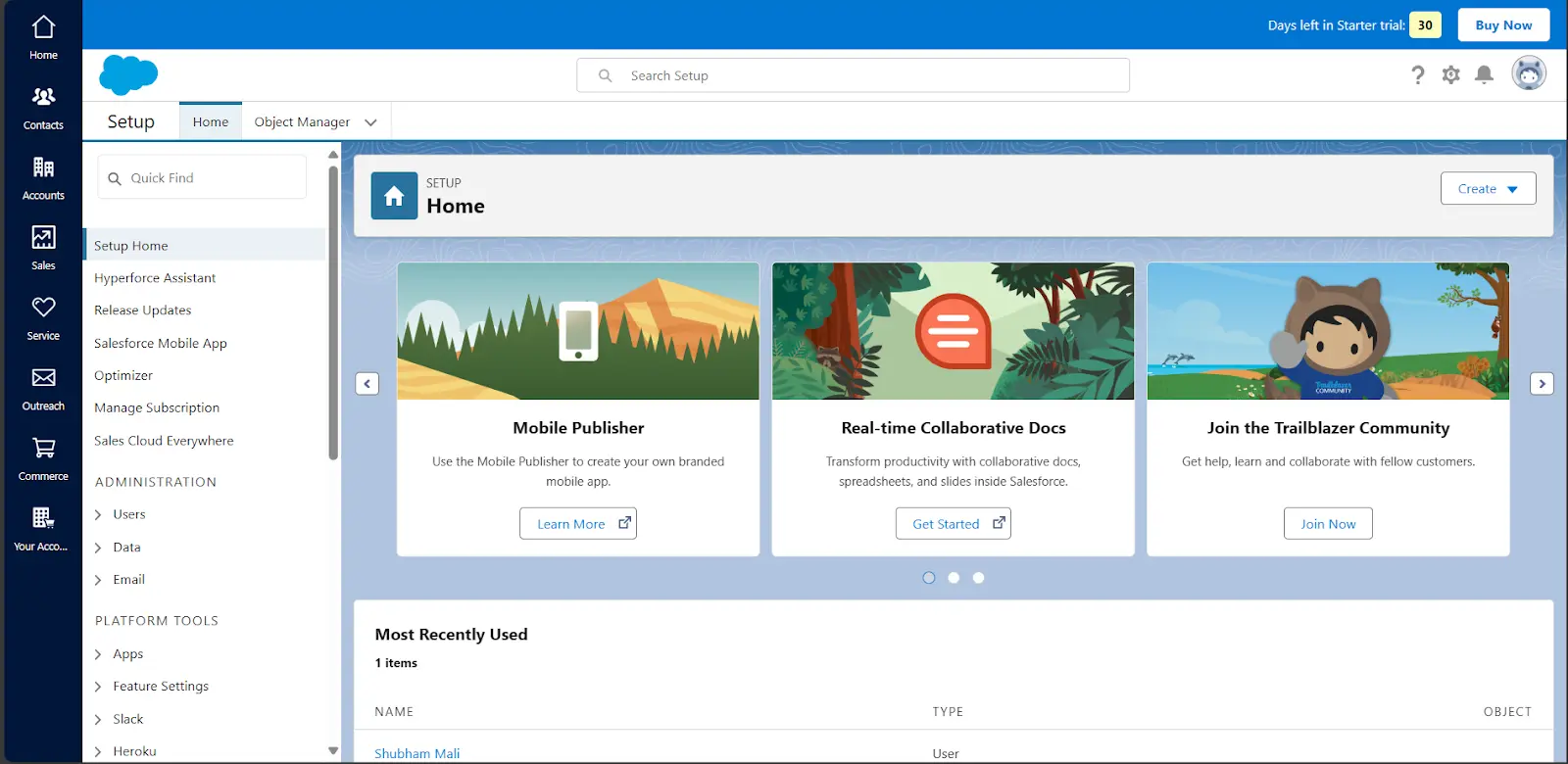
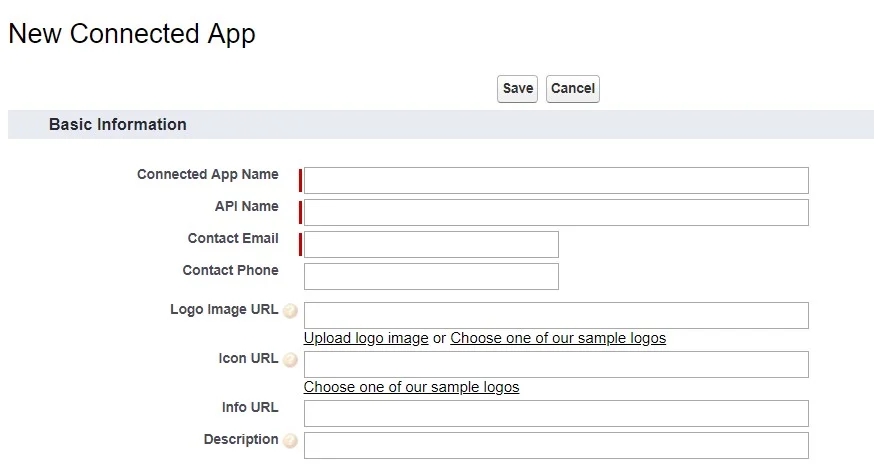

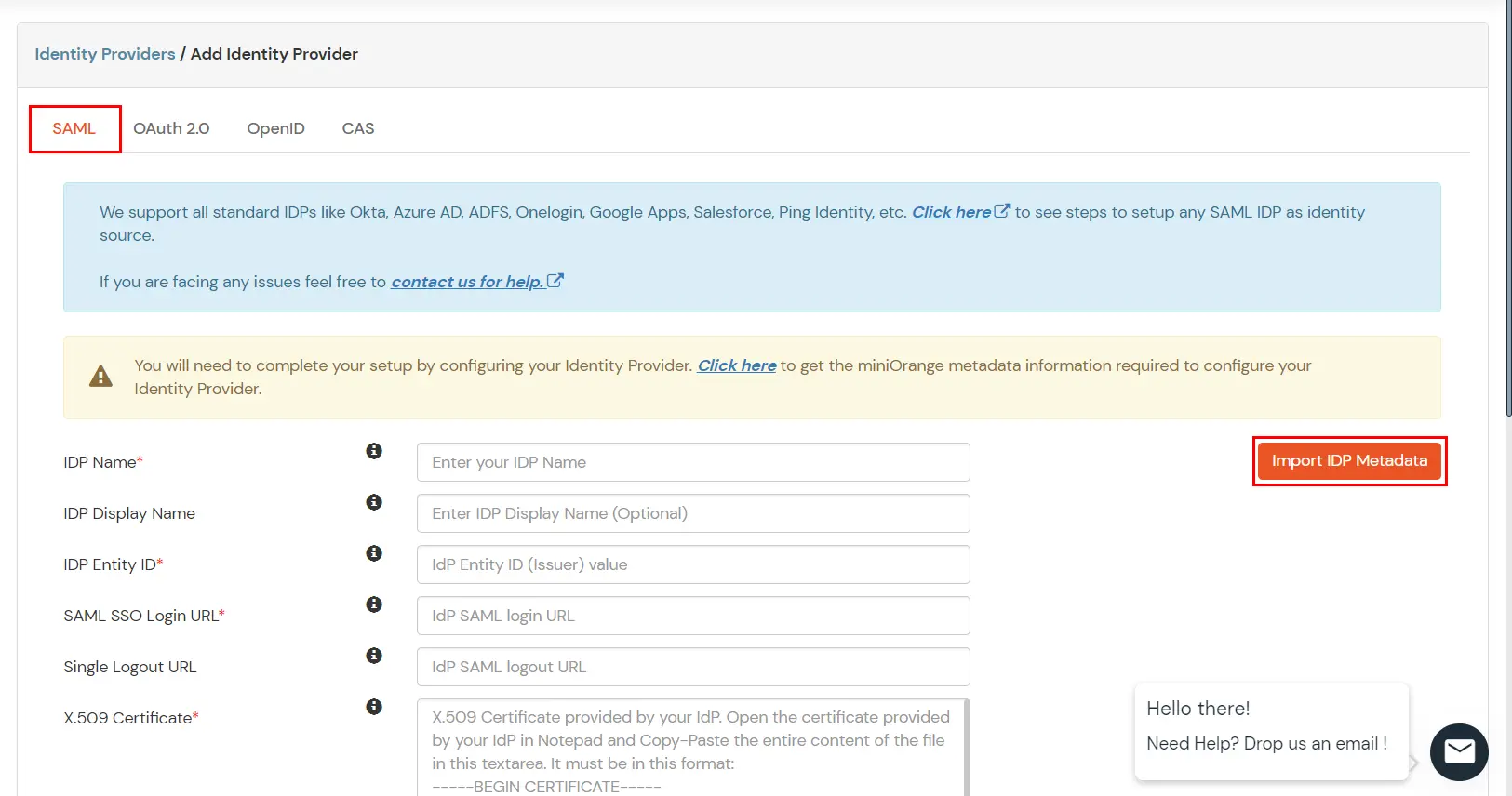

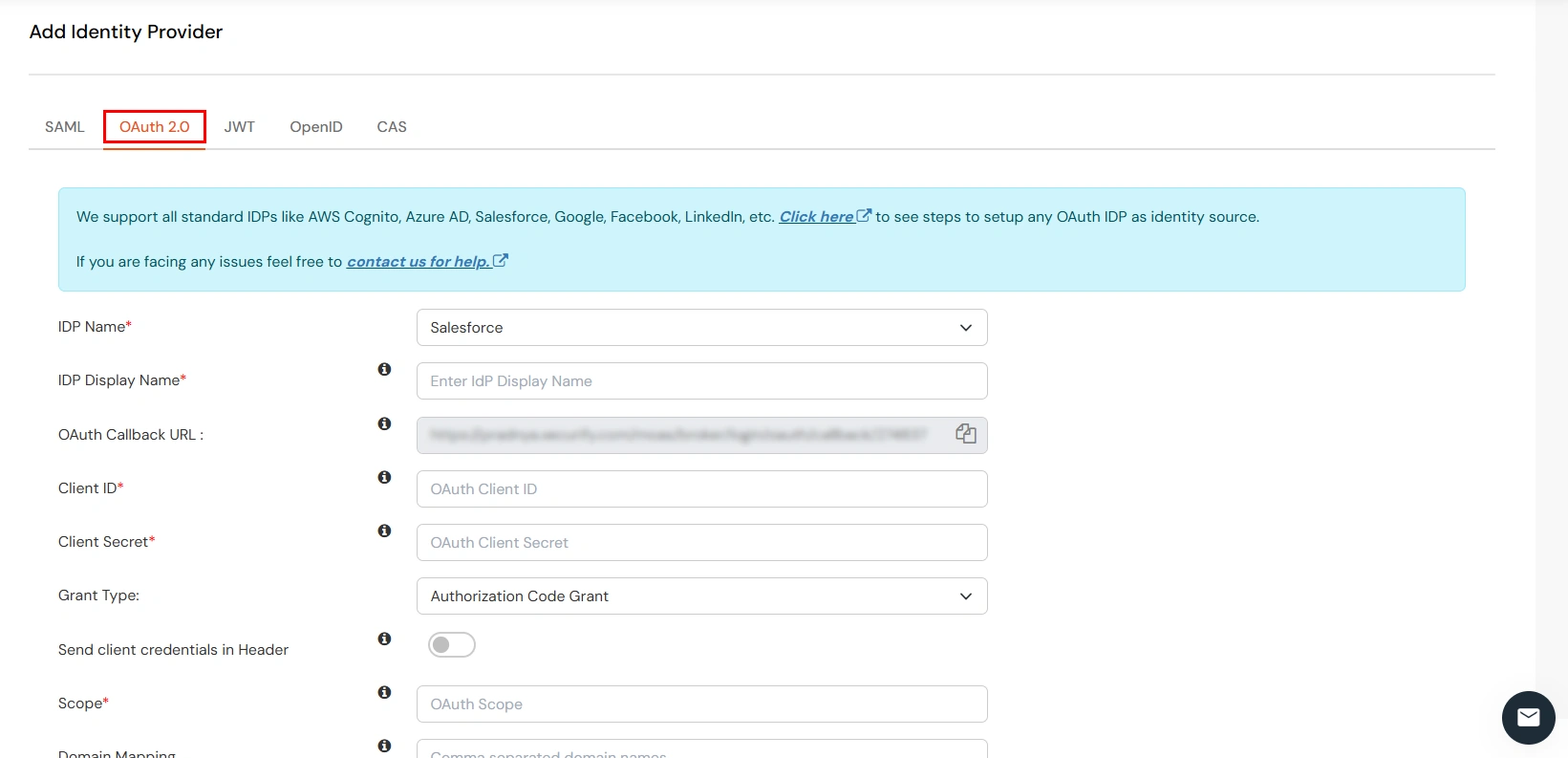
| IdP Name | Salesforce |
| IdP Display Name | Choose appropriate Name |
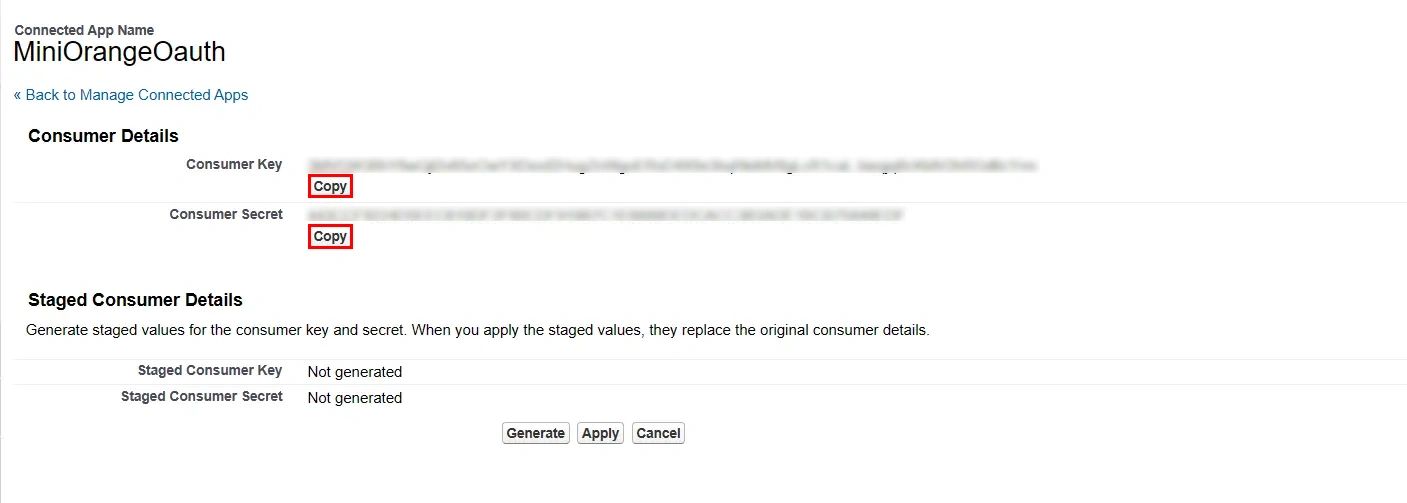
| Client ID | Consumer key from step 2 |
| Client Secret | Consumer secret from step 2 | Scope | email profile openid |

Our Other Identity & Access Management Products